Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
December 6, 2012 6:03 AM
|
Intercepts SMS messages from bank, defeating two-factor authentication. A new version of the Zeus trojan—a longtime favorite of criminals conducting online financial fraud—has been used in attacks on over 30,000 electronic banking customers in Europe, ===> infecting both their personal computers and smartphones. <=== The sophisticated attack is designed to circumvent banks' use of two-factor authentication for transactions by intercepting messages sent by the bank to victims' mobile phones. Read more, a MUST: http://arstechnica.com/security/2012/12/sophisticated-botnet-steals-more-than-47m-by-infecting-pcs-and-phones/
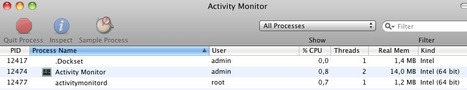
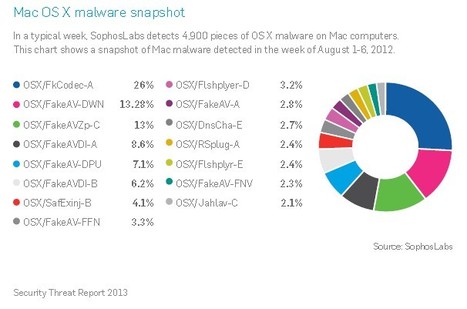
Attackers have expanded their attacks beyond the Windows platform to include Mac OS X and Android. 27 Percent of All Cybercrime Linked to the ‘Blackhole’ Exploit Kit, Sophos said. Even though the overall market share for Mac OS X remains small compared to other platforms, the number of Mac threats are growing as more users switch. Flashback, the malware that reportedly infected hundreds of thousands of Apple systems in April was the largest mass attack this year, but it's not the only Mac malware out there. In a typical week, SophosLabs detects 4,900 pieces of OS X malware on Mac computers. ===> In a snapshot of Mac malware detected over a one-week period in August, SophosLab detected various variants of fake antivirus, codecs and Flash player. <=== Read more, a MUST: http://www.securityweek.com/sophos-blackhole-will-get-more-complex-android-and-mac-os-are-prime-attack-targets

|
Scooped by
Gust MEES
December 4, 2012 11:27 AM
|
Read about the latest cyber security trends in the Sophos Security Threat Report 2013. Most malware developers have found it more profitable to attack Windows than to learn new skills needed to target the smaller OS X user community. ===> But Macs are finding a new home in thousands of businesses and government agencies, and malware authors are paying attention. <===
Forrester Research analyst Frank Gillette recently reported that “almost half of enterprises (1,000 employees or more) are issuing Macs to at least some employees—and they plan a 52% increase in the number of Macs they issue in 2012.”
===> Even more Macs are arriving unofficially through bring your own device arrangements, where they are often an executive’s device of choice for accessing web or cloud applications. <=== ===> Growing Mac usage means many IT organizations must objectively assess, mitigate, and anticipate Mac-related malware threats for the first time. And the risks are clearly increasing! <=== ============================================= Gust MEES Check also my Curation about it: - http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
=============================================
Read more, a MUST: http://www.sophos.com/en-us/medialibrary/PDFs/other/sophossecuritythreatreport2013.pdf?id=ee65b697-1d30-4971-b240-ce96b5e529aa&amp;amp;dl=true

|
Scooped by
Gust MEES
December 4, 2012 8:26 AM
|
Mac malware has been found on a website related to the Dalai Lama, capable of allowing hackers to steal files and spy on keystrokes. If your Mac is infected by OSX/Bckdr-RNW, remote hackers will be able to steal information from your computer and capture any keypresses you make. The attack was presumably designed to infect computers visiting the Dalai Lama-related website, which - one would imagine - would belong to sympathisers with the exiled Tibetan government. ===> Running a Mac without anti-virus software is a little like running naked through a field of thistles. Sooner or later, something bad is going to happen. <=== Read more, a MUST: http://nakedsecurity.sophos.com/2012/12/03/dockster-mac-malware-dalai-lama/

|
Scooped by
Gust MEES
November 30, 2012 2:38 PM
|
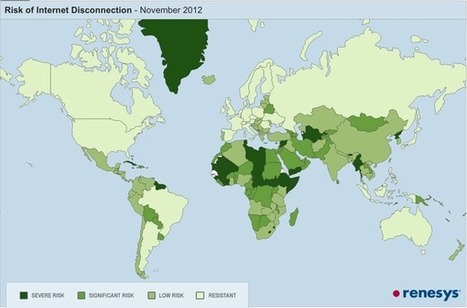
The key to the Internet's survival is the Internet's decentralization — and it's not uniform across the world. In some countries, international access to data and telecommunications services is heavily regulated. There may be only one or two companies who hold official licenses to carry voice and Internet traffic to and from the outside world, and they are required by law to mediate access for everyone else. Under those circumstances, it's almost trivial for a government to issue an order that would take down the Internet. Make a few phone calls, or turn off power in a couple of central facilities, and you've (legally) disconnected the domestic Internet from the global Internet. Of course, this level of centralization also makes it much harder for the government to defend the nation's Internet infrastructure against a determined opponent, who knows they can do a lot of damage by hitting just a few targets. With good reason, most countries have gradually moved towards more diversity in their Internet infrastructure over the last decade. Sometimes that happens all by itself, as a side effect of economic growth and market forces, as many different companies move into the market and compete to provide the cheapest international Internet access to the citizenry. Read more, a MUST: http://www.renesys.com/blog/2012/11/could-it-happen-in-your-countr.shtml

|
Scooped by
Gust MEES
November 28, 2012 9:11 AM
|
According to a survey commissioned by Public Interest Registry (PIR) – the not-for-profit operator of the .ORG domain – to better assess Americans' basic understanding of Internet and network attacks, ===> 85 percent of Americans are uninformed or ill-equipped to deal with a DDoS attack. <=== Moreover, only 17 percent could correctly identify what the acronym DDoS stood for with 77 percent admitting that they had no idea. Read more: http://www.net-security.org/secworld.php?id=14025&utm_source=dlvr.it&utm_medium=twitter

|
Scooped by
Gust MEES
November 27, 2012 4:20 PM
|
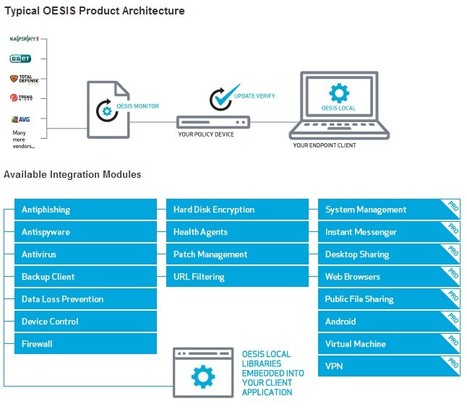
Integrating OESIS Framework enables solutions such as SSL VPN, NAC and others to detect, classify and manage thousands of third party applications. Use OESIS for powerful software manageability. - OESIS Framework is a cross platform, open development framework which enables software engineers and technology vendors to develop products that detect, classify and manage thousands of third-party software applications. OESIS Framework is perfect for SSL VPN, network access control (NAC), support tools and other solutions requiring software manageability. - OESIS Framework consists of software development libraries, source code, and XML files. It provides 4 major components for software manageability: - OESIS Local - libraries that may be embedded in your client to enable the detection, classification and management of endpoint applications
- OESIS Monitor - a data service that monitors and reports application and definition updates
Update Verify - a utility that compares definition data from OESIS Local and OESIS Monitor to ensure that the latest available updates are present on the endpoint
- AppDocs - a toolkit that graphically instructs end-users on how to properly configure endpoint applications
See the capabilities of OESIS in action by trying out OPSWAT's free Security Score tool!
- http://www.opswat.com/products/security-score Read more, very interesting...: http://www.opswat.com/products/oesis-framework

|
Scooped by
Gust MEES
November 27, 2012 9:34 AM
|
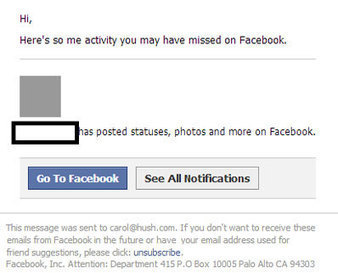
Due to the huge popularity of Facebook and its one billion active users, bogus emails impersonating the social network are constantly hitting users' inboxes. The latest of these is a notification alert about "activity you may have missed on Facebook": Read more, a MUST: http://www.net-security.org/malware_news.php?id=2333

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
November 25, 2012 12:36 AM
|

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
November 24, 2012 9:51 AM
|

|
Scooped by
Gust MEES
November 23, 2012 1:45 PM
|

|
Scooped by
Gust MEES
November 23, 2012 11:23 AM
|
|

|
Scooped by
Gust MEES
December 5, 2012 9:21 AM
|
This is Kaspersky Lab’s annual threat analysis report covering the major issues faced by corporate and individual users alike as a result of malware, potentially harmful programs, crimeware, spam, phishing and other different types of hacker activity. The report has been prepared by the Global Research & Analysis Team (GReAT) in conjunction with Kaspersky Lab’s Content & Cloud Technology Research and Anti-Malware Research divisions. Read more, a MUST: http://www.securelist.com/en/analysis/204792254/Kaspersky_Security_Bulletin_2012_Malware_Evolution

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
December 4, 2012 12:45 PM
|

|
Scooped by
Gust MEES
December 4, 2012 8:34 AM
|
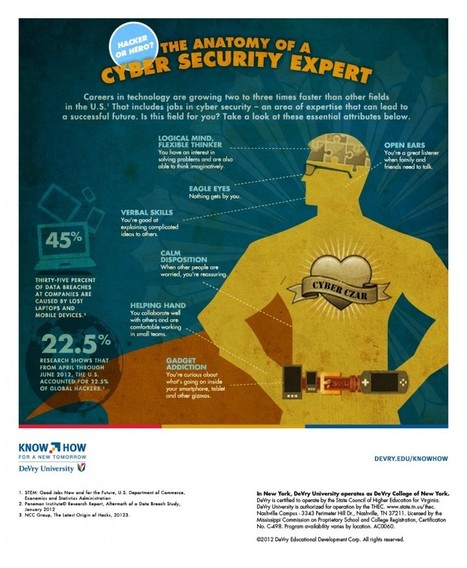
Infographic: Anatomy of a Cyber Security Expert

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
December 3, 2012 4:13 PM
|
A sample of a new Mac spyware called OSX/Dockster.A was found today on Virus Total. This trojan is currently considered low risk as it is not known to have infected users. It has backdoor functiona...

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
November 30, 2012 8:08 AM
|

|
Scooped by
Gust MEES
November 28, 2012 7:55 AM
|

|
Scooped by
Gust MEES
November 27, 2012 9:54 AM
|
Jeremy Hammond is denied bail, placed on terrorist watch list... Either way, a potential sentence of 30 years to life for alleged hacking crimes is probably enough to get the attention of most 27-year-olds. And that is what U.S. District Judge Loretta Preska told Hammond last week that he could face if he is convicted on all counts. Hammond, much better known in the world of hactivism by various online aliases including "Anarchaos," "sup_g," "burn," "yohoho," "POW," "tylerknowsthis," and "crediblethreat," has been held without bail since his arrest in March on charges connected with last year's hacking of Strategic Forecasting, or Stratfor, an Austin, Texas-based international intelligence broker, by AntiSec, an offshoot of LulzSec, which is in turn an offshoot of the hacktivist collective Anonymous. Read more: http://www.csoonline.com/article/722380/lulzsec-hacker-faces-30-years-to-life

|
Scooped by
Gust MEES
November 27, 2012 9:12 AM
|

|
Scooped by
Gust MEES
November 24, 2012 4:33 PM
|
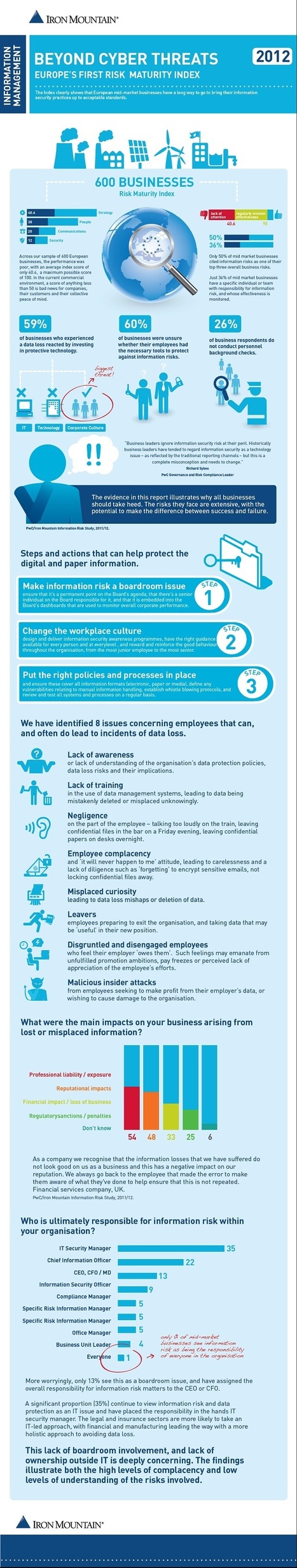
Infographic of the week: Why ignoring information security is lethal
Via Frederic GOUTH

|
Scooped by
Gust MEES
November 23, 2012 12:29 PM
|
A Georgian security researcher is due to present details of an unpatched vulnerability in Google's Chrome browser at the Malcon security conference in India over the weekend. Years ago the circumstances of Ucha Gobejishvili's presentation would hardly have raised an eyebrow but that was before Google began offering up to $60,000 in bug bounties for the low-down on most serious, remotely exploitable bugs in its Chrome web browser software. Gobejishvili has apparently forgone potential financial rewards by leaving Google in the dark before unwrapping a remotely exploitable hole in the Chrome web browser, which reportedly involves a critical vulnerability in a Chrome DLL. More details are due to emerge at a presentation by Gobejishvili at the International Malware Conference (MalCon) in New Delhi on Saturday (24 November). Read more: http://www.theregister.co.uk/2012/11/23/mystery_chrome_0_day/
|



 Your new post is loading...
Your new post is loading...







![Why You Should Care About Mobile Security [Infographic] | ICT Security-Sécurité PC et Internet | Scoop.it](https://img.scoop.it/eCYKbrsHLFNXs4GayRTQ8zl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)