For a very long time, Apple and its pseudo-religious user-base prided itself on being a platform free of malware; those days are inarguably and unequivocally over. Its emergence as the early winner...
Get Started for FREE
Sign up with Facebook Sign up with X
I don't have a Facebook or a X account

 Your new post is loading... Your new post is loading...
 Your new post is loading... Your new post is loading...
Apple recently addressed a macOS vulnerability that allows attackers to bypass System Integrity Protection (SIP) and install malicious kernel drivers by loading third-party kernel extensions.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Apple recently addressed a macOS vulnerability that allows attackers to bypass System Integrity Protection (SIP) and install malicious kernel drivers by loading third-party kernel extensions.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Apple rushes out out major macOS and iOS security updates to cover a pair of vulnerabilities already being exploited in the wild.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Apple rushes out out major macOS and iOS security updates to cover a pair of vulnerabilities already being exploited in the wild.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Unauthorized data access vulnerability in macOS is detailed by Microsoft
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Unauthorized data access vulnerability in macOS is detailed by Microsoft
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Des failles de sécurité critiques ont été découvertes au sein d’un outil open source impliqué dans la création de millions d’apps iOS et macOS. Ces vulnérabilités, restées inconnues pendant près de dix ans, permettent de voler des données sensibles, comme des numéros de cartes de crédit.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Des failles de sécurité critiques ont été découvertes au sein d’un outil open source impliqué dans la création de millions d’apps iOS et macOS. Ces vulnérabilités, restées inconnues pendant près de dix ans, permettent de voler des données sensibles, comme des numéros de cartes de crédit.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Nutzer von Apple-Computern sind derzeit im Visier von Cyber-Kriminellen. Wie "Malwarebytes" berichtet, läuft aktuell eine Kampagne unter dem Namen ClearFake. Dabei soll Schadsoftware auf den Rechnern der Opfer installiert werden.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Nutzer von Apple-Computern sind derzeit im Visier von Cyber-Kriminellen. Wie "Malwarebytes" berichtet, läuft aktuell eine Kampagne unter dem Namen ClearFake. Dabei soll Schadsoftware auf den Rechnern der Opfer installiert werden.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Citizen Lab says two zero-days fixed by Apple today in emergency security updates were actively abused as part of a zero-click exploit chain (dubbed BLASTPASS) to deploy NSO Group's Pegasus commercial spyware onto fully patched iPhones.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Blastpass
Gust MEES's insight:
Citizen Lab says two zero-days fixed by Apple today in emergency security updates were actively abused as part of a zero-click exploit chain (dubbed BLASTPASS) to deploy NSO Group's Pegasus commercial spyware onto fully patched iPhones.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Blastpass
Apple released security updates for older iPhones to fix a zero-day vulnerability tracked as CVE-2023-41064 that was actively exploited to infect iOS devices with NSO's Pegasus spyware.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Apple released security updates for older iPhones to fix a zero-day vulnerability tracked as CVE-2023-41064 that was actively exploited to infect iOS devices with NSO's Pegasus spyware.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Der Sicherheitsforscher Patrick Wardle machte auf der Defcon-Hackerkonferenz in Las Vegas auf mehrere Schwachstellen im Background-Task-Management (BTM) von macOS aufmerksam. Wie aus einem Bericht von Wired hervorgeht, soll es Angreifern damit möglich sein, Apples Warnsystem zu umgehen und so eine persistente Schadsoftware auf einem Mac zu installieren, ohne dass der Benutzer dies mitbekommt.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Der Sicherheitsforscher Patrick Wardle machte auf der Defcon-Hackerkonferenz in Las Vegas auf mehrere Schwachstellen im Background-Task-Management (BTM) von macOS aufmerksam. Wie aus einem Bericht von Wired hervorgeht, soll es Angreifern damit möglich sein, Apples Warnsystem zu umgehen und so eine persistente Schadsoftware auf einem Mac zu installieren, ohne dass der Benutzer dies mitbekommt.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Microsoft hat eine kritische Sicherheitslücke im macOS entdeckt, die Hackern leichten Zugang zu den wichtigsten Daten Ihres Macs ermöglichen könnte. Die als "Migraine" bezeichnete Sicherheitslücke zeigt, warum es äußerst wichtig ist, Ihren Mac so schnell wie möglich zu aktualisieren.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Microsoft hat eine kritische Sicherheitslücke im macOS entdeckt, die Hackern leichten Zugang zu den wichtigsten Daten Ihres Macs ermöglichen könnte. Die als "Migraine" bezeichnete Sicherheitslücke zeigt, warum es äußerst wichtig ist, Ihren Mac so schnell wie möglich zu aktualisieren.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
This is new. For the very first time, Apple has released a Rapid Security Response (RSR) update to iPhone users, with a corresponding RSR for the Mac. It represents a change in how Apple will launch smaller updates—as indicated by the number of this one. After iOS 16.4.1, you might legitimately have expected iOS 16.4.2 as the small update before iOS 16.5 lands.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
This is new. For the very first time, Apple has released a Rapid Security Response (RSR) update to iPhone users, with a corresponding RSR for the Mac. It represents a change in how Apple will launch smaller updates—as indicated by the number of this one. After iOS 16.4.1, you might legitimately have expected iOS 16.4.2 as the small update before iOS 16.5 lands.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Über manipulierte Kalendereinträge konnten Angreifer inzwischen mehrmals Spionagesoftware auf die iPhones ihrer Opfer laden. Wie Sicherheitsexperten von Microsoft und Citizen Lab herausgefunden haben, handelt es sich dabei um einen sogenannten Zero-Click-Exploit. Die Malware wird dabei installiert, ohne dass das Opfer auf einen Link klicken oder Rechte freigeben muss.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Über manipulierte Kalendereinträge konnten Angreifer inzwischen mehrmals Spionagesoftware auf die iPhones ihrer Opfer laden. Wie Sicherheitsexperten von Microsoft und Citizen Lab herausgefunden haben, handelt es sich dabei um einen sogenannten Zero-Click-Exploit. Die Malware wird dabei installiert, ohne dass das Opfer auf einen Link klicken oder Rechte freigeben muss.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
MacStealer: Mac-Malware will Passwörter und Krypto-Wallets klauen
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=MacStealer
Gust MEES's insight:
MacStealer: Mac-Malware will Passwörter und Krypto-Wallets klauen
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=MacStealer
|
From
www
Un simple site piégé permet de pirater 270 millions d’iPhone en quelques minutes. Un redoutable outil de piratage a été impliqué dans plusieurs cyberattaques menées par des hackers russes au cours des derniers mois. Il peut voler vos photos, vos messages, vos mots de passe ou vos portefeuilles crypto, puis disparaître sans laisser presque aucune trace. Le kit cible les iPhone qui n’ont pas été mis à jour.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Un simple site piégé permet de pirater 270 millions d’iPhone en quelques minutes. Un redoutable outil de piratage a été impliqué dans plusieurs cyberattaques menées par des hackers russes au cours des derniers mois. Il peut voler vos photos, vos messages, vos mots de passe ou vos portefeuilles crypto, puis disparaître sans laisser presque aucune trace. Le kit cible les iPhone qui n’ont pas été mis à jour.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Apple schiebt iOS 18.1.1, macOS 15.1.1 und visionOS 2.1.1 nach, um aktiv ausgenutzte Exploits zu stoppen. Nutzer sollten am besten schnell aktualisieren.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Apple schiebt iOS 18.1.1, macOS 15.1.1 und visionOS 2.1.1 nach, um aktiv ausgenutzte Exploits zu stoppen. Nutzer sollten am besten schnell aktualisieren.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Microsoft: macOS Vulnerability Potentially Exploited in Adware Attacks
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Microsoft: macOS Vulnerability Potentially Exploited in Adware Attacks
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Eine Sicherheitslücke in iOS und iPadOS ermöglichte es VoiceOver, Passwörter laut vorzulesen. Apple hat reagiert und mit einem Update das Problem behoben.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Eine Sicherheitslücke in iOS und iPadOS ermöglichte es VoiceOver, Passwörter laut vorzulesen. Apple hat reagiert und mit einem Update das Problem behoben.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
The myth that your Mac is safe from computer viruses may have originated from Apple's commercials in 2006, but it's simply not true.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
The myth that your Mac is safe from computer viruses may have originated from Apple's commercials in 2006, but it's simply not true.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Apple released emergency security updates to fix two new zero-day vulnerabilities exploited in attacks targeting iPhone and Mac users, for a total of 13 exploited zero-days patched since the start of the year.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Apple released emergency security updates to fix two new zero-day vulnerabilities exploited in attacks targeting iPhone and Mac users, for a total of 13 exploited zero-days patched since the start of the year.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
A new information stealer malware named 'MetaStealer' has appeared in the wild, stealing a wide variety of sensitive information from Intel-based macOS computers.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
A new information stealer malware named 'MetaStealer' has appeared in the wild, stealing a wide variety of sensitive information from Intel-based macOS computers.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
A security researcher caused something of a kerfuffle during the Def Con 2023 hacking conference in Las Vegas last month. Some attendees with iPhones were shocked to see an Apple pop-up notification asking them to connect to a nearby Apple TV device using their Apple ID credentials. Not least, as some of the hackers on the receiving end of these Bluetooth-powered prompts were running with Bluetooth disabled. Or so they thought. Now, another security researcher has demonstrated a similar hack that uses a readily available hacking device to spam nearby iPhones with pop-up notifications and effectively execute a denial of service attack.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
A security researcher caused something of a kerfuffle during the Def Con 2023 hacking conference in Las Vegas last month. Some attendees with iPhones were shocked to see an Apple pop-up notification asking them to connect to a nearby Apple TV device using their Apple ID credentials. Not least, as some of the hackers on the receiving end of these Bluetooth-powered prompts were running with Bluetooth disabled. Or so they thought. Now, another security researcher has demonstrated a similar hack that uses a readily available hacking device to spam nearby iPhones with pop-up notifications and effectively execute a denial of service attack.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Utilisateurs d’un iPhone, d’une tablette ou d’un ordinateur Mac, à vos mises à jour ! Le fabricant Apple vient de publier des correctifs pour ces différents produits, à la suite de la découverte d’une faille (CVE-2023-37450) dans le moteur de navigation WebKit par un chercheur en sécurité anonyme.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Utilisateurs d’un iPhone, d’une tablette ou d’un ordinateur Mac, à vos mises à jour ! Le fabricant Apple vient de publier des correctifs pour ces différents produits, à la suite de la découverte d’une faille (CVE-2023-37450) dans le moteur de navigation WebKit par un chercheur en sécurité anonyme.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
The "rapid" security fixes are designed to quickly patch security flaws under active exploitation by hackers.
Apple on Monday released its first batch of publicly available “rapid security” patches, aimed at quickly fixing security vulnerabilities that are under active exploitation or pose significant risks to its customers.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
The "rapid" security fixes are designed to quickly patch security flaws under active exploitation by hackers.
Apple on Monday released its first batch of publicly available “rapid security” patches, aimed at quickly fixing security vulnerabilities that are under active exploitation or pose significant risks to its customers.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Last week, we warned about the appearance of two critical zero-day bugs that were patched in the very latest versions of macOS (version 13, also known as Ventura), iOS (version 16), and iPadOS (version 16).
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Last week, we warned about the appearance of two critical zero-day bugs that were patched in the very latest versions of macOS (version 13, also known as Ventura), iOS (version 16), and iPadOS (version 16).
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Apple’s latest update blast is out, including an extensive range of security patches for all devices that Apple officially supports.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
Gust MEES's insight:
Apple’s latest update blast is out, including an extensive range of security patches for all devices that Apple officially supports.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
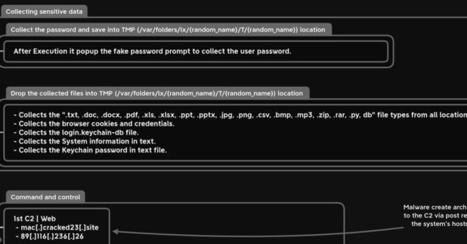
A new information-stealing malware has set its sights on Apple's macOS operating system to siphon sensitive information from compromised devices.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=MacStealer
Gust MEES's insight:
A new information-stealing malware has set its sights on Apple's macOS operating system to siphon sensitive information from compromised devices.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=MacStealer
|




































https://achetersaxendaenligne.com/Produit/acheter-belviq-en-ligne/
https://acheteractiskenan.com/
https://acheteractiskenan.com/produit/
https://acheteractiskenan.com/produit/achete-klonopin/
https://acheteractiskenan.com/produit/acheter-4-aco-dmt/
https://acheteractiskenan.com/product/acheter-5-meo-dmt-usa/
https://acheteractiskenan.com/product/acheter-dmt/
https://acheteractiskenan.com/product/acheter-adderall-en-ligne/
https://acheteractiskenan.com/product/acheter-adipex/
https://acheteractiskenan.com/product/acheter-toseina-2-ml-solucion/
https://acheteractiskenan.com/product/acheter-oxycodone-mallinckrodt/
https://acheteractiskenan.com/product/acheter-de-loxycodone/
https://acheteractiskenan.com/product/acheter-ativan-en-ligne/
https://acheteractiskenan.com/product/acheter-percocet/
https://acheteractiskenan.com/product/acheter-tramadol/
https://acheteractiskenan.com/product/morphine/
https://acheteractiskenan.com/product/acheter-codeine-en-ligne/
https://acheteractiskenan.com/product/injection-de-morphine/
https://acheteractiskenan.com/product/acheter-phentermine-en-ligne/
https://acheteractiskenan.com/product/acheter-tren-a-en-ligne/
https://acheteractiskenan.com/product/achetez-trenbolone-enanthate/
https://acheteractiskenan.com/product/acheter-trenarapid-en-ligne/
https://acheteractiskenan.com/product/acheter-de-la-cocaine/
https://acheteractiskenan.com/product/acheter-demerol/
https://acheteractiskenan.com/product/acheter-desoxyn/
https://acheteractiskenan.com/product/buy-dexedrine-online/
https://acheteractiskenan.com/product/acheter-dilaudid-en-ligne/
https://acheteractiskenan.com/product/acheter-du-fentanyl/
https://acheteractiskenan.com/product/acheter-du-suboxone/
https://acheteractiskenan.com/product/acheter-du-xanax-vert/
https://acheteractiskenan.com/product/acheter-norvas-10mg/
https://acheteractiskenan.com/product/acheter-oramorph/
https://acheteractiskenan.com/product/acheter-rubifen/
https://acheteractiskenan.com/product/acheter-subutex/
https://acheteractiskenan.com/product/acheter-vicodin/
https://acheteractiskenan.com/product/achetez-vyvanse/
https://acheteractiskenan.com/product/acheter-de-la-cocaine/
https://acheteractiskenan.com/product/acheter-de-lheroine/
https://acheteractiskenan.com/product/acheter-methadone-en-ligne/
https://acheteractiskenan.com/product/acheter-ms-contin/
https://acheteractiskenan.com/product/acheter-oxazepam-en-ligne/
https://acheteractiskenan.com/product/acheter-oxynorm-en-ligne/
https://acheteractiskenan.com/product/acheter-phentermine-en-ligne/
https://acheteractiskenan.com/product/acheter-plegine-en-ligne/
https://acheteractiskenan.com/product/acheter-rubifen/
https://acheteractiskenan.com/product/acheter-stilpane-sirop-100ml/
https://acheteractiskenan.com/product/acheter-toseina-2-ml-solucion/
https://acheteractiskenan.com/product/acheter-histaverin-2-mg-ml/
https://acheteractiskenan.com/product/acheter-lheroine-black-goudron/
https://acheteractiskenan.com/product/acheter-la-cocaine-colombienne/
https://acheteractiskenan.com/product/acheter-ultram-en-ligne/
https://acheteractiskenan.com/product/acheter-oxecta-oxycodone-hcl-...
acheter percocet
acheter tramadol
acheter morphine
acheter codeine en lign
injection de morphine
acheter phentermine en ligne
achetez trenbolone enanthate
acheter trenarapid
kopen nembutal liquid
kopen oxycodon hcl
https://kopenoxycodone.com/
https://kopenoxycodone.com/producten/
https://kopenoxycodone.com/product/ambien-online-kopen/
https://kopenoxycodone.com/product/buprenorfine-kopen/
https://kopenoxycodone.com/product/carisoprodol-nederland-kopen/
https://kopenoxycodone.com/product/fentanyl-citrate-kopen/
https://kopenoxycodone.com/product/fentanyl-poeder-kopen/
https://kopenoxycodone.com/product/fentanyl-pleister-kopen/
https://kopenoxycodone.com/product/gouden-leraar-paddenstoelen/
https://kopenoxycodone.com/product/hydromorphone-kopen/
https://kopenoxycodone.com/product/ketamine-poeder-kopen/
https://kopenoxycodone.com/product/koop-5-meo-dmt/
https://kopenoxycodone.com/product/koop-adderall-online/
https://kopenoxycodone.com/product/koop-desoxyn-online/
https://kopenoxycodone.com/product/koop-dexedrine/
https://kopenoxycodone.com/product/koop-dmt-netherland/
https://kopenoxycodone.com/product/koop-flakka-a-pvp/
https://kopenoxycodone.com/product/koop-mdma-crystal/
https://kopenoxycodone.com/product/koop-morphine/
https://kopenoxycodone.com/product/koop-natriumcyanide/
https://kopenoxycodone.com/product/koop-nembutal-pentobarbital/
https://kopenoxycodone.com/product/koop-nembutal-poeder/
https://kopenoxycodone.com/product/koop-oxycodon/
https://kopenoxycodone.com/product/koop-oxycontin-online/
https://kopenoxycodone.com/product/koop-percocet-online/
https://kopenoxycodone.com/product/koop-phentermine-adipex/
https://kopenoxycodone.com/product/koop-suboxone-strips/
https://kopenoxycodone.com/product/koop-subutex-nederlands/
https://kopenoxycodone.com/product/koop-vicodin-online/
https://kopenoxycodone.com/product/koop-vyvanse-online/
https://kopenoxycodone.com/product/kopen-ultram-online/
https://kopenoxycodone.com/product/lsd-sheet/
https://kopenoxycodone.com/product/nembutal-pillen-kopen/
https://kopenoxycodone.com/product/koop-nembutal-liquid/
https://kopenoxycodone.com/product/oxycodon-hcl-kopen/
comprar-ultram
comprar xanax verde
buy xanax
comprar vyvanse en linea
comprar vicodin en linea
golden teacher
comprar psilocybe
comprar polvo-
comprar micro mushrooms
comprar metanfetaminas
comprar flakka
comprar fentanilo en linea
comprar extasis en linea
comprar-etizolam
comprar-5-meo-dmt
buy-seconal-sodium
buy-nembutal-pills
buy-nembutal-liquid
Oxycodone
comprar Oxycodone
https://comprarmorfina.com/
https://comprarmorfina.com/productos-comprar-dilaudid/
https://comprarmorfina.com/product/comprar-adderall-en-linea/
https://comprarmorfina.com/product/comprar-adipex-en-linea/
https://comprarmorfina.com/product/comprar-ambien-en-linea/
https://comprarmorfina.com/product/comprar-buprenorfine-en-linea/
https://comprarmorfina.com/product/comprar-dexedrina/
https://comprarmorfina.com/product/comprar-desoxyn-en-linea/
https://comprarmorfina.com/product/comprar-dilaudid/
https://comprarmorfina.com/product/comprar-dmt-en-linea/
https://comprarmorfina.com/product/comprar-heroina-en-linea/
https://comprarmorfina.com/product/comprar-ketamina/
https://comprarmorfina.com/product/comprar-klonopin/
https://comprarmorfina.com/product/comprar-morfina/
https://comprarmorfina.com/product/comprar-oxicodona-en-linea/
https://comprarmorfina.com/product/comprar-oxycontin-en-linea/
https://comprarmorfina.com/product/comprar-percocet-en-linea/
https://comprarmorfina.com/product/comprar-rubifen-espana/
https://comprarmorfina.com/product/comprar-soma-en-linea/
https://comprarmorfina.com/product/comprar-suboxone-en-linea/
https://comprarmorfina.com/product/comprar-subutex-en-linea/
https://comprarmorfina.com/product/comprar-ultram-en-linea/
https://comprarmorfina.com/product/comprar-xanax-verde/
https://comprarmorfina.com/product/buy-xanax/
https://comprarmorfina.com/product/comprar-vyvanse-en-linea/
https://comprarmorfina.com/product/comprar-vicodin-en-linea/
https://comprarmorfina.com/product/golden-teacher-crecer-rapidamente/https://onlinevapesshop.com/
https://onlinevapesshop.com/product/
https://onlinevapesshop.com/product/buy-phentermine-online/
https://onlinevapesshop.com/product/buy-adipex-online/
https://onlinevapesshop.com/product/buy-oxynorm-online/
https://onlinevapesshop.com/product/buy-oxycontin-online/
https://onlinevapesshop.com/product/buy-adderall-online-3/
https://onlinevapesshop.com/product/buy-adderall-online-2/
https://onlinevapesshop.com/product/buy-celexa-online/
https://onlinevapesshop.com/product/buy-concerta-online/
https://onlinevapesshop.com/product/buy-desoxyn-5mg-online/
https://onlinevapesshop.com/product/buy-dexedrine-online/
https://onlinevapesshop.com/product/buy-klonopin-online/
https://onlinevapesshop.com/product/buy-mescaline-online/
https://onlinevapesshop.com/product/buy-valium-online/
https://onlinevapesshop.com/product/buy-xanax-online/
https://onlinevapesshop.com/product/buy-yellow-xanax-bars-online/
https://onlinevapesshop.com/product/buy-zopiclone-online/
https://onlinevapesshop.com/product/buy-botox-online/
https://onlinevapesshop.com/product/buy-cbd-oil-online/
https://onlinevapesshop.com/product/buy-diclazepam-online/
https://onlinevapesshop.com/product/buy-liquid-red-mercury-online/
https://onlinevapesshop.com/product/buy-mdma-crystal-online/
https://onlinevapesshop.com/product/buy-phenylacetone-oil-online/
https://onlinevapesshop.com/product/buy-nembutal-pentobarbital-liqu...
https://onlinevapesshop.com/product/buy-piperonyl-methyl-ketone/
https://onlinevapesshop.com/product/buy-anavar-oxandrolone-online/
https://onlinevapesshop.com/product/buy-ssd-chemical-solution/
https://onlinevapesshop.com/product/buy-ayurvedic-urea-online/
https://onlinevapesshop.com/product/buy-dxn-code-strike-online/
https://onlinevapesshop.com/product/buy-deca-durabolin-online/
https://onlinevapesshop.com/product/buy-viagra-online/
https://onlinevapesshop.com/product/buy-genius-test-online/
https://onlinevapesshop.com/product/buy-viagra-online/
https://onlinevapesshop.com/product-category/growth-hormones/
https://onlinevapesshop.com/product/buy-viagra-online/
https://onlinevapesshop.com/product/buy-ketamine-liquid-online/
https://onlinevapesshop.com/product/buy-ketamine-powder-online/
https://onlinevapesshop.com/product/buy-methoxetamine-online/
https://onlinevapesshop.com/product/buy-methylone-crystals-online/
https://onlinevapesshop.com/product/buy-morphine-online-2/
https://onlinevapesshop.com/product/buy-oramorph-online/
https://onlinevapesshop.com/product/buy-percocet-online/
https://onlinevapesshop.com/product/buy-roxicodone-online/
https://onlinevapesshop.com/product/buy-soma-online/
https://onlinevapesshop.com/product/buy-tramadol-online/
https://onlinevapesshop.com/product/buy-vicodin-online/
Buy oxycodone online
Buy phentermine online
Buy adipex online
Buy oxynorm online
Buy oxycontin online
Buy adderall USA online
Buy adderall online
Buy oxycodone online
Buy 4-aco-dmt online
Buy 5-meo-dmt online
Buy adipex online
Buy ambien online
Buy oxycodone
buy oxycontin
buy percocet
buy oramorph
Buy oxycodone online
buy-nembutal liquid
https://dolorendo.com/
https://dolorendo.com/product/
https://dolorendo.com/product/comprar-oxicodona-en-linea/
https://dolorendo.com/product/comprar-oxicodon/
https://dolorendo.com/product/comprar-oxynorm-en-linea/
https://dolorendo.com/product/comprar-oxycontin-en-linea/
https://dolorendo.com/product/comprar-percocet-en-linea/
https://dolorendo.com/product/comprar-oramorph-sr/
https://dolorendo.com/productos-comprar-dilaudid/
https://dolorendo.com/product/comprar-vyvanse-en-linea/
https://dolorendo.com/product/comprar-suboxone-en-linea/
https://dolorendo.com/product/comprar-subutex-en-linea/
https://dolorendo.com/product/comprar-pastillas-nembutal/
https://dolorendo.com/productos-comprar-dilaudid/
https://dolorendo.com/product/comprar-acetaminofen-codeina/
https://dolorendo.com/product/comprar-adderall-en-linea/
https://dolorendo.com/product/comprar-desoxyn-en-linea/
https://dolorendo.com/product/comprar-dexedrina/
https://dolorendo.com/product/comprar-dmt-en-linea/
https://dolorendo.com/product/comprar-ketamina/
https://dolorendo.com/product/comprar-klonopin/
https://dolorendo.com/product/comprar-5-meo-dmt/
https://dolorendo.com/product/comprar-adipex-en-linea/
https://dolorendo.com/product/comprar-alphabol-cr/
https://buypsychedelicsnow.com/shop/buy-morphine-canada/
https://buypsychedelicsnow.com/shop/buy-5-meo-dmt-usa/
https://buypsychedelicsnow.com/shop/buy-codeine-online/
https://buypsychedelicsnow.com/shop/buy-4-aco-dmt-online/
https://buypsychedelicsnow.com/shop/buy-ayahuasca-online-usa/
https://buypsychedelicsnow.com/shop/black-tar-heroin/
https://buypsychedelicsnow.com/shop/buy-bolivian-cocaine/
https://buypsychedelicsnow.com/shop/buy-brown-heroin-usa/
https://buypsychedelicsnow.com/shop/buy-changa-online/
https://buypsychedelicsnow.com/shop/buy-white-heroin-online/
https://buypsychedelicsnow.com/shop/buy-dmt-online-canada/
https://buypsychedelicsnow.com/shop/buy-flakka-online/
https://buypsychedelicsnow.com/shop/buy-psilocybe-cubensis-online/
https://buypsychedelicsnow.com/shop/buy-ibogaine-online-canada/
https://buypsychedelicsnow.com/shop/ketamine-powder-for-sale/
https://buypsychedelicsnow.com/shop/buy-kratom-online-canada/
https://buypsychedelicsnow.com/shop/buy-lsd-online-canada/
https://buypsychedelicsnow.com/shop/mdma-for-sale-canada/
https://buypsychedelicsnow.com/shop/buy-mescaline-online-canada/
https://buypsychedelicsnow.com/shop/buy-mushroom-online-canada/
https://buypsychedelicsnow.com/shop/buy-psilocybin-online-canada/
https://achetersaxendaenligne.com/
https://achetersaxendaenligne.com/Produit/acheter-saxenda-en-ligne/
https://achetersaxendaenligne.com/
https://achetersaxendaenligne.com/Produit/acheter-saxenda-en-ligne/
https://achetersaxendaenligne.com/Produit/acheter-adipex-en-ligne/
https://achetersaxendaenligne.com/Produit/acheter-belviq-en-ligne/
https://achetersaxendaenligne.com/Produit/acheter-dexedrine/
https://achetersaxendaenligne.com/Produit/acheter-du-ritalin/https://achetersaxendaenligne.com/Produit/ozempic-sans-ordonnance/
https://achetersaxendaenligne.com/Produit/acheter-victoza-en-ligne/https://achetersaxendaenligne.com/Produit/acheter-vyvanse/
https://achetersaxendaenligne.com/Produit/achetez-qsymia-en-ligne/
WhatsApp: +380 96 386 6267 ) TOP QUALITY COUNTERFEIT MONEY FOR
SALE. DOLLAR, POUNDS, EUROS AND OTHER CURRENCIES AVAILABLE.
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
WhatsApp: +380 96 386 6267 ) GET 100% UNDETECTABLE BANK NOTES AND
QUALITY DOCUMENTS.https://banksnote.com
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
FOR MORE INFORMATION'S, CONTACT US BELOW>>>>>
VISIT OUR WEBSITE AT: https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
Whats-app Number:: +380 96 386 6267
Whats-app Number:: +380 96 386 6267
Email: globalcurrency22@gmail.com
HIGH QUALITY UNDETECTABLE COUNTERFEIT MONEY FOR SALE IN ALL
CURRENCIES. WHATSAPP us +38096386 6267
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
We use latest technology to produce our notes so that it looks 100%
https://banksnote.com
identical to the real note. This thus implies all security features
present in the real notes are present in the note we make. Our team is
made up of Quality IT technicians from Morocco, US, Russia, India,
https://banksnote.com
Korea and China etc We offer high quality counterfeit NOTES for all
currencies.
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
FOR MORE INFORMATION'S, CONTACT US BELOW>>>>>
VISIT OUR WEBSITE AT: https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
Whats-app Number:: +380 96 386 6267
Whats-app Number:: +380 96 386 6267
Email: globalcurrency22@gmail.com
Why would you buy from us? https://banksnote.com
Our banknotes contain the following security features that make
it to be genius and we have the best grade counterfeit in the world
both Euro and Dollar and any bills of your choice you want.
Security features of our bank notes below : https://banksnote.com
Intaglio printing
Watermarks
Security thread https://banksnote.com
See-through register
Special foil/special foil elements
Iridescent stripe / shifting colors. https://banksnote.com
OUR WEBSITE BELOW:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
Our banknotes are printed on 80% cotton 20% cellulose paper which
differs substantially from normal paper. By using a special printing
technique, several picture elements on the front of the banknote are
identifiable by touch. The guidelines on detecting counterfeit
currency give a comparison of genuine and falsified security features.
https://banksnote.com
OUR WEBSITE BELOW:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
- Our bills/notes bypass everything, counterfeit pens and
machines.https://banksnote.com
- Can be used in banks but can be used else where same like normal money
- We have the best HOLOGRAMS AND DUPLICATING MACHINES
- UV: YES
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
FOR MORE INFORMATION'S, CONTACT US BELOW>>>>>
VISIT OUR WEBSITE AT: https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
Whats-app Number:: +380 96 386 6267
Whats-app Number:: +380 96 386 6267
Email: globalcurrency22@gmail.com
EUR - Euro : https://banksnote.com
USD - US Dollar: https://banksnote.com
DNR - DINAR: https://banksnote.com
GBP - British Pound: https://banksnote.com
INR - Indian Rupee :https://banksnote.com
AUD - Australian Dollar: https://banksnote.com
CAD - Canadian Dollar: https://banksnote.com
AED - Emirati Dirham: https://banksnote.com
ZAR - Rand: https://banksnote.com
CHF - Swiss Franc:https://banksnote.com
CNY - Chinese Yuan Renminbi: https://banksnote.com
MYR - Malaysian Ringgit: https://banksnote.com
THB - Thai Baht: https://banksnote.com
NZD - New Zealand Dollar: https://banksnote.com
SAR - Saudi Arabian Riyal: https://banksnote.com
QAR - Qatari Riyal: https://banksnote.com
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
FOR MORE INFORMATION'S, CONTACT US BELOW>>>>>
VISIT OUR WEBSITE AT: https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
Whats-app Number:: +380 96 386 6267
Whats-app Number:: +380 96 386 6267
Email: globalcurrency22@gmail.com
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
Tags:
counterfeit cash, counterfeiting
High Quality Undetectable Counterfeit Banknotes For Sale
HIGH QUALITY UNDETECTABLE COUNTERFEIT BANKNOTES FOR SALE
BUY SUPER HIGH QUALITY FAKE MONEY ONLINE GBP, DOLLAR, EUROS
BUY 100% UNDETECTABLE COUNTERFEIT MONEY £,$,€
BEST COUNTERFEIT MONEY ONLINE, DOLLARS, GBP, EURO NOTES AVAILABLE
BUY TOP GRADE COUNTERFEIT MONEY ONLINE, DOLLARS, GBP, EURO NOTES AVAILABLE.
TOP QUALITY COUNTERFEIT MONEY FOR SALE. DOLLAR, POUNDS, EUROS AND
OTHER CURRENCIES AVAILABLE
Counterfeit money for sale
money, banknotes, fake money, prop money,
EUROS,DOLLARS AND POUNDS AND NOVELTY DOCUMENTS LIKE PASSPORTS,ID
CARDS,GREEN CARDS AND DRIVERS LICENSE
counterfeit money for sale, buy fake money online, fake dollars, fake
pounds, fake euro, buy money online, fake money for sale. Buy Fake
Dollars, Buy Fake British Pounds, Buy Fake Euro, Money, where can i
buy counterfeit money?.
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
FOR MORE INFORMATION'S, CONTACT US BELOW>>>>>
VISIT OUR WEBSITE AT: https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
Whats-app Number:: +380 96 386 6267
Whats-app Number:: +380 96 386 6267
Email: globalcurrency22@gmail.com.
VISIT OUR WEBSITE AT:
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com
https://banksnote.com