Your new post is loading... Your new post is loading...
 Your new post is loading... Your new post is loading...
PC Rental Agent was supposed to stem theft. Instead, it sparked a firestorm.
Before 2012, there were only two instances of cyber weapons being used – Stuxnet and Duqu.
However, analysis of these two forced the IT community to dramatically expand the whole concept of what cyber warfare entails. Apart from an increase in the number of security incidents involving cyber weapons, the events of 2012 have also brought to light the fact that many sovereign states are heavily involved in the development of cyber weapons – something that was picked up on and widely discussed by the mass media. Moreover, cyber warfare was on the agenda of public discussions between governments and state representatives over the course of 2012. It is safe to say, therefore, that 2012 has brought key revelations in this sphere – both in terms of the increase in security incidents and a greater understanding of how cyber weapons are being developed
2012 saw some of the biggest malware discoveries in the history of information security. AlienVault has crafted this unique slideshow that proves modern malware never dies, it just morphs and reappears.
WordPress Pingback Vulnerability Can Be Abused for DDOS Attacks
56 suspected members of a major network of payment card fraudsters (38 in Bulgaria, 17 in Italy and 1 in the Netherlands) have been arrested in a coordinated raid across Europe. This major police operation was led by Italy and Bulgaria and was coordinated from the Operational Centre at Europol headquarters in The Hague.
October 23, 2009
"Evil Maid" Attacks on Encrypted Hard Drives Earlier this month, Joanna Rutkowska implemented the "evil maid" attack against TrueCrypt. The same kind of attack should work against any whole-disk encryption, including PGP Disk and BitLocker. Basically, the attack works like this: Step 1: Attacker gains access to your shut-down computer and boots it from a separate volume. The attacker writes a hacked bootloader onto your system, then shuts it down. Step 2: You boot your computer using the attacker's hacked bootloader, entering your encryption key. Once the disk is unlocked, the hacked bootloader does its mischief. It might install malware to capture the key and send it over the Internet somewhere, or store it in some location on the disk to be retrieved later, or whatever.
“Necurs is a prevalent threat in the wild at the moment,” warns Microsoft, with more than 80,000 unique infections detected during November. Necurs is a rootkit delivered by drive-by downloading.
The Trojan in question has DDoS and Bitcoin-mining capabilities, but it's main function is to steal banking credentials.
The botnet operator spreads the malware via the Usenet discussion forum, which is also a popular platform for distributing pirated content. In order to hide its malicious nature, the file "weighs" 15MB, a great part of which is junk data. The rest consists of a ZeuS bot, a Tor client for Windows, the CGMiner bitcoin mining tool, and a copy of a DLL file used by CGMiner for CPU and GPU hash cracking. Read more, a MUST: http://www.net-security.org/malware_news.php?id=2357
Mobile Device Security: What Senior Managers Should Know
This article provides clear, practical guidance on how you can make sure mobile ===> devices are a benefit rather than a risk for your organization. <===
Read more, a MUST:
Kaspersky Lab released its annual Kaspersky Security Bulletin, which provides the overall malware and cyber-threat statistics for 2012.
===> The report revealed significant growth of Mac-specific malware and an explosive growth in the number of threats targeting the Android platform. <===
Overall, Kaspersky Lab detected and blocked more than 1.5 billion web-based attacks in 2012 and more than 3 billion infected files.
At the present time Kaspersky Lab detects and blocks more than 200,000 new malicious programs every day, a significant increase from the first half of 2012, when 125,000 malicious programs were detected and blocked each day on average.
===> Servers located in the United States were the most frequently used to host and deliver malicious objects (25.5% of all incidents). Russia occupies the second place with 19.6% followed by the Netherlands, Germany and the United Kingdom. <===
This is a significant change compared to years past: in 2010 the majority of malware was hosted in China. Changes in domain registration policies and other regulations taken by Chinese authorities resulted in the rapid decline of malicious hosts originating from the country.
Read more, a MUST: http://www.net-security.org/malware_news.php?id=2352
Purveyors of the Gameover trojan are using the wellknown Cutwail botnet to lure victims into downloading the banking malware.
A new wave of spam campaigns are dispensing "Gameover,” the ===> only banking trojan in the Zeus family to use peer-to-peer (P2P) communications to hide its activities. <===
Read more, a MUST: http://www.scmagazine.com/zeus-family-trojan-spreads-by-way-of-spam-botnet/article/271333/
Cracking encrypted passwords is getting increasingly easier as researchers come up with new ways of harnessing CPU, GPU and cloud power to perform the task.
Read more, a MUST: http://www.net-security.org/secworld.php?id=14077
|
Banks around the world are getting ready to face a massive cyber assault. But now that it’s been discovered, it might not happen as expected.
Cyber security is something that many consumers view more as a theoretical concept than an issue worth worrying about. After all, the majority of consumers have never been hacked or watched their bank accounts siphoned of cash.
===> For many folks, security issues are read about, never experienced. But that might soon change. <===
A so-called “cyber gang” of Botmasters was discovered in October to be working on a scheme that would allow them to target customer accounts at 30 banks, including Chase, Citibank, and even PayPal, and steal money from unsuspecting victims.
Graham Cluley jumps in his TARDIS, and takes us on a trip through time to see Christmas-related malware from 1987 to present.
Gust MEES's insight:
===> Be AWARE of the MALWARE! <===
Check also my other FREE courses here:
- http://gustmees.wordpress.com/category/get-smart-with-5-minutes-tutorials/
An infographic from security-testing company Veracode explores the rise of data breaches and what it could mean for businesses and consumers.
Security vendor Cloudmark says it is the first time they've detected a botnet that abuses other people's phones to send spam
New malware Batchwiper is unsophisticated, but can cause a lot of damage, researchers say
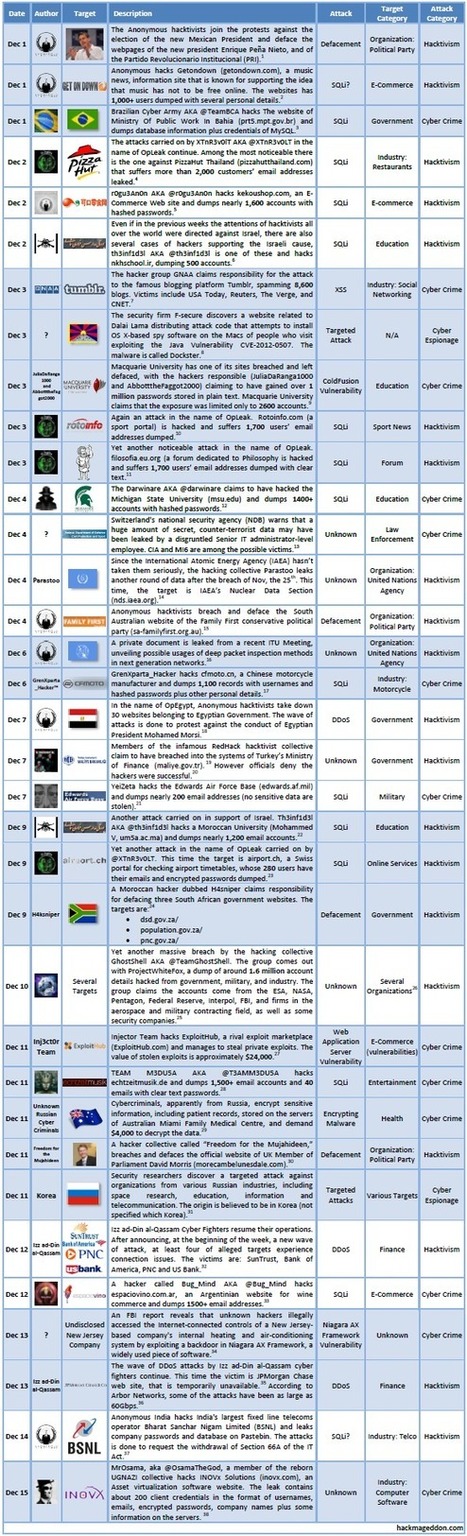
Christmas is coming quickly, we have just passed the first half of December, and hence it’s time for the first update of the Cyber Attacks Timeline for December. The Team GhostShell has decid...
Taking your tablet online can make you vulnerable to an assortment of internet dangers, including identity theft and hackers. This is especially true if you’re taking advantage of a public hotspot ...
==================================================== Gust MEES Please read also my FREE course here: - http://gustmees.wordpress.com/2012/11/29/cyber-hygiene-ict-hygiene-for-population-education-and-business/ ====================================================
Chrome 23, Internet Explorer 9 et 10, Flash 11.x, Java SE 6 et 7. Tous se voient proposer des mises à jour corrigeant des failles de sécurité critiques.
===> UPDATE asap!!! <===
Russian anti-virus company Doctor Web informs users about a new Trojan for Mac OS X dubbed Trojan.SMSSend.3666.
Cybercrooks are putting up stickers featuring URLs embedded in Quick Response codes (QR codes) as a trick designed to drive traffic to dodgy sites.
Sian John, UK security strategist at Symantec, said: “There has been an explosion in the number of QR codes over the last couple of years, and cybercriminals are taking full advantage. Because QR codes just look like pictures it’s extremely difficult to tell if they’re genuine or malicious, making it easy to dupe passers-by into scanning codes that may lead to an infected site, or perhaps a phishing site.
===========================================
Gust MEES
Please check also:
- http://www.scoop.it/t/apps-for-any-use-mostly-for-education-and-free?tag=QR-Reader-App
===========================================
Read more: http://www.theregister.co.uk/2012/12/10/qr_code_sticker_scam/
A recent survey from the Ponemon Institute and ID Experts found that breaches are costing the health care industry an average of 7 billion annually.
Read more:
Blackberry has always had a reputation for taking particular care when it comes to security.
Read more, a good practice example:

Jocyl Garcia's curator insight,
May 17, 2013 8:45 AM
not evrythng dat u wanted and worked hard for always meant to be yours
|














![Why You Should Care About Mobile Security [INFOGRAPHIC] | ICT Security-Sécurité PC et Internet | Scoop.it](https://img.scoop.it/bCDzCBQu4qMgWJAbygdm2jl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)