 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
January 2, 2013 11:08 AM
|
News that an Internet Explorer zero-day vulnerability was being and has been for quite some time been used in a new "watering hole" attack has livened the otherwise uneventful last week of 2012. The exploited website was that of the Council on Foreign Relations, an organization, publisher, and think tank specializing in U.S. foreign policy and international affairs, among whose members are a number of high-profile U.S. government and political figures such as former secretary of state Madeleine Albright, former treasury secretary Robert Rubin, and many others.

|
Scooped by
Gust MEES
January 2, 2013 10:50 AM
|
Sitting in an office in the Australian Security Intelligence Organisation’s Soviet-style building, which mirrors the Orwellian bunker one might imagine, Australia’s most experienced spy master, David Irvine, has a lot on his mind as he gazes over...

|
Scooped by
Gust MEES
December 31, 2012 8:10 AM
|
ThreatMetrix announced cybersecurity trends and risks businesses and consumers must keep top of mind in 2013. These include cyberwarfare, data breaches, migrating malware, BYOD, cloud computing, and mobile and social media fraud.

|
Scooped by
Gust MEES
December 31, 2012 3:46 AM
|

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
December 27, 2012 12:44 PM
|
Spoofing, banking attacks, authentication flaws, and more top the list of 2012's biggest mobile security headaches

|
Scooped by
Gust MEES
December 25, 2012 5:51 AM
|
A data stealer designed to collect users personally identifiable information from point of sale systems has been detected.

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
December 24, 2012 2:58 PM
|
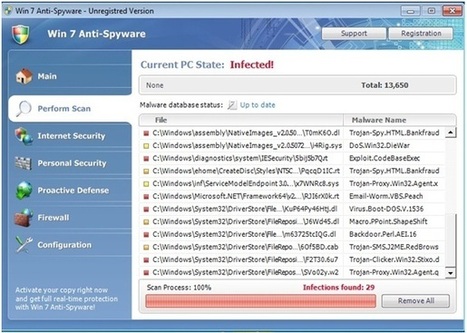
Compromised websites have been an attractive target for cyber-criminals. These websites distribute different malwares designed to steal valuable information from the victim’s machine. McAfee has recently encountered a compromised website which distributes malicious .jar file and Fake AV.
Via Gust MEES
And where are we going with OS X security in 2013? 2012 was an "exciting" year for OS X security—at least if you're a security expert or researcher. There were plenty of events to keep people on their toes. Although Apple took some egg on the face for some of them, overall, the company came out ahead when it came down to keeping users safe. At least that's the opinion of some security researchers who followed OS X developments throughout the year. A MUST READ!!!

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
December 23, 2012 3:24 PM
|
The National Security Agency's Perfect Citizen program hunts for vulnerabilities in 'large-scale' utilities, including power grid and gas pipeline controllers, new documents from EPIC show. Read this article by Declan McCullagh on CNET News.

|
Scooped by
Gust MEES
December 22, 2012 6:51 PM
|
A self-proclaimed hacker going by the name TibitXimer on Saturday leaked some 300,000 Verizon Wireless customer records after breaching the company's security systems. He downloaded ...

|
Scooped by
Gust MEES
December 21, 2012 4:03 AM
|
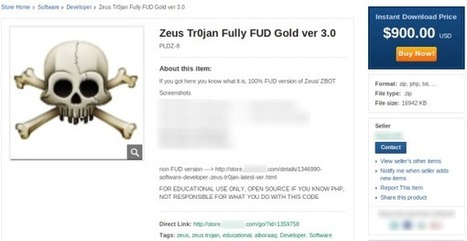
In the past, crime kits such as Zeus or SpyEye were only being sold on underground markets. However, Symantec has found several places where the illegal software is being sold openly and available to anyone.

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
December 20, 2012 5:22 AM
|
Au même titre que les années passées, les appareils connectés et en particulier les tablettes et les smartphones, seront sûrement dans de nombreuses (...)

|
Scooped by
Gust MEES
December 20, 2012 12:08 AM
|
Interested in the buzz around the Mayan calendar ceasing to increment after December 21st, 2012? ===> Don't go looking for presentations about the topic, you might be in for a nasty surprise!!! <===
|

|
Scooped by
Gust MEES
January 2, 2013 11:01 AM
|
A Trojan horse has been spammed out across the net, posing as zipped-up bikini images inside a screensaver.
Seriously, think for one minute before opening emails like this or face the consequenc...

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
January 2, 2013 8:52 AM
|
Researchers and attackers catalog vulnerable systems connected to the Internet, from video conferencing systems set to auto-answer to open point-of-sale servers to poorly configured database systems.

|
Scooped by
Gust MEES
December 31, 2012 5:37 AM
|
Britain is losing the war on internet crime, a leading police officer has admitted, after it emerged that cyber crime cost UK businesses around £205 million in lost revenue last year.

|
Scooped by
Gust MEES
December 29, 2012 2:52 PM
|
Stolen social security numbers. Erased online identities. Pilfered payment information, and even hacked hotel locks. Yep, 2012 was a banner year for the bad guys.

|
Scooped by
Gust MEES
December 25, 2012 2:27 PM
|
Android is the mobile equivalent of Windows -- hugely popular and open to security threats such as malware. Here's how to keep safe.

|
Scooped by
Gust MEES
December 25, 2012 5:48 AM
|
What happens once your identity gets stolen? How exactly does a phisher benefit from gaining access to your sensitive information? What can he do?
Of course it depends on the information stolen, and the goal of the hacker, as to what can be done with sensitive information. The first thing to clarify is that there are two types of phishing attacks – consumer oriented phishing attacks and enterprise oriented phishing attacks.

|
Scooped by
Gust MEES
December 24, 2012 10:21 AM
|
As 2012 comes to a close, it's time to reflect on the security trends of the year with this look at the hottest security slideshows of 2012.

|
Scooped by
Gust MEES
December 24, 2012 9:16 AM
|
Un fichier de coordonnées de plus d'un million de clients de la SNCB (chemins de fer belges) était accessible sur le Net. La bévue a été corrigée ce week-end.

|
Scooped by
Gust MEES
December 22, 2012 7:09 PM
|
Europe's top cybersecurity watchdog has warned that there are many problems with national or governmental Computer Emergency Response Teams (CERTs).

|
Scooped by
Gust MEES
December 22, 2012 6:40 PM
|
With a new year come new challenges. But while many see bringyourowndevice gaining momentum, more organizations may be ready to issue their own handhelds to employees.

|
Scooped by
Gust MEES
December 20, 2012 3:23 PM
|
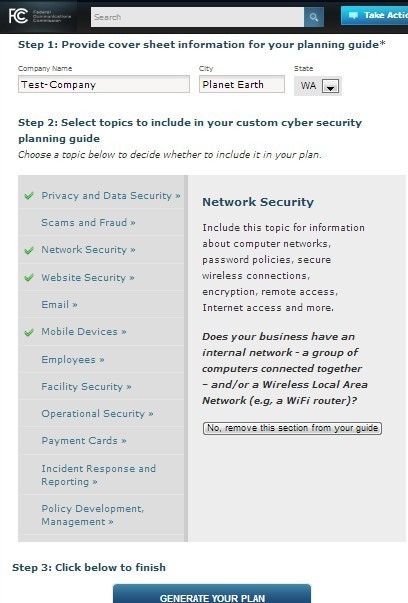
Information technology and high-speed Internet are great enablers of small business success, but with the benefits comes the need to guard against growing cyber threats. As larger companies take steps to secure their systems, less secure small businesses are easier targets for cyber criminals. In October 2012, the FCC re-launched Small Biz Cyber Planner 2.0, an online resource to help small businesses create customized cybersecurity plans. Use this tool to create and save a custom cyber security plan for your company, choosing from a menu of expert advice to address your specific business needs and concerns. ================================================== Gust MEES A MUST for Education and Business! Especially for "Bring Your Own Device" (BYOD) ==================================================

|
Scooped by
Gust MEES
December 20, 2012 12:17 AM
|
Iran, the cyber shooting range, new malware detected
Analysis revealed that the malicious code has a simple and efficient design that allows it to wipe files on different drives in various predefined times. The malware wipes disk partitions and user profile directories avoiding ordinary anti-virus software detection, Maher advisory provided the list of components of the malware:
|



 Your new post is loading...
Your new post is loading...

























The browsers are the gateway for malware!
===> They MUST get updated <===, check here:
- https://gustmees.wordpress.com/2012/11/29/cyber-hygiene-ict-hygiene-for-population-education-and-business/
- https://gustmees.wordpress.com/2012/05/02/get-smart-with-5-minutes-tutorialsit-securitypart-1-browsers/