 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
October 26, 2013 11:11 AM
|
Neben Bundeskanzlerin Angela Merkel sind noch viele weitere Regierungschefs auf der ganzen Welt vom US-Geheimdienst NSA abgehört worden. Das offenbart ein Geheimdokument von Whistleblower Edward Snowden.

|
Rescooped by
Gust MEES
from Luxembourg (Europe)
October 11, 2013 9:04 AM
|
The company's alleged involvement in the NSA's Prism program has put Luxembourg on notice, according to a recent report. Read this article by Don Reisinger on CNET News.

|
Scooped by
Gust MEES
September 19, 2013 10:11 AM
|
La NSA a souscrit pour 12 mois un contrat avec Vupen Security, un acteur français de la sécurité commercialisant des prestations de sécurité offensive et défensive, dont des failles Zero-day.

|
Scooped by
Gust MEES
September 12, 2013 12:00 AM
|
Les documents publiés à la suite de la confiscation il y a trois ans d'appareils électroniques à un défenseur du soldat Manning montrent que les services américains bloquent et fouillent à la frontière, des alertes permettant d'intercepter des...

|
Scooped by
Gust MEES
September 10, 2013 9:45 AM
|
More documents from former security contractor Edward Snowden show that the National Security Agency has been secretly working to gain a back door into all encryption technologies, The New York Times reports.

|
Scooped by
Gust MEES
September 7, 2013 12:13 AM
|
The NSA's Cryptographic Capabilities The latest Snowden document is the US intelligence "black budget." There's a lot of information in the few pages the Washington Post decided to publish, including an introduction by Director of National Intelligence James Clapper. In it, he drops a tantalizing hint: "Also, we are investing in groundbreaking cryptanalytic capabilities to defeat adversarial cryptography and exploit internet traffic." Honestly, I'm skeptical. Whatever the NSA has up its top-secret sleeves, the mathematics of cryptography will still be the most secure part of any encryption system. I worry a lot more about poorly designed cryptographic products, software bugs, bad passwords, companies that collaborate with the NSA to leak all or part of the keys, and insecure computers and networks. Those are where the real vulnerabilities are, and where the NSA spends the bulk of its efforts.
WASHINGTON -- The National Security Agency has broken privacy rules or overstepped its legal authority thousands of times each year since Congress granted the agency broad new powers in 2008, The Washington Post reported Thursday. Most of the infractions involve unauthorized surveillance of Americans or foreign intelligence targets in the United States, both of which are restricted by law and executive order. They range from significant violations of law to typographical errors that resulted in unintended interception of U.S. emails and telephone calls, the Post said, citing an internal audit and other top-secret documents provided it earlier this summer from NSA leaker Edward Snowden, a former systems analyst with the agency.

|
Scooped by
Gust MEES
August 12, 2013 10:42 AM
|
Revelations of the U.S. government's spying programs could have a massive impact on the U.S. cloud industry, which stands to lose vast sums over the next three years as a result — compounded by other countries bankrolling efforts to combat U.S.

|
Scooped by
Gust MEES
August 12, 2013 6:45 AM
|
Bei ihren Durchsuchungen von Internetdaten gehen die Mitarbeiter der NSA auch Informationen über Dritte nach, die bereits überwachte Personen erwähnen. Das kann auch US-Bürger betreffen.

|
Scooped by
Gust MEES
August 5, 2013 7:22 PM
|
"[Government Communications Headquarters] must pull its weight," UK spies wrote. NSA paid $152M over 3 years to British spy agency, new Snowden docs show"[Government Communications Headquarters] must pull its weight," UK spies wrote.

|
Scooped by
Gust MEES
August 2, 2013 4:58 PM
|
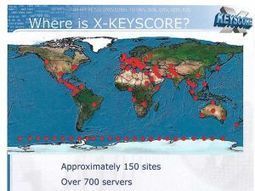
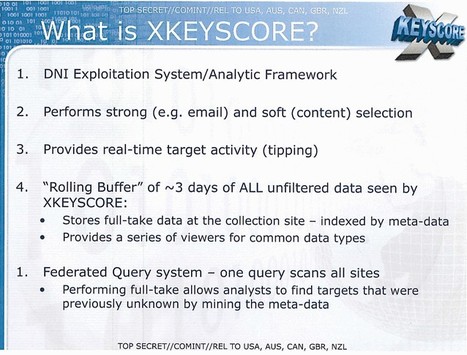
XKeyscore doesn't just turn somebody's Internet life inside out. It's also a blood hound for sniffing out vulnerable systems. According to Ars Technica's Sean Gallagher, the vulnerability "fingerprints" are added to serve as a filtering criteria for XKeyscore's application engines, comprised of "a worldwide distributed cluster of Linux servers attached to the NSA's Internet backbone tap points." This turns XKeyscore into a passive port scanner, Gallagher writes, which can be used to search for network behavior on systems that match the NSA TAO's profiles for exploits or for systems already exploited by malware that the TAO can then take advantage of.

|
Scooped by
Gust MEES
August 2, 2013 6:46 AM
|
Eine im Web veröffentlichte geheime Präsentation beweist: Die NSA überwacht mit der Spionagesoftware Xkeyscore das ganze Internet - und das sogar in Echtzeit.

|
Scooped by
Gust MEES
July 31, 2013 5:46 PM
|
In a story no doubt timed to the keynote speech from NSA Director General Keith Alexander at this year's Black Hat conference in Las Vegas, the Guardian has released information on Xkeyscore, a surveillance program run by the NSA.
|

|
Scooped by
Gust MEES
October 15, 2013 12:01 PM
|
The leaders who run the internet's technical global infrastructure say the time has come to end U.S. dominance over it.

|
Scooped by
Gust MEES
October 2, 2013 8:49 AM
|
The analysis of phone call and e-mail logs for foreign intelligence purposes adds to the growing body of knowledge about the agency’s access to private information, prompting concern from lawmakers.

|
Scooped by
Gust MEES
September 17, 2013 6:26 AM
|
Aus der Antwort auf eine Anfrage einer amerikanischen Bürgerrechts-Aktivistin geht hervor, dass der Geheimdienst Informationen über aktuelle Schwachstellen von der französischen Sicherheitsfirma erhält.

|
Scooped by
Gust MEES
September 10, 2013 8:49 PM
|
What happens when a secret U.S. court allows the National Security Agency access to a massive pipeline of U.S. phone call metadata, along with strict rules on how the spy agency can use the information?

|
Scooped by
Gust MEES
September 9, 2013 6:37 AM
|
Die NSA hat laut einem Medienbericht Arbeitsgruppen für jedes große mobile Betriebssystem. Die Angreifer können Kontaktlisten, SMS, E-Mail und Aufenthaltsorte auslesen.

|
Scooped by
Gust MEES
September 6, 2013 5:14 PM
|
NSA also bugged more than 80 embassies and consulates, says Der Spiegel.

|
Scooped by
Gust MEES
August 15, 2013 9:58 PM
|
The wide-reaching leak on data surveillance programs by Edward Snowden (who has sought asylum in Russia) is still ongoing.
According to the Washington Post, an internal audit and other top-secret documents show that the National Security Agency (NSA) has broken privacy laws or overstepped its legal authority thousands of times each year since it was granted broader powers in 2008. ===> In most cases, the NSA was involved in unauthorized surveillance of Americans or foreign intelligence targets in the U.S., despite these being restricted by law and executive order. <===

|
Scooped by
Gust MEES
August 12, 2013 9:31 AM
|
En parallèle des questions légales et morales, les fournisseurs américains de solutions cloud pointent toujours du doigt les conséquences de la révélation de la surveillance par la NSA sur leurs activités.

|
Scooped by
Gust MEES
August 7, 2013 6:25 AM
|
US-Cloud-Anbieter wie Microsoft, Amazon und Google haben durch die NSA-Enthüllungen zunehmend Probleme mit Kunden im Ausland. Das wird die Betreiber Milliarden kosten.

|
Scooped by
Gust MEES
August 5, 2013 9:20 AM
|
CNET has learned the FBI has developed custom 'port reader' software to intercept Internet metadata in real time. And, in some cases, it wants to force Internet providers to use the software. Read this article by Declan McCullagh on CNET News.

|
Scooped by
Gust MEES
August 2, 2013 6:54 AM
|

|
Scooped by
Gust MEES
August 2, 2013 6:34 AM
|
Verizon, BT, Vodafone, Global Crossing, Level 3, Viatel und Interoute helfen dem britischen Geheimdienst beim Ausspähen ihrer Kunden, berichtet die Süddeutsche Zeitung unter Berufung auf Folien des NSA-Whistleblowers Snowden. Einige der Firmen haben sich demnach für die Entwicklung von Software zum Ausspähen sogar bezahlen lassen.
|
 Your new post is loading...
Your new post is loading...
 Your new post is loading...
Your new post is loading...

































Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=PRISM
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Cyberespionage...