Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
July 13, 2011 7:11 AM
|
Twitter can be addictive. For some, it’s the perfect mix of an RSS reader, a chat room and a never-ending cocktail party. But for cybercriminals, it’s just another technology to be exploited.
To protect your irreplaceable content, relationships and financial information, remember the following while you’re tweeting, re-tweeting and hashtagging away:

|
Scooped by
Gust MEES
July 8, 2011 2:48 AM
|
My #1 help question of 2011? It’s no contest: “How do I protect myself online?

|
Scooped by
Gust MEES
July 7, 2011 2:58 PM
|
The rootkit allows its creators to sell YOUR computer to cyber-criminals - MalwareCity Blog on viruses description, botnets, spam review, malware history...

|
Scooped by
Gust MEES
May 29, 2011 3:36 PM
|
Secure your PC by easy to follow steps. A knol about a series of Knol-Tutorials who will show you how to secure your PC and...

|
Scooped by
Gust MEES
June 25, 2011 10:17 AM
|
Fiches de sécurité informatique

|
Scooped by
Gust MEES
May 31, 2011 7:09 AM
|
Military to gain a new range of offensive options to defend critical installations around the country from cyber attacks...

|
Scooped by
Gust MEES
May 26, 2011 11:58 AM
|
Apple’s security reality is changing right before our eyes and the company’s response will be telling.

|
Scooped by
Gust MEES
July 3, 2011 6:04 AM
|
WHY (SHOULD I BE WORRIED)?
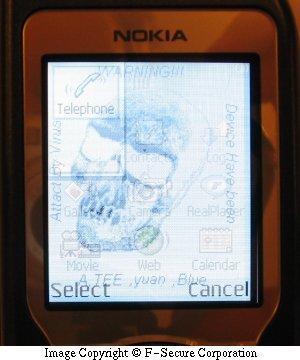
Worm:iOS/Ikee.A changed the phone's wallpaper
Last week I gave a brief summary of the kinds of threats a user might encounter on the smartphones of today. This week’s article is supposed to cover the reasons why a user would worry about mobile malware, so let me give the short answer now:
Usually, mobile malware attacks are motivated by: Bragging rights; money; stealing personal information that can be sold for money. For the user that gets hit by the malware, it means: Losing control over your phone; losing your money; someone else might be using your personal details for who-knows-what.

|
Scooped by
Gust MEES
May 25, 2011 5:11 PM
|
Apple finally responded to the Mac Defender outbreak, with a technical note containing removal instructions and the promise of a removal tool.

|
Scooped by
Gust MEES
May 27, 2011 8:44 AM
|
Un chercheur italien a démontré comment dérober à distance des informations de connexion stockées dans des cookies par IE. La technique est complexe et n’inquiète pas Microsoft, à ce stade.

|
Scooped by
Gust MEES
July 17, 2011 12:09 PM
|
Die neueste Version des mobilen Betriebssystems iOS schließt eine kritische Sicherheitslücke und deaktiviert den Jailbreak auf iPhone, iPad und iPod Touch.

|
Scooped by
Gust MEES
May 24, 2011 4:27 PM
|
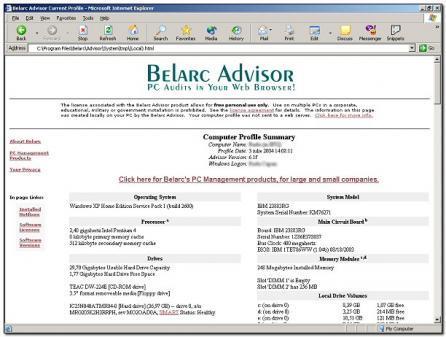
Get a free and detailed PC audit...

|
Scooped by
Gust MEES
May 23, 2011 11:59 AM
|
Yes, I realize that’s an ambitious title for a blog post about staying secure online, but there are a handful of basic security principles that — if followed religiously — can blunt the majority of malicious threats out there today.
|

|
Scooped by
Gust MEES
July 12, 2011 4:28 PM
|
Al-Qaeda is using social media sites such as Facebook to plan attacks in pursuit of a "cyber-jihad", the UK government warns.

|
Scooped by
Gust MEES
July 7, 2011 3:16 PM
|
SAN FRANCISCO — Hackers infected computers, derailed websites, and plundered networks in a memorably miserable quarter, according to a report released Wednesday by Internet security firm PandaLabs.
Hacking groups Lulz Security and Anonymous caused "widespread mayhem" during the three months ending June 30, and malicious software "spread substantially," according to the research unit of Spain-based Panda Security.

|
Scooped by
Gust MEES
July 7, 2011 12:21 PM
|
Hier, à Londres, l'organisme a été inauguré. Il regroupe divers gouvernements, entreprises et organisations d'état ...

|
Scooped by
Gust MEES
June 28, 2011 11:23 AM
|
When hackers from penetration testing firm Netragard were hired to pierce the firewall of a customer, they knew they had their work cut out. The client specifically ruled out the use of social networks, telephones, and other social-engineering vectors, and gaining unauthorized physical access to computers was also off limits.
Deprived of the low-hanging fruit attackers typically rely on to get a toe-hold onto their target, Netragard CTO Adriel Desautels borrowed a technique straight out of a plot from Mission Impossible: He modified a popular, off-the-shelf computer mouse to include a flash drive and a powerful microcontroller that ran custom attack code that compromised whatever computer connected to it.

|
Scooped by
Gust MEES
June 23, 2011 1:55 PM
|
What’s the best way to deal with malicious software on PCs and Macs?

|
Scooped by
Gust MEES
July 3, 2011 6:02 AM
|
From late 2010 to the first few months of 2011, there’s been a fair bit of buzz in the tech media about how mobile malware may be the big IT security issue for 2011. (To be fair, I also said something similar in a previous post.)
Even though PC threats are still hugely more prevalent, mobile malware tends to get more press because they’re like the up-and-coming starlets of tech threats – they’re fresh, new, interesting, and frankly, just a little sexier than plain ol’ Windows malware.

|
Scooped by
Gust MEES
July 3, 2011 6:07 AM
|
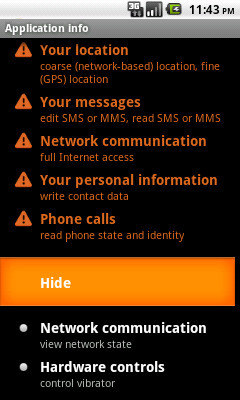
This is the third and final article in this series on mobile malware.
HOW (CAN I PROTECT MYSELF)?
Permissions request list from Trojan:Android/AdSMS
In my previous articles, I’ve covered what kind of mobile threats have emerged in the first half of 2011 and why these malicious programs may cause concern for smartphone users.
Now, let’s assume you’re a cautious smartphone user who wants to make sure you don’t get hit by a malware infection on your smartphone. What can you do?

|
Scooped by
Gust MEES
May 26, 2011 9:07 AM
|
A new variant of the fake security software for OS X was discovered today and it no longer requires administrators to enter their passwords. We take a brief look at the advancement of malware on the Mac over the last month.

|
Scooped by
Gust MEES
May 25, 2011 5:09 PM
|
SECURITE - Apple publie un guide pour se débarrasser du malware Mac Defender, en attendant une mise à jour de son OS...

|
Scooped by
Gust MEES
May 25, 2011 12:58 PM
|
Apple will deliver a Mac OS X update “in coming days” that will put its Mac Defender malware headaches to rest...

|
Scooped by
Gust MEES
May 25, 2011 4:57 AM
|
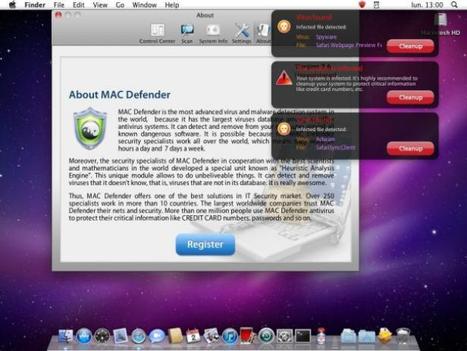
A recent phishing scam has targeted Mac users by redirecting them from legitimate websites to fake websites which tell them that their computer is infected with a virus. The user is then offered Mac Defender "anti-virus" software to solve the issue.
This “anti-virus” software is malware (i.e. malicious software). Its ultimate goal is to get the user's credit card information which may be used for fraudulent purposes.
The most common names for this malware are MacDefender, MacProtector and MacSecurity.
In the coming days, Apple will deliver a Mac OS X software update that will automatically find and remove Mac Defender malware and its known variants. The update will also help protect users by providing an explicit warning if they download this malware.
In the meantime, the Resolution section below provides step-by-step instructions on how to avoid or manually remove this malware.

|
Scooped by
Gust MEES
May 24, 2011 2:35 AM
|
Tough Economic Times ; Internet Safety; Bullying; Cyberbullying...
|



 Your new post is loading...
Your new post is loading...