Your new post is loading...
 Your new post is loading...
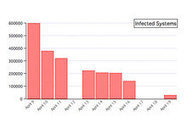
Die Sicherheitsexperten von Kaspersky melden, dass nur noch 30.000 Rechner mit dem Mac-Trojaner Flashback infiziert wären. Dr.Web geht hingegen von 566.000 Betroffenen aus. ===> Für Systeme mit einer älteren Version als Mac OS X 10.6 gibt es derzeit jedoch kein offizielles Java-Sicherheitsupdate!!! <===
Selon l’éditeur de sécurité Kaspersky, il ne reste plus que 30 000 Mac infectés par le malware Flashback à la date du 19 avril, contre 600 000 une dizaine de jours plus tôt.

|
Scooped by
Gust MEES
April 20, 2012 7:29 PM
|
SophosLabs is intercepting a spammed-out malware campaign, pretending to be an email about a revealing photo posted online of the recipient.
The emails, which have a variety of subject lines and...

|
Scooped by
Gust MEES
April 20, 2012 10:42 AM
|
Sicherheitsexperten warnen vor einem Backdoor, der bereits über eine Million Windows-Rechner infiziert und zu Mitgliedern eines Botnetzes gemacht haben soll.
The Flashback malware threat for OS X is on a steep decline, but still underscores that Mac systems are not immune to threats. Read this blog post by Topher Kessler on MacFixIt.
Kate Bevan: For too long Mac users have been complacent about malware – it's time they woke up to the threat from trojans like Flashback... ===> Mac users should 'become responsible members of the wider computing community.' <=== Read more...

|
Rescooped by
Gust MEES
from IT Security
April 19, 2012 7:27 AM
|
Tough economic times make it tempting for an employee to switch his white hat to a black one for financial gain. Insider threats also include contractors, auditors, and anyone who has authorized access to systems. Read more, A MUST...
Via IS Decisions
A new Trojan known as “Sabpab” could hurt Mac users who run Java and Microsoft Word. Security researchers are warning users to make sure their computers ===> have the latest software updates from both Apple and Microsoft, <=== and to use anti-virus software. In some cases, manual removal of Sabpab may be needed. Word about Sabpab comes on the heels of another nasty piece of malware, Flashback, that infected up to as many as 600,000 Macs, security experts said, by exploiting a vulnerability in Java software. Apple last week issued a software-base removal tool for that malware, which can be used by criminals to steal personal information, including passwords. Read more...

|
Scooped by
Gust MEES
April 18, 2012 4:36 PM
|
According to authorities, Murmylyuk was part of a gang that beginning in late 2010, gained access to online trading accounts at Scottrade, e*Trade, Fidelity, Charles Schwab, and other brokerage firms and conducted a series of sham trades. Once the hackers controlled the accounts, they used stolen identities to open additional accounts at other brokerage houses, and then initiated "unprofitable and illogical securities trades" that benefited the attackers. They also changed the phone numbers and email addresses on file to prevent victims from being notified of the illegal trades. If convicted, Murmylyuk faces a maximum penalty of five years in prison and a $250,000 fine. Read more...
D'autres chevaux de Troie, moins graves que Flashback, ont visé Mac OS X - Malware - Après avoir découvert le Cheval de Troie Flashback sur Mac, les...
Given the attention that the Flashback Mac malware has received since the discovery of the 600K strong botnet of computers infected with it and the number of tools that various security firms and Apple issued for its removal, it's somewhat disheartening to hear that===> the botnet still counts around 140,000 zombies. <=== Read more...
Alors qu'Apple et plusieurs éditeurs en sécurité viennent de publier des correctifs pour venir à bout du cheval de Troie Flashback, un nouveau malware s'invite actuellement sur Mac OS X. Son nom : Backdoor.OSX.SabPub.a.

|
Scooped by
Gust MEES
April 18, 2012 10:24 AM
|
Advisory boards have been established by ISC to act as a resource for industry, government and special interest groups. Read more...
|

|
Scooped by
Gust MEES
April 21, 2012 9:24 AM
|
Infected pages look to compromise employee systems...
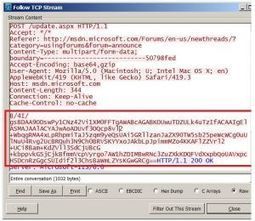
Le retour récent dans l'actualité du malware Flashback a remis en avant les questions de sécurité autour du Mac. Les auteurs de ces malware ont également un total contrôle des Mac infectés et peuvent installer et exécuter de nouveaux codes natifs OS X, via le processus de mise à jour de Flashback. Je l'ai observé dans une de mes boîtes virtuelles (un OS X fonctionnant dans une machine VMware), un binaire shell a été installé et un malfaiteur a exécuté des commandes shell sur cette machine virtuelle, pour vite s'apercevoir de la supercherie (on peut voir ces machines virtuelles comme des chèvres attachées à un piquet…, ndr). À mon avis la personne à l'autre bout avait un doute sur l'infection réalisée… et il avait raison. Veuillez lire plus, très intéressant...

|
Scooped by
Gust MEES
April 20, 2012 7:27 PM
|
The need for more effective information security practices is increasingly evident with each security breach reported in the media. When adopting new technologies like cloud computing, virtualization, or IT outsourcing, enterprises are facing imminent security threats and must adjust their security processes, policies, and architectures accordingly. Read more...
La firme de Cupertino arrive en tête du classement réalisé par Trend Micro devant Oracle, Google et Microsoft.

|
Scooped by
Gust MEES
April 19, 2012 10:42 AM
|
In an attempt to take advantage of the popularity of free photo-sharing app Instagram among smartphone users, malware writers have created fake Instagram...

|
Rescooped by
Gust MEES
from Social Media and its influence
April 19, 2012 9:28 AM
|
Live from the Emsisoft Lab.... A few weeks ago our colleagues over at BleepingComputer approached us asking for help with a recent malware outbreak that specifically targets Windows servers. Several companies as well as individuals found their servers being locked by a malware that claims to originate from the “Anti Cyber Crime Department of Federal Internet Security Agency” or short “ACCDFISA”. Of course such an institution does not exist and even if it did, it surely wouldn’t ask the owner of the server to submit a certain dollar amount using PaySafeCard or MoneyPak codes. The affected servers fell prey to a new malware family that is currently on the loose. The ACCDFISA malware family belongs to a malware category called “ransomware”. Ransomware is a special kind of malware that takes a system and its data hostage in an attempt to extort money from its owner in exchange for returning control back to him. What makes the ACCDFISA family special is the unorthodox way in which systems get infected as well as how various third party tools are used to accomplish the malware family’s goals. Read more...

|
Scooped by
Gust MEES
April 19, 2012 7:12 AM
|
SecurEnvoy revealed details of its latest release that gives users full flexibility of the device they use, while ensuring complete security to the organization. At the click of a button users can have their authentication token as an SMS on a mobile, an app on a smartphone or tablet, or a soft token on a laptop – with the ability to swap between devices at will. Read more...

|
Scooped by
Gust MEES
April 18, 2012 5:50 PM
|
SC Magazine has various news articles and information for IT security professionals. Bring-your-own-device and cloud security are just some of the topics that add to the changing threat landscape of online security. Read more...
Java update is no protection against new SabPub Mac Trojan! SabPub Mac Trojan is spreading via Word documents, using an ancient vulnerability... Read more...
Repéré par des chercheurs de chez Kasperky, le malware SabPub exploite une fois encore une faille de sécurité Java dans Mac OS X via des documents Word piégés.
Découvert par Kaspersky, ce nouveau malware qui cible les Mac exploite une faille de sécurité Java. Le répit aura été de courte durée. À peine Apple avait-il publié une mise à jour de Java contenant un logiciel de suppression du malware Flashback qu’un nouveau fléau était découvert. Baptisé SabPub, il a été découvert par l’éditeur Kaspersky qui en a repéré deux variantes. Comme Flashback, SabPub passe par une faille de sécurité de Java au moyen d’un document Word piégé. Le Mac infecté va ensuite se connecter à un site web depuis lequel sont envoyées des commandes. Un pirate peut notamment obtenir des captures d’écran du Mac de la victime. Cependant, le mode de diffusion de ce malware via des documents Word piégés rend sa propagation moins puissante que celle de Flashback qui a touché 600 000 machines de par le monde.

|
Scooped by
Gust MEES
April 18, 2012 10:38 AM
|
17 April 2012
"MAKING EUROPE SAFER: Europol at the Heart of European Security" co-organised by the Academy of European Law (ERA) and Europol The Hague, 18-19 June 2012
Target audience: law enforcement officers, ministry officials, legal practitioners, as well as representatives of academia and NGOs
This conference at Europol’s new headquarters will mark the tenth anniversary of the ERA organisation and bring together its members, law enforcement agents, civil society representatives, ministry officials and legal practitioners to debate the role of Europol in the coming years. Two major developments in recent years have confirmed the place of Europol as a major EU actor. First, Council Decision 2009/371/JHA, which entered into force on 1 January 2010, finally established Europol as a European agency and broadened and strengthened its competences. Secondly, on 1 July 2011, Europol inaugurated its new headquarters in a building specifically designed for it. From dealing almost exclusively with drug-related matters at its origins, Europol now has an ever expanding set of priority areas.
|



 Your new post is loading...
Your new post is loading...