 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
March 21, 2014 1:07 PM
|
Two researchers at California Polytechnic San Luis Obispo have created an application for Google Glass that can spy on everything the wearer is looking at, without the knowledge of the user.
If you do insist on wearing Google Glass, then please make sure that you have protected your devices using a passcode, and be careful about what apps you install on your devices from unofficial app stores.
Chances are that there will be others out there, with more malicious intentions than Mike Lady and Kim Paterson, who will be interested in spying upon what Google Glass wearers are looking at.
Apple has quietly pushed out a security update to iOS, the operating system used by its flagship iPhone and iPad products.
And it's really important for your privacy that you update your iPhones and iPads as quickly as possible.
===> A shame then that Mac OS X doesn't yet have a patch... <===

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
January 13, 2014 12:05 PM
|
With the pace of innovation of Internet-connected devices, experts are worried security will struggle to catch up. They are all impressive but "they're all breachable" said Kevin Haley, director of Symantec Security Response, while attending the huge high-tech trade show. "If the object is connected to the Internet, you will find it, and if it has an OS (operating system) you can hack it," he told AFP at the Las Vegas expo. Haley said the pace of innovation could outstrip the security protecting the devices. ===> "As we start to bring all this new stuff in our houses, we're going have to take some responsibility," he said. <===

|
Scooped by
Gust MEES
December 31, 2013 10:31 AM
|
Breathless headlines suggest that the NSA can snoop on everyone's iPhone, turn on your phone's camera and read all your messages.
But the story isn't quite as simple as that.
Utrecht, le 27 novembre 2013 - Selon une récente enquête de Kaspersky Lab, il existe de fortes probabilités qu’un nombre croissant d’utilisateurs Mac soient la proie de menaces d’Internet. La quantité des logiciels malveillants ciblant les Mac a augmenté de 50% au cours des douze derniers mois. Pourtant, plus d’un tiers (35%) de tous les utilisateurs Mac pensent à tort être protégés contre les menaces numériques.
Le nombre des propriétaires de Mac continue de progresser, et par conséquent l’intérêt des cybercriminels pour cette plate-forme s’amplifie lui aussi. Les virus informatiques, chevaux de Troie, astuces de phishing et autres menaces d’Internet visant cette plate-forme sont d’ores et déjà en circulation, en grands nombres qui plus est. Les utilisateurs sont ainsi tout aussi vulnérables que les utilisateurs de PC Windows.
Via Gust MEES

|
Scooped by
Gust MEES
November 23, 2013 11:08 AM
|
During an investigation into how a breach occurred at a large internet hosting provider, researchers found a Linux backdoor capable of stealing login credentials from secure shell connections.
===> The Fokirtor Trojan targets users of the Linux operating system. <===

|
Scooped by
Gust MEES
November 20, 2013 9:38 AM
|
GitHub users should consider changing their account password to a more complex one and setting up 2-factor authentication in order to protec...
About 860,000 members who post on the forums of popular Apple news website MacRumors are being asked to change their passwords after accounts were compromised in a hack.
Via Gust MEES

|
Rescooped by
Gust MEES
from 21st Century Learning and Teaching
September 30, 2013 12:51 PM
|
Another day, another privacy vulnerability found in iOS.
When will Apple learn that a lockscreen should really, properly, lock the phone?
Via Gust MEES
Two US security researchers have revealed how they hacked the computer system inside two popular models of car.
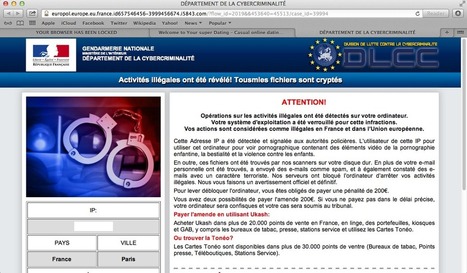
Further customizations of the Mac ransom pages discovered today shows the bad guys are busy updating their templates for each country's police force. ===> Not all countries currently have their own ‘theme’ but it is only a matter of time before the bad guys roll them out. <===
Via Gust MEES
Apple's developer portal has been offline since the middle of last week. On Sunday, Apple explained the outage.
Via Gust MEES
|

|
Scooped by
Gust MEES
March 4, 2014 3:07 PM
|
This GnuTLS bug is worse than the big Apple "goto fail" bug patched last week.

|
Scooped by
Gust MEES
January 15, 2014 11:24 AM
|
News spread that the hacking group got into the Microsoft News Twitter account, but apparently it also breached Xbox's Twitter and Instagram accounts. Read this article by Dara Kerr on CNET News.

|
Rescooped by
Gust MEES
from CYBER SECURITY LIVES HERE
January 8, 2014 6:30 AM
|
A Pakistani hacker named ‘H4x0r HuSsY’ has successfully compromised the official Forum of the popular Linux OS openSUSE accessing to the database.
Via GianniPintonello

|
Scooped by
Gust MEES
December 31, 2013 5:38 AM
|
The National Security Agency knows no boundaries -- and has tools for spying that span computers, keyboards, firewalls and servers, or nearly all the security architecture created by ...

|
Scooped by
Gust MEES
November 27, 2013 12:09 PM
|
Symantec has discovered a new Linux worm that appears to be engineered to target the “Internet of things”. The worm is capable of attacking a range of small, Internet-enabled devices in addition to traditional computers.

|
Scooped by
Gust MEES
November 21, 2013 7:21 AM
|
Untersucht wurden 2107 Apps für iOS von 601 Herstellern. Die HP-Tochter bewertet die entsprechenden Android-Anwendungen jedoch als ebenso anfällig. Zahlreiche Apps setzten keine Verschlüsselung ein und schützten die Nutzerdaten nicht angemessen.

|
Scooped by
Gust MEES
November 14, 2013 6:49 AM
|
In May of this year, sophisticated attackers breached a large Internet hosting provider and gained access to internal administrative systems. The attackers appear to have been after customer record information such as usernames, emails, and passwords.
While these internal administrative systems had access to customer records, discovery of the attack and certain security implementations mitigated the scope of the breach. Customer passwords were accessible, but these passwords were hashed and salted making mass password cracking difficult. Customer financial information was also accessible, but encrypted. Unfortunately, access to the encryption key cannot be ruled out.
While breaches of organizations and mass customer record dumps are posted almost daily, this particular attack was more sophisticated than we have seen in the past.
Macs have never been that popular in business. But if Apple is indeed no longer supporting security updates for older Mac OS X versions, Macs won't have any place left in the enterprise office.
iPhones and iPads will be vulnerable until they get the iOS 7 update, which is scheduled for release later this year. Until then, you might want to avoid plugging into sleazy charging stations, tho...
Via Gust MEES
For a very long time, Apple and its pseudo-religious user-base prided itself on being a platform free of malware; those days are inarguably and unequivocally over. Its emergence as the early winner...
Via Gust MEES
Cupertino finally gives an explanation for the extended downtime of its developer website. After a weekend of outage and mysterious password reset emails, Apple has revealed the cause of the extended downtime of its developer website. ===> "Last Thursday, an intruder attempted to secure personal information of our registered developers from our developer website," Apple said in an email sent to developers. <=== While Apple claimed that the site's information was encrypted, and thus unable to be accessed, the company could not rule out that developer names, mailing addresses, or email addresses were not accessed during the incident.
Via Gust MEES
You may want to think twice about using your iPhone as a wireless hotspot. A group of researchers from the Department Informatik at Friedrich-Alexander-Universität Erlangen-Nürnberg in Germany deve...
Via Gust MEES
|



 Your new post is loading...
Your new post is loading...








![Yet another iPhone lockscreen vulnerability. This time in iOS 7.02 [VIDEO] | ICT Security-Sécurité PC et Internet | Scoop.it](https://img.scoop.it/boKnUeA0iZ0rIALHJ2F8kzl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)

![Download with Caution! McAfee Identifies Risky Mobile App Sources [Infographic] | ICT Security-Sécurité PC et Internet | Scoop.it](https://img.scoop.it/nlwfbsAWi3frp2_-nQ6pvTl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)


















If you do insist on wearing Google Glass, then please make sure that you have protected your devices using a passcode, and be careful about what apps you install on your devices from unofficial app stores.
Chances are that there will be others out there, with more malicious intentions than Mike Lady and Kim Paterson, who will be interested in spying upon what Google Glass wearers are looking at.