Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
November 24, 2014 2:39 PM
|
Security researchers have discovered a new type of "Man-in-the-Middle" (MitM) attack in the wild targeting smartphone and tablets users on devices running either iOS or Android around the world.
The MitM attack, dubbed DoubleDirect, enables an attacker to redirect a victim’s traffic of major websites such as Google, Facebook and Twitter to a device controlled by the attacker. Once done, cyber crooks can steal victims’ valuable personal data, such as email IDs, login credentials and banking information as well as can deliver malware to the targeted mobile device.
San Francisco-based mobile security firm Zimperium detailed the threat in a Thursday blog post, revealing that the DoubleDirect technique is being used by attackers in the wild in attacks against the users of web giants including Google, Facebook, Hotmail, Live.com and Twitter, across 31 countries, including the U.S., the U.K. and Canada.

|
Scooped by
Gust MEES
November 7, 2014 4:25 PM
|
Researchers have pointed out an interesting aspect of the iOS malware. The threat contains binary code for 32-bit ARMv7, 32-bit ARMv7s, and 64-bit ARM64 architectures. This makes WireLurker the first iOS malware that targets the ARM64 architecture.
The Maiyadi App Store on which the initially discovered variants were hosted seems to be linked to the creators of the malware, Palo Alto said. One piece of evidence is the bundle identifier named "com.maiyadi.installer" in the OS X samples. The samples also include copyright information referencing Maiyadi.
The C&C servers user by WireLurker are currently inactive, and Apple has taken steps to ensure that its users are protected, including the revocation of the stolen code signing certificates used by the malware creators to run the malicious iOS apps on non-jailbroken devices.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security?q=wirelurker

|
Scooped by
Gust MEES
December 31, 2013 12:03 PM
|
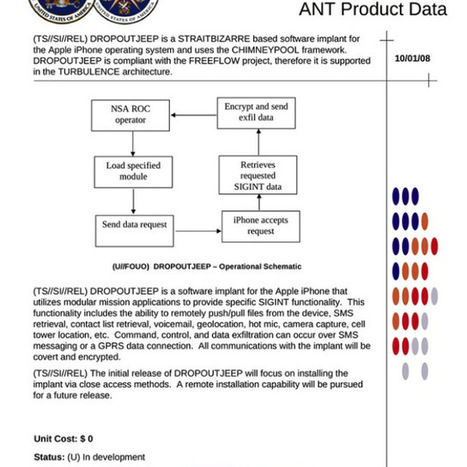
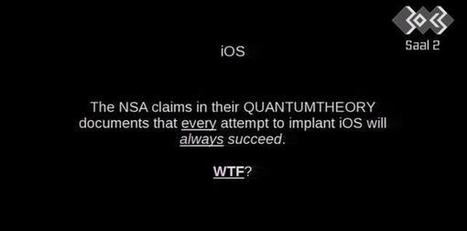
Apple has contacted TechCrunch with a statement about the DROPOUTJEEP NSA program that detailed a system by which the organization claimed it could snoop on..

|
Scooped by
Gust MEES
January 17, 2013 7:53 AM
|
AdaptiveMobile today sheds light on the extent of a new global SMS spam threat. According to Ongoing Threat Analysis (OTA) which examines mobile security threats from around the world, consumers should to be on the lookout for fraudulent spam texts informing them they have won a free Apple product such an iPad, iPhone or MacBook.
The texts frequently include a web address that looks like it is from Apple but upon closer inspection is not a legitimate Apple website and are sent from US mobiles numbers (+1-XXX-XXX-XXXX).
“Congratulations! You are Australia’s WINNER OF THE DAY! Go to http://www.apple.au.[redacted].com to claim your prize. Must claim within 24 hrs.”
“Your phone was randomly chosen as Apple’s Over-Stock iWinner. Go to http://ie.appleoverstock.[redacted] & type code 2872 to win your Free Gift-Card now!”
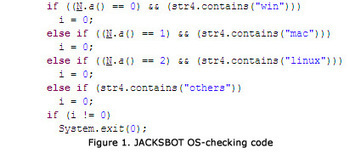
Two weeks ago, Mac security software company Intego discovered malware which it classified as "a new Java backdoor trojan called Java/Jacksbot.A.” New threats are discovered all the time, but Intego later concluded that even though Jacksbot is a variant of the Java remote access tool (RAT) created by the jailbreaking group Redpois0n, it can target multiple platforms. The malware writers behind JACKSBOT may just be testing the waters for a successful multiplatform malware; however for now they appear to be unwilling to invest the time and resources to develop the code more completely. ===> It’s likely that the authors will continue to improve the code to fully support infection for OS X and Linux. <=== Read more, a MUST: http://thenextweb.com/2012/10/31/jacksbot-java-malware-can-take-control-of-windows-mac-and-linux-systems/?utm_source=dlvr.it&amp;utm_medium=twitter

|
Scooped by
Gust MEES
September 4, 2012 9:56 AM
|
According to Wired, Amazon no longer allows people to call Amazon and change account settings such as email addresses and credit cards, and Apple has temporarily suspended the option of asking for an AppleID password reset over the phone. Read more: http://www.net-security.org/secworld.php?id=13392
Il semble bien que le mythe du Mac infaillible soit en train de tomber. Après l'épisode Flashback (un malware ciblant exclusivement les ... La maturité pour Apple ? Lorsque l'on regarde l'ancienne version de la page, le discours passé d'Apple fait sourire. Il était temps que l'entreprise redescende sur terre, et reconnaisse enfin la vulnérabilité de son OS aux menaces des cybercriminels. L'épisode Flashback y est certainement pour quelque chose. L'entreprise à la pomme a sûrement pris conscience de quelque chose. On espère que cela la poussera à se focaliser davantage sur la sécurité, de même que ses consommateurs (qui se croient encore trop souvent hors d'atteinte). En savoir plus : http://www.linformaticien.com/actualites/id/25390/apple-l-admet-il-y-a-des-virus-sur-mac.aspx
Security industry insiders have long known the Mac platform has its holes. The Flashback Trojan is the first in-the-wild issue that's confirmed this, and big-time. More will follow unless Apple steps up its game. Apple has cultivated a myth about security on the Mac platform. The myth goes like this: Apple users don't need antivirus software. We're more secure than anything out there. Security worries are overblown.
In reality, Apple practiced security by obscurity with the Mac.
Those days may be ending in a hurry. Apple's relative silence about malware is going to have to end as the company finds itself managing a large ecosystem, noted ZDNet's Ed Bott.
Delivering massive security updates during product launches and software rollouts just isn't going to cut it. ===> Read more, YOU should!!! <===
Secunia’s Chief Security Specialist hopes Apple will work better with researchers in the future and provide more informative status updates and estimated fix dates. ”It's regretful to experience that there are still some major software vendors that do not understand how to properly work with researchers,” Eiram added. “Hopefully, Apple will in the future strive to work better with researchers to ultimately protect their customers by providing more informative status updates and estimated fix dates instead of prioritizing antiquated internal policies higher.”
|

|
Scooped by
Gust MEES
November 15, 2014 3:58 AM
|
L’iPhone 5S a été mis à mal par une équipe de Corée du Sud, qui a réussi à profiter d'une combinaison de deux bugs dans Safari pour en prendre le contrôle. Le Samsung Galaxy S5 non plus n'a pas réisté aux assauts des hackers. Deux équipes ont profité de failles dans la gestion du protocole NFC pour en prendre le contrôle. le Nexus 5 a lui aussi été piraté via NFC, grâce à une technique étonnante, qui a consisté à forcer un appairage Bluetooth entre deux appareils.

|
Scooped by
Gust MEES
May 27, 2014 6:59 PM
|

|
Scooped by
Gust MEES
December 31, 2013 10:31 AM
|
Breathless headlines suggest that the NSA can snoop on everyone's iPhone, turn on your phone's camera and read all your messages.
But the story isn't quite as simple as that.

|
Scooped by
Gust MEES
September 5, 2012 6:01 AM
|
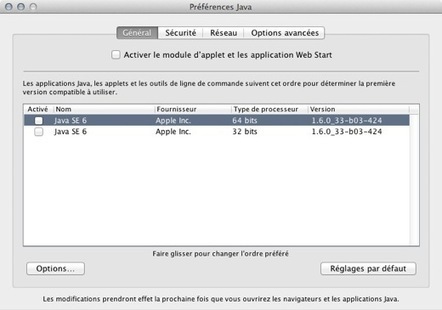
Actualité Apple : OS X : désactiver JAVA en attente d'un correctif de sécurité... JAVA ne se traine pas une formidable réputation en matière de sécurité, surtout sur nos Mac où Apple a souvent fait preuve d'une formidable lenteur pour mettre à jour la machine virtuelle JAVA. Désormais c'est Oracle qui préside aux destinées de la brique logicielle sur nos machines pommées. En attendant, si vous n'en avez pas un besoin immédiat et absolu, vous pouvez simplement désactiver JAVA pour régler la question. Pour cela, direction le dossier Utilitaires de votre dossier Applications. Lancez Préférences JAVA et, dans l'onglet gGénéral, désactivez Java SE 7 (oui, l'image montre un système avec JAVA 6). Et voilà. Pour réactiver, procédure inverse.

|
Scooped by
Gust MEES
July 5, 2012 11:14 AM
|
In KB article HT5244, Apple has - apparently for the very first time! - talked openly about a security problem before it has all its threat reponse ducks in a row.
This is good news.
The nightmare scenario for Mac owners is here. At least 600,000 Macs worldwide have been infected, silently, by the Flashback virus. What makes this outbreak especially chilling is that the owners of infected Macs didn’t have to fall for social engineering, give away their administrative password, or do something stupid. All they had to do was visit a web page using a Mac that had a current version of Java installed. Macs are not immune. For years Apple owners have been told that Macs don’t get viruses, but we know that’s not true. And Apple’s casual approach to security updates makes them arguably more vulnerable to this sort of attack than other platforms.
|




 Your new post is loading...
Your new post is loading...