 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
June 29, 2018 8:36 AM
|
Data breaches are always bad news, and this one is peculiarly bad.
Gentoo, a popular distribution of Linux, has had its GitHub repository hacked.
Hacked, as in “totally pwned”, taken over, and modified; so far, no one seems to be sure quite how or why.
That’s the bad news.
Fortunately (we like to find silver linings here at Naked Security):
The Gentoo team didn’t beat around the bush, and quickly published an unequivocal statement about the breach.
The Gentoo GitHub repository is only a secondary copy of the main Gentoo source code.
The main Gentoo repository is intact.
All changes in the main Gentoo repository are digitally signed and can therefore be verified.
As far as we know, the main Gentoo signing key is safe, so the digital signatures are reliable.
Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Linux

|
Scooped by
Gust MEES
April 30, 2018 6:20 PM
|
Over a million fiber routers can be remotely accessed, thanks to an authentication bypass bug that's easily exploited by modifying the URL in the browser's address bar.
The bug lets anyone bypass the router's login page and access pages within -- simply by adding "?images/" to the end of the web address on any of the router's configuration pages, giving an attacker near complete access to the router. Because the ping and traceroute commands on the device's diagnostic page are running at "root" level, other commands can be remotely run on the device, too.
The findings, published Monday, say the bug is found in routers used for fiber connections. These routers are central in bringing high-speed fiber internet to people's homes.
At the time of writing, about 1.06 million routers marked were listed on Shodan, the search engine for unprotected devices and databases. Half the vulnerable routers are located on the Telmex network in Mexico, and the rest are found on in Kazakhstan and Vietnam. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Router

|
Scooped by
Gust MEES
April 9, 2018 1:27 PM
|
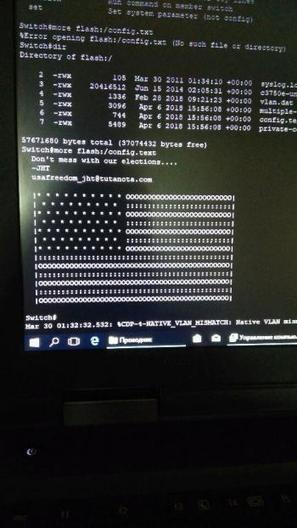
Unbekannte haben eine Sicherheitslücke in Cisco-Routern ausgenutzt und auf Systemen in Russland und Iran eine politische Botschaft hinterlassen. In westlichen Ländern hingegen schlossen sie die Lücke - behauptet zumindest eine anonyme E-Mail.
Hacker mit Sympathie für die USA nehmen für sich in Anspruch, am vergangenen Freitag zahlreiche Computersysteme in Russland und dem Iran über eine Sicherheitslücke gekapert und eine Abbildung der amerikanischen Flagge hinterlassen zu haben – zusammen mit dem Warnhinweis: "Don't mess with our elections..." (zu deutsch etwa: Mischt euch nicht in unsere Wahlen ein). Das meldet das Online-Magazin Motherboard.
"Don't mess with our elections..." Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberattacks

|
Scooped by
Gust MEES
March 1, 2018 3:26 PM
|

|
Scooped by
Gust MEES
November 27, 2017 11:16 AM
|
Eine DDoS-Attacke hat die Kryptowähungs-Börse Bitfinex lahmgelegt. Das bestätigten die Betreiber auf Twitter. Der Angriff sei während Wartungsarbeiten an der Infrastruktur gestartet worden.
Während Wartungsarbeiten an der Infrastruktur legten Hacker die Kryptowährungs-Börse Bitfinex mit einer DDoS-Attacke lahm. Wie die Betreiber auf Twitter mitteilen, ist der Angriff noch in vollem Gange.
Damit erleidet die Tauschbörse einen weiteren schweren Schlag. Erst vor wenigen Tagen hatte die von den Bitfinex-Machern entwickelte Kryptowährung Tether durch einen Cyber-Angriff 31 Millionen US-Dollar verloren. Es bleibt abzuwarten, wie lange die Nutzer der Plattform noch ihr Vertrauen schenken.
Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Bitfinex https://www.scoop.it/t/securite-pc-et-internet/?&tag=crypto-currency

|
Scooped by
Gust MEES
November 22, 2017 5:42 PM
|
Der Sicherheitsforscher Florian Bogner, der für den österreichischen IT-Dienstleister Kapsch arbeitet, hat einen Fehler in Antivirenlösungen verschiedener Hersteller gefunden, der diese Produkte unter Umständen unbrauchbar macht. Demnach ist es möglich, bereits erkannte Schadsoftware an den Sicherheitsanwendungen vorbei aus der Quarantäne zu holen und auszuführen. Der von ihm als AVGater bezeichnete Fehler betrifft demnach unter anderem Check Point, Emisoft, Ikarus, Kaspersky Lab, Malwarebytes, Trend Micro und Zone Alarm.
Allerdings muss ein Angreifer lokalen Zugriff auf das System haben, wie Bleeping Computer berichtet. Administratorrechte benötigt er jedoch nicht – ein Konto mit eingeschränkten Nutzerrechten ist vollkommen ausreichend. Die für die Ausführung der Malware benötigten höheren Rechte erhält der Angreifer später automatisch von der Antivirensoftware. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=antivirus

|
Scooped by
Gust MEES
November 22, 2017 3:29 PM
|
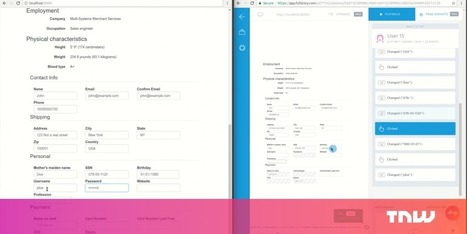
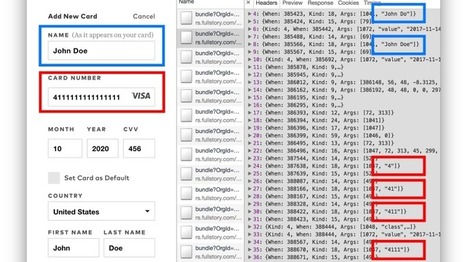
Hundreds of websites record your scrolling behavior, clicks and movements according to a study recently carried out at Princeton University. Among these are The Guardian, Reuters, Samsung, AlJazeera and WordPress.com.
Most of us are aware that our searches, page views and even page scrolls are documented, but the report sheds light on how intricate that tracking can be. Using something called “session replays,” they record keystrokes and movements a user makes while they navigate a page — basically “looking over your shoulder,” but virtually.
The study, carried out by Princeton’s Center for Information Technology Policy, focused on some of the main companies that offer session replay services: SessionCam, UserReplay, FullStory, Clicktale, Yandex, Smartlook, and Hotjar.
It’s important to understand why this is dangerous — apart from straight-up invading your privacy. The report pointed out that most of these services directly exclude password input fields from recordings, but a lot of the time mobile-friendly forms are not redacted on the recordings, and end up revealing sensitive information, including passwords, credit card numbers, and even credit card security codes.
The report explains, “All of the companies studied offer some mitigation through automated redaction, but the coverage offered varies greatly by provider. UserReplay and SessionCam replace all user input with an equivalent length masking text, while FullStory, Hotjar, and Smartlook exclude specific input fields by type.”
This kind of information is usually shared when a user is signing up for a service or making a payment, and is expected to be completely confidential. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Session-Replay+Scripts https://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberespionage https://www.scoop.it/t/securite-pc-et-internet/?&tag=Privacy https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/

|
Scooped by
Gust MEES
November 22, 2017 12:44 PM
|
Mit einer Technik namens Session-Replay lassen sich Texteingaben auf Webseiten in Echtzeit erfassen, während sie passieren. Diese Daten werden oft an Drittwebseiten zum Zwecke der Besucheranalyse übermittelt.
Die meisten Webnutzer haben eine Vorstellung davon, dass besuchte Webseiten nachverfolgen, auf welche Links sie geklickt haben und welche Seiten geladen wurden. Viele wissen auch, dass eine große Anzahl an Webseiten diese Informationen mit Drittfirmen teilt – hauptsächlich zu Analyse- und Werbezwecken. Weniger bekannt ist, dass manche Webseiten auch alle Texteingaben speichern, selbst wenn der Nutzer die Daten gar nicht an die Webseite übermittelt. Mit einer Technik namens Session-Replay lassen sich so zum Beispiel auch die Eingaben in Textfeldern mitlesen, die der Nutzer überhaupt nicht abgeschickt hat.
Datenschutz-Funktionen der Dienste mangelhaft
Drei Forscher der Universität Princeton in den USA haben nun versucht, zu quantifizieren, auf wie vielen Webseiten diese Technik im Einsatz ist. Dazu testeten Sie mit den Skripten der beliebtesten Tracking-Firmen, die Session-Replay anbieten. Dabei kam heraus, dass von den laut Alexa meistbesuchten 50.000 Webseiten mindestens 482 ein oder mehr Skripte der Fimen Clicktale, FullStory, Hotjar, UserReplay, SessionCam, Smartlook oder der großen russischen Suchmaschine Yandex einsetzen. Sie schätzen, dass die Dunkelziffer viel höher ist, ihnen aber nicht alle Seiten ins Netz gingen weil Session-Replay oft nicht bei jedem Besucher aktiv ist.
Zwar bieten die meisten dieser Firmen Möglichkeiten an, private Daten von der Erfassung auszuschließen, dabei kommt es aber immer wieder zu Fehlern. Die Forscher fanden zum Beispiel oft Passwörter, obwohl diese explizit nicht erfasst werden sollten. Dazu kommt, dass Nutzer ab und zu Dinge aus ihrer Zwischenablage aus Versehen in Textfelder kopieren. Ist Session-Replay im Einsatz, werden diese Daten erfasst, auch wenn der Nutzer sie sofort wieder löscht. Und auch Daten, die der Nutzer nicht eingegeben hat, aber von der Webseite angezeigt werden, landen in den Händen der Datensammler. Fazit der Forscher: Laufen entsprechende Skripte, kann man sich nicht darauf verlassen, dass Daten nicht aufgezeichnet werden.
Dienstanbieter untergraben SSL-Verschlüsselung Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Session-Replay+Scripts https://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberespionage https://www.scoop.it/t/securite-pc-et-internet/?&tag=Privacy https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/

|
Scooped by
Gust MEES
October 30, 2017 1:55 PM
|

|
Scooped by
Gust MEES
September 16, 2017 11:05 AM
|

|
Rescooped by
Gust MEES
from Social Media and its influence
December 5, 2018 7:49 PM
|
Twitter’s been combatting harassment for years. The latest effort: quelling its horde of anonymous, hostile egg accounts. But for many users, Twitter’s abuse problem has long since undermined its value as a platform for creative communication. That’s what makes Mastodon—a free, open-source, and increasingly popular six-month-old Twitter alternative—so intriguing.
Mastodon has created a diverse yet welcoming online environment by doing exactly what Twitter won’t: letting its community make the rules. The platform consists of various user-created networks, called instances, each of which determines its own laws. One instance could ban sexist jokes and Nazi logos, while another might practice radically free speech. (In this way, Mastodon is not unlike a network of discretely moderated message boards crossed with a Tweetdeck-like interface.) Users choose for themselves which instance they want to join and select from a host of privacy and anti-harassment settings. Oh, and the character limit is 500, not 140. In essence, Mastodon is an experiment in whether individually moderated communities can make a social network like Twitter more civil. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/social-media-and-its-influence/?&tag=Mastodon

|
Scooped by
Gust MEES
March 18, 2016 1:49 PM
|

|
Scooped by
Gust MEES
March 14, 2016 1:04 PM
|
|

|
Scooped by
Gust MEES
June 29, 2018 6:50 AM
|
Hacker erlangen Zugriff auf Gentoo-Code in Github
Der Quellcode der Linux-Distribution Gentoo könnte kompromittiert sein: Das Entwicklerteam berichtet von einem Hack der gesamten Github-Organisation, in der Repositories abgelegt sind. Davon unberührt sein sollen die Backup-Dateien, die das Team auf eigener Infrastruktur hostet. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Linux

|
Scooped by
Gust MEES
April 25, 2018 3:18 PM
|
A new form of cryptocurrency mining malware uses a leaked NSA-exploit to spread itself to vulnerable Windows machines, while also disabling security software and leaving the infected computer open to future attacks.
The Python-based malicious Monero miner has been uncovered by researchers at security company Fortinet who've dubbed it PyRoMine. It first appeared this month and spreads using EternalRomance, a leaked NSA-exploit which takes advantage of what until a year ago had been an undisclosed SMB vulnerability to self-propagate through networks.
EternalRomance helped spread BadRabbit ransomware and is similar in many ways to EternalBlue, a second leaked NSA exploit which helped fuel WannaCry and NotPetya. Both exploits look for public-facing SMB ports, allowing them to deliver malware to networks.
Researchers discovered the malware was downloadable from a particular web address as a zip file, bundled with Pyinstaller, a program which packages programs written in Python into stand alone executables, meaning there's no need for Python to be installed on the compromised machine.
The malicious code behind PyRoMine appears to have been directly copied from a publicly shared EternalRomance implementation. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=crypto-currency

|
Scooped by
Gust MEES
April 2, 2018 9:44 AM
|
Around 20% of today's top VPN solutions are leaking the customer's IP address via a WebRTC bug known since January 2015, and which apparently some VPN providers have never heard of.
The discovery belongs to Paolo Stagno, a security researcher who goes by the pseudonym of VoidSec, and who recently audited 83 VPN apps on this old WebRTC IP leak.
Stagno says he found that 17 VPN clients were leaking the user's IP address while surfing the web via a browser.
The researcher published his results in a Google Docs spreadsheet. The audit list is incomplete because Stagno didn't have the financial resources to test all commercial VPN clients.
The researcher is now asking the community to test their own VPN clients and send him the results. For this, he set up a demo web page that users must access in their browser with their VPN client enabled. The code running on this page is also available on GitHub, if users want to test the leak locally, without exposing their IP on somebody else's server.
WebRTC leak known since 2015
Stagno's code is based on the WebRTC bug discovered in January 2015 by security researcher Daniel Roesler. Back then, Roesler found that WebRTC STUN servers, which intermediate WebRTC connections, will keep records of the user's public IP address, along with his private IP address, if the client is behind-NAT network, proxy, or VPN client.
The problem was that STUN servers would disclose this information to websites that had already negotiated an WebRTC connection with a user's browser.
Since then, many advertisers and law enforcement agencies have used this WebRTC-related bug to acquire a site's visitor's IP address. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=VPN

|
Scooped by
Gust MEES
November 27, 2017 2:35 PM
|
The average home now has around three connected computers and four smart mobile devices. Hardly surprising, considering that 86 per cent of us check the Internet several times a day or more, and that’s outside of work. Chatting, shopping, banking, playing games, listening to music, booking travel and managing our increasingly connected homes. The risk of cyberattack can be the furthest thing from our mind. Every year, Kaspersky Lab’s experts look at the main cyberthreats facing connected businesses over the coming 12 months, based on the trends seen during the year. For 2018, we decided to extract some top predictions that also have big implications for everyday connected life. So what could the hackers be after in 2018? Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet

|
Scooped by
Gust MEES
November 22, 2017 6:09 PM
|
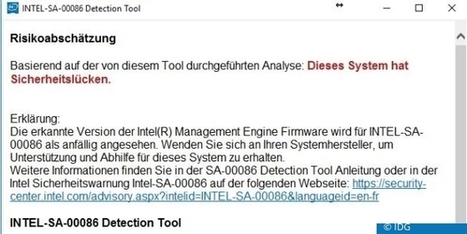
Vereinfacht gesagt: Jeder Desktop-Rechner und jedes Notebook mit einem einigermaßen aktuellen Intel-Prozessor sowie viele Serversysteme sind für die Übernahme durch feindlich gesinnte Angreifer anfällig. Der Angreifer kann zum Beispiel auf dem fremden System seinen Code ausführen, ohne dass der PC-Besitzer das mitbekommt und den gekaperten Rechner auch abstürzen lassen. Mit diesem Gratis-Tool prüfen Sie Ihren Rechner
Mit diesem kostenlosen englischsprachigen Intel-SA-00086 Detection Tool können Besitzer von Rechnern mit Windows 7, 8.1 und 10 sowie mit Linux ihre Rechner daraufhin prüfen, ob die Sicherheitslücke vorhanden ist. Die Windows-Version liegt als ZIP vor, die Linuxversion als tar.gz. Learn more / En savoir plus / Mehr erfahren: https://downloadcenter.intel.com/download/27150

|
Scooped by
Gust MEES
November 22, 2017 3:49 PM
|
Luxembourg, a tiny country with ONLY 590.667 inhabitants (January 2017) in the heart of Europe and one of the smallest countries in the world, WHERE MOST persons don’t even know where to find it on the map, shows up as an international country well known and recognized for its Cyber Security knowledge, as well as its skills in ICT. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/luxembourg-europe/?tag=Digital+L%C3%ABtzebuerg

|
Scooped by
Gust MEES
November 22, 2017 2:35 PM
|

|
Scooped by
Gust MEES
November 5, 2017 5:42 PM
|
Gefahren im Internet sind für Anwender und Unternehmen gleichermaßen gefährlich und resultieren nicht selten in Verlust von Geld oder des Rufes. Daher sollten sich Anwender bewusst sein welche Gefahren es gibt, um diese erfolgreich bekämpfen zu können. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet

|
Scooped by
Gust MEES
October 16, 2017 8:04 AM
|

|
Scooped by
Gust MEES
May 15, 2017 10:34 AM
|
The account details of millions of subscribers to the education platform Edmodo have not only been stolen but witnessed to be for sale on the dark web, according to a post on Motherboard. The platform is used by more than 78 million teachers, students and parents to compose lesson plans, make homework assignments and other tasks.
Breach notification website LeakBase provided Motherboard with a sample of more than two million records, which included usernames, email addresses and hashed passwords.
The good news is that the passwords apparently are hashed with the stealthy bcrypt algorithm, and a string of random characters known as a salt, which likely will make it more difficult for hackers to obtain users' login credentials. And, when staffers at Motherboard attempted to open Edmodo accounts using some of the purloined data, they were unsuccessful as the address was already linked to an Edmodo account, the report explained.
The bad news is that at least a portion of the database is up for sale on the dark web marketplace Hansa for $1,000. The seller, going under the name nclay, said s/he was in possession of 77 million accounts. LeakBase reported that 40 million of those come with an email address.
Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?&tag=DATA-BREACHES http://www.scoop.it/t/securite-pc-et-internet/?&tag=Edmodo+Insecurity

|
Scooped by
Gust MEES
December 16, 2016 2:34 PM
|

|
Scooped by
Gust MEES
March 18, 2016 1:46 PM
|
Yup, I get it: The cloud computing train has left the station and there’s no stopping it now, but it certainly won’t reach Eurostar speeds if there aren’t enough cybersecurity professionals with the right cloud computing knowledge to support this transition.
Given this imbalance, what can CISOs do to support cloud computing business initiatives AND mitigate risk appropriately? Learn more /En savoir plus / Mehr erfahren: http://www.scoop.it/t/securite-pc-et-internet/?tag=Cloud-Security
|



 Your new post is loading...
Your new post is loading...























Data breaches are always bad news, and this one is peculiarly bad.
Gentoo, a popular distribution of Linux, has had its GitHub repository hacked.
Hacked, as in “totally pwned”, taken over, and modified; so far, no one seems to be sure quite how or why.
That’s the bad news.
Fortunately (we like to find silver linings here at Naked Security):
The Gentoo team didn’t beat around the bush, and quickly published an unequivocal statement about the breach.
The Gentoo GitHub repository is only a secondary copy of the main Gentoo source code.
The main Gentoo repository is intact.
All changes in the main Gentoo repository are digitally signed and can therefore be verified.
As far as we know, the main Gentoo signing key is safe, so the digital signatures are reliable.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/securite-pc-et-internet/?&tag=Linux