XKeyscore doesn't just turn somebody's Internet life inside out. It's also a blood hound for sniffing out vulnerable systems.
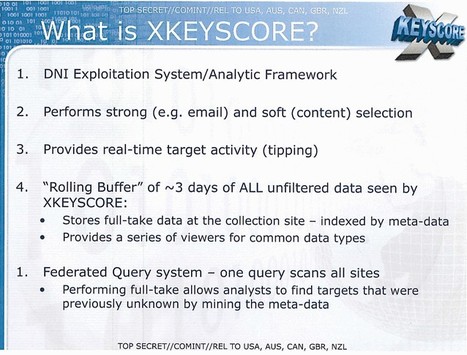
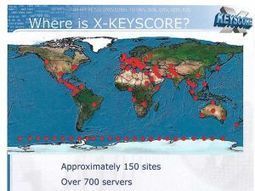
According to Ars Technica's Sean Gallagher, the vulnerability "fingerprints" are added to serve as a filtering criteria for XKeyscore's application engines, comprised of "a worldwide distributed cluster of Linux servers attached to the NSA's Internet backbone tap points."
This turns XKeyscore into a passive port scanner, Gallagher writes, which can be used to search for network behavior on systems that match the NSA TAO's profiles for exploits or for systems already exploited by malware that the TAO can then take advantage of.



 Your new post is loading...
Your new post is loading...









Dem NDR und WDR ist es eigenen Aussagen nach gelungen, einen Teil des Quellcodes des NSA-Tools 'XKeyscore' zu analysieren. Was die Analyse ergibt, lässt einem die Haare zu Berge stehen.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=NSA