 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
December 17, 2018 12:10 PM
|
A New York Times investigation has found that apps such as GasBuddy and The Weather Channel are among at least 75 companies getting purportedly “anonymous” but pinpoint-precise location data from about 200 million smartphones across the US.
They’re often sharing it or selling it to advertisers, retailers or even hedge funds that are seeking valuable insights into consumer behavior. One example: Tell All Digital, a Long Island advertising firm, buys location data, then uses it to run ad campaigns for personal injury lawyers that it markets to people who wind up in emergency rooms.
The Times reviewed a database holding location data gathered in 2017 and held by one company, finding that it held “startling detail” about people’s travels, accurate to within a few yards and in some cases updated more than 14,000 times a day. Several of the businesses whose practices were analyzed by the Times claim to track up to 200 million mobile devices in the US.
The data being sold is supposedly anonymous, as in, not tied to a phone number. The Times could still easily figure out who mobile device owners were through their daily routines, including where they live, where they work, or what businesses they frequent. Learn more / En savoir plus / Mehr erfahren: https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/ https://www.scoop.it/t/securite-pc-et-internet/?&tag=tracking https://www.scoop.it/t/securite-pc-et-internet/?&tag=Privacy https://www.scoop.it/t/securite-pc-et-internet/?&tag=Big+Data

|
Scooped by
Gust MEES
May 17, 2018 5:17 PM
|
A company that collects the real-time location data on millions of cell phone customers across North America had a bug in its website that allowed anyone to see where a person is located -- without obtaining their consent.
US cell carriers are selling access to your real-time phone location data
The company embroiled in a privacy row has "direct connections" to all major US wireless carriers, including AT&T, Verizon, T-Mobile, and Sprint -- and Canadian cell networks, too.
Earlier this week, we reported that four of the largest cell giants in the US are selling your real-time location data to a company that you've probably never heard about before.
The company, LocationSmart, is a data aggregator and claims to have "direct connections" to cell carriers to obtain locations from nearby cell towers. The site had its own "try-before-you-buy" page that lets you test the accuracy of its data. The page required explicit consent from the user before their location data can be used by sending a one-time text message to the user. When we tried with a colleague, we tracked his phone to a city block of his actual location.
But that website had a bug that allowed anyone to track someone's location silently without their permission.
"Due to a very elementary bug in the website, you can just skip that consent part and go straight to the location," said Robert Xiao, a PhD student at the Human-Computer Interaction Institute at Carnegie Mellon University, in a phone call.
"The implication of this is that LocationSmart never required consent in the first place," he said. "There seems to be no security oversight here."
The "try" website was pulled offline after Xiao privately disclosed the bug to the company, with help from CERT, a public vulnerability database, also at Carnegie Mellon.
Xiao said the bug may have exposed nearly every cell phone customer in the US and Canada, some 200 million customers. Learn more / En savoir plus / Mehr erfahren: https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/ https://www.scoop.it/t/securite-pc-et-internet/?&tag=tracking https://www.scoop.it/t/securite-pc-et-internet/?&tag=Privacy https://www.scoop.it/t/securite-pc-et-internet/?&tag=Big+Data

|
Scooped by
Gust MEES
April 20, 2018 3:33 PM
|
Spätestens seit dem Cambridge-Analytica-Skandal stehen viele Menschen Facebook skeptisch gegenüber. Wie Forscher nun herausgefunden haben können beim "Login mit Facebook" Skripte von Drittfirmen die Facebook-Identität des Besuchers nachverfolgen.
Wenn ein Internet-Nutzer auf einer Webseite die Funktion "Login mit Facebook" verwendet, gibt er der Webseite, auf der er sich befindet, unter Umständen Zugriff auf sein öffentliches Facebook-Konto. Forscher der Princeton-Universität in den USA warnen nun davor, dass auf dieser Webseite eingebettete Skripte von Dritten ebenfalls Zugriff auf diese Daten haben. Laut den Forschern sammeln Tracker so die Informationen der Webseitenbesucher – in den meisten Fällen wohl ohne dass die betroffene Webseite davon Kenntnis hat. Derartige Scripte fanden sie auf 434 der eine Million meistbesuchten Seiten im Netz.
Die meisten der Dritt-Skripte fragen den Facebook-Namen und die E-Mail-Adresse des Besuchers ab, der sich über Facebook auf der Seite anmeldet. Zwar ist die ID, welche die Skripte abgreifen, erst einmal auf die Anmelde-Routine der besuchten Webseite beschränkt; wie die Forscher zeigen, lassen sich darüber allerdings die öffentlichen Facebook-Informationen des Besuchers extrahieren. Dazu gehört dessen Facebook-Name und sein Profilbild. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Facebook https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/

|
Scooped by
Gust MEES
February 19, 2018 9:40 AM
|
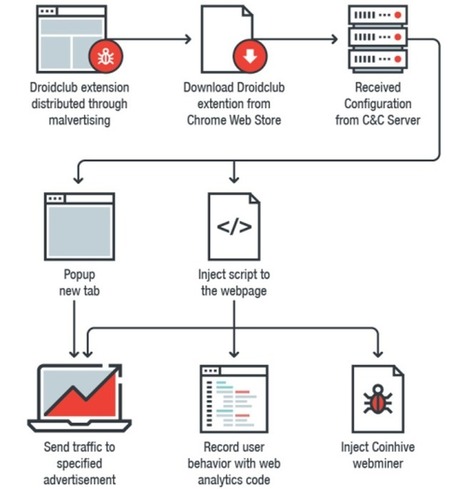
Google has removed 89 malicious extensions from the Chrome Web Store that have been installed on over 420,000 browsers, turning them into Monero-mining slaves and loading a tool to record and replay what their owners do on every website they visit.
Researchers at Trend Micro dubbed the family of malicious extensions Droidclub and discovered they included a software library with so-called "session-replay scripts" used by online analytics firms.
Princeton's Center for Information Technology in November drew attention to the increasing use of session-replay scripts by third-party analytics firms on high-traffic websites.
The study looked at replay services from Yandex, FullStory, Hotjar, UserReplay, Smartlook, Clicktale, and SessionCam, which were found on nearly 500 popular sites.
The scripts allow a site owner to essentially shoulder-surf their visitors by recording and replaying your "keystrokes, mouse movements, and scrolling behavior, along with the entire contents of the pages you visit".
But instead of allowing a site owner to record and play back what users do on one site, Droidclub extensions allow the attacker to see what victims do on every single site they visit. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberespionage https://www.scoop.it/t/securite-pc-et-internet/?&tag=Privacy https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/ https://www.scoop.it/t/securite-pc-et-internet/?&tag=Session-Replay+Scripts
|

|
Scooped by
Gust MEES
August 9, 2018 3:47 AM
|
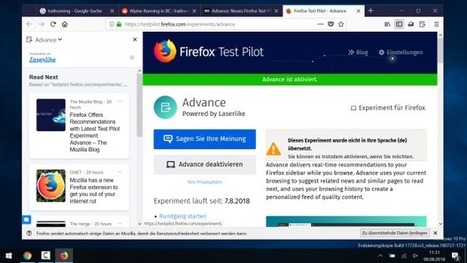
Das Tracking wird über die US-Firma Laserlike abgewickelt. Damit die Empfehlungen in der Seitenleiste auch passen, ist der umfangreiche Zugriff auf Daten, etwa den Browser-Verlauf und die aktuell geöffneten Seiten, nötig. Außerdem sammelt Laserlike IP-Adresse, Zugriffszeiten und Verweildauer auf Webseiten.
Im Rahmen von Test-Pilot tracken Laserlike und Mozilla noch Daten zur Nutzung von Advance, etwa Verweildauer auf empfohlenen Seiten oder Informationen zum Betriebssystem. Was man Mozilla zugute halten muss: Sie verschweigen das Thema Tracking nicht und bauen einen Schalter ein, um Advance pausieren zu lassen.
Auch im Privatmodus oder mit eingeschaltetem Tracking-Schutz funktioniert die Erweiterung nicht. Wer möchte, kann die übermittelten Daten einsehen und löschen. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=tracking

|
Scooped by
Gust MEES
April 26, 2018 2:47 PM
|
Forscher der Princeton University haben kürzlich ein anspruchsvolles Tool entdeckt, dass den Namen „Session-Replay Script“ trägt. Damit sind Berichte über das User-Verhalten selbst bis ins kleinste Detail möglich. Die eingebetteten Code-Schnipsel beobachten und verfolgen jede Interaktion eines Webseitenbesuchers mit der Webseite in Echtzeit. Es ist so, als ob ihm jemand beim Surfen über die Schulter sieht. Anders ausgedrückt ermöglichen diese „Screen Recordings“ das Aufzeichnen jeder Tastatureingabe, jeder Mausbewegung oder jedes Page Scrollings. Alles wird zusammen mit dem Content der Webseite zu einem Paket geschnürt und an Third-Party Server – also an Dritte – zur Analysierung geschickt.
Wir haben die Session-Replay Scipts von sieben der beliebtesten Anbieter solcher Tools untersucht. Das Ergebnis: 482 der weltweit 50.000 meistbesuchten Webseiten benutzen eines der Scripte. Sicherlich ist das nur ein winziger Teil des Internets, wahrscheinlich liegt die tatsächliche Zahl der im Gebrauch befindlichen Scripts weitaus höher.
Was sind die Risiken von Session-Replay Scripts?
Eigentlich sind die Scripts für legitime Anwendungszwecke gedacht. Dazu gehört beispielsweise das Verstehen, wie die User mit der eigenen Webseite zurechtkommen oder das Aufspüren von unverständlichen Abschnitten. Der Einsatz von Session-Replay-Scripts kann aber profunde Auswirkungen auf die Privatsphäre und die Sicherheit haben. Am wichtigsten ist die Tatsache, dass so ein Script nicht zwischen sensiblen und profanen Daten unterscheidet. Ohne angemessene Sicherheitsmaßnahmen können sensible Nutzerdaten preisgegeben werden, wie Login-Daten, Kreditkartendaten oder Informationen zum Gesundheitszustand. Außerdem tracken die Scripts Informationen, die in Echtzeit in ein Feld eingegeben werden, ohne dass sie schon an den Server übermittelt sind – das Aufzeichnen von eigentlich gelöschten Eingaben ist damit möglich.
Weiterhin beabsichtigen die Scripts das Aufzeichnen und Abrufen von individuellen Browser Sessions. Anonymität kann dadurch nicht gewährleistet werden. Aus dem vorangegangenen Whitepaper geht hervor, dass einige Provider sogar echte Namen einzelnen User-Sessions zuordnen. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Session-Replay+Scripts https://www.scoop.it/t/securite-pc-et-internet/?&tag=tracking

|
Scooped by
Gust MEES
March 4, 2018 10:01 AM
|
As location-aware advertising goes mainstream—like that Jack in the Box ad that appears whenever you get near one, in whichever app you have open at the time—and as popular apps harvest your lucrative location data, the potential for leaking or exploiting this data has never been higher.
It’s true that your smartphone’s location-tracking capabilities can be helpful, whether it’s alerting you to traffic or inclement weather. That utility is why so many of us are giving away a great deal more location data than we probably realize. Every time you say “yes” to an app that asks to know your location, you are also potentially authorizing that app to sell your data.
Dozens of companies track location and/or serve ads based on this data. They aim to compile a complete record of where everyone in America spends their time, in order to chop those histories into market segments to sell to corporate advertisers.
Marketers spent $16 billion on location-targeted ads served to mobile devices like smartphones and tablets in 2017. That’s 40% of all mobile ad spending, research firm BIA/Kelsey estimates, and it expects spending on these ads to double by 2021.
The data required to serve you any single ad may pass through many companies’ systems in milliseconds—from data broker to ad marketplace to an agency’s custom system. In part, this is just how online advertising works, where massive marketplaces hold ongoing high-speed auctions for ad space. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=tracking https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/ https://gustmees.wordpress.com/2014/03/05/often-asked-questions-are-there-cyber-security-dangers-with-apps-and-whats-about-privacy/

|
Scooped by
Gust MEES
January 29, 2018 2:39 PM
|
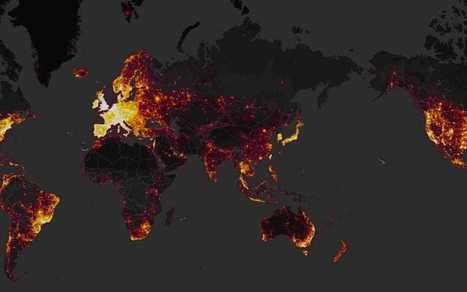
A secretive special air service base has been inadvertently revealed by a fitness app that has created a heatmap of running routes around the country.
A SAS base in Hereford, along with a nuclear deterrent naval base and the government's spy agency GCHQ has been placed on a heatmap of Strava's customers, including the profiles of several people who regularly run to-and-from the highly sensitive buildings.
The buildings appear on a global, interactive map created by Strava, which is an app that allows users to track cycling or running speeds and distances and share them with friends. But unbeknown to many of its users, Strava has used their location data to in a worldwide heatmap including three trillion coordinates, titled "Where We Play".
"When sensitive sites, such as the GCHQ, are quite literally highlighted by GPS activity, it raises concern not only for the individual connected to the device, but the institution as a whole. The UK’s security services must be hyper-aware of what they’re sharing – regardless of what may be labelled as ‘excluded’ within the device. If a device or application has the capability to share location in any respect, it signifies a breach in security protocols."
Learn more / En savoir plus / Mehr erfahren: https://gustmees.wordpress.com/2012/11/05/naivety-in-the-digital-age/ https://www.scoop.it/t/securite-pc-et-internet/?&tag=wearables
|



 Your new post is loading...
Your new post is loading...










A New York Times investigation has found that apps such as GasBuddy and The Weather Channel are among at least 75 companies getting purportedly “anonymous” but pinpoint-precise location data from about 200 million smartphones across the US.
They’re often sharing it or selling it to advertisers, retailers or even hedge funds that are seeking valuable insights into consumer behavior. One example: Tell All Digital, a Long Island advertising firm, buys location data, then uses it to run ad campaigns for personal injury lawyers that it markets to people who wind up in emergency rooms.
The Times reviewed a database holding location data gathered in 2017 and held by one company, finding that it held “startling detail” about people’s travels, accurate to within a few yards and in some cases updated more than 14,000 times a day. Several of the businesses whose practices were analyzed by the Times claim to track up to 200 million mobile devices in the US.
The data being sold is supposedly anonymous, as in, not tied to a phone number. The Times could still easily figure out who mobile device owners were through their daily routines, including where they live, where they work, or what businesses they frequent.
Learn more / En savoir plus / Mehr erfahren:
https://gustmees.wordpress.com/2013/12/21/privacy-in-the-digital-world-shouldnt-we-talk-about-it/
https://www.scoop.it/t/securite-pc-et-internet/?&tag=tracking
https://www.scoop.it/t/securite-pc-et-internet/?&tag=Privacy
https://www.scoop.it/t/securite-pc-et-internet/?&tag=Big+Data