 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
March 20, 2014 9:41 AM
|
A shake-up is coming to the mobile security industry, and it will happen when Google begins to secure its Android environment, David Duncan, CMO of Webroot, says.
When you look at most of the mobile apps, you accept the application and its privileges settings, and there is very little ability for you to customise those settings, so you either agree or disagree.
App developers are trying to monetise their apps, because remember, most of these are being sold for $1.99 or they're free, so the only way that they are going to make money is collecting and harvesting data, and selling it to a data house, who in turn is going to sell it to advertisers.
Learn more:
- http://gustmees.wordpress.com/2014/03/05/often-asked-questions-are-there-cyber-security-dangers-with-apps-and-whats-about-privacy/
- http://www.scoop.it/t/apps-for-any-use-mostly-for-education-and-free

|
Scooped by
Gust MEES
January 15, 2014 10:31 AM
|
De plus en plus d’employés emmènent leurs appareils au travail et se connectent sur le réseau de l’entreprise.

|
Scooped by
Gust MEES
July 30, 2013 12:55 PM
|
Summer 2013 App Reputation Report to examine the hidden behaviors behind free and paid mobile apps The cloud-based, fully automated Appthority App Risk Management Service performed static, dynamic and behavioral app analysis on the 400 most popular free and paid apps on the iOS and Android platforms. Appthority analyzed each app for particular behaviors within a test environment . Highlights from the App Reputation Report are: - Overall, 83% of the most popular apps are associated with security risks and privacy issues. - iOS apps exhibited more risky behaviors than Android apps. 91% of iOS apps exhibit at least one risky behavior, as compared to 80% of Android apps. - 95% of the top free apps and 77.5% of the top paid apps exhibited at least one risky behavior. - 78% of the most popular free Android apps identify the user's ID (UDID). - Even though Apple prohibits its developers from accessing the UDID, 5.5% of the tested iOS apps still do. - 72% of the top free apps track for the user's location, compared to 41% of paid apps. - Although paid apps already generate revenue when downloaded, 59% of paid iOS and 24% of paid Android apps still support in-app purchasing. - Furthermore, 39% of paid iOS and 16% of paid Android apps still share data with ad networks.

|
Scooped by
Gust MEES
May 14, 2013 5:07 PM
|
By now, most everyone has heard the story: on April 23rd, the AP’s twitter account was “hacked.” The tweet, which was a fairly obviously fake, still managed to send Wall Street into a panic. The Dow Jones Industrial Average dropped 145 points in 2 minutes.
So why is this important? It highlights the reality of the threat landscape.
The point of the story is that mobile security isn’t just about protecting you from viruses. Threats don’t only come in the form of malicious applications that one inadvertently “sideloads” onto his or her device. Mobile security is also about making sure your data is protected. It doesn’t matter whether the economic climate is good or bad, there is always a market for fraud. The marketplace for carding is growing and will continue to grow. And as the engineers behind these types of attacks get smarter and smarter, we can only expect to see them more and more often.

|
Scooped by
Gust MEES
May 2, 2013 12:32 PM
|
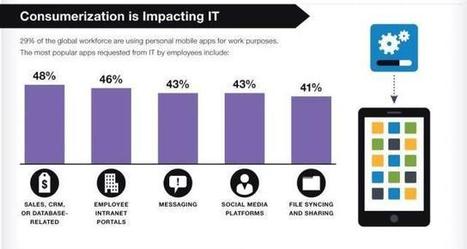
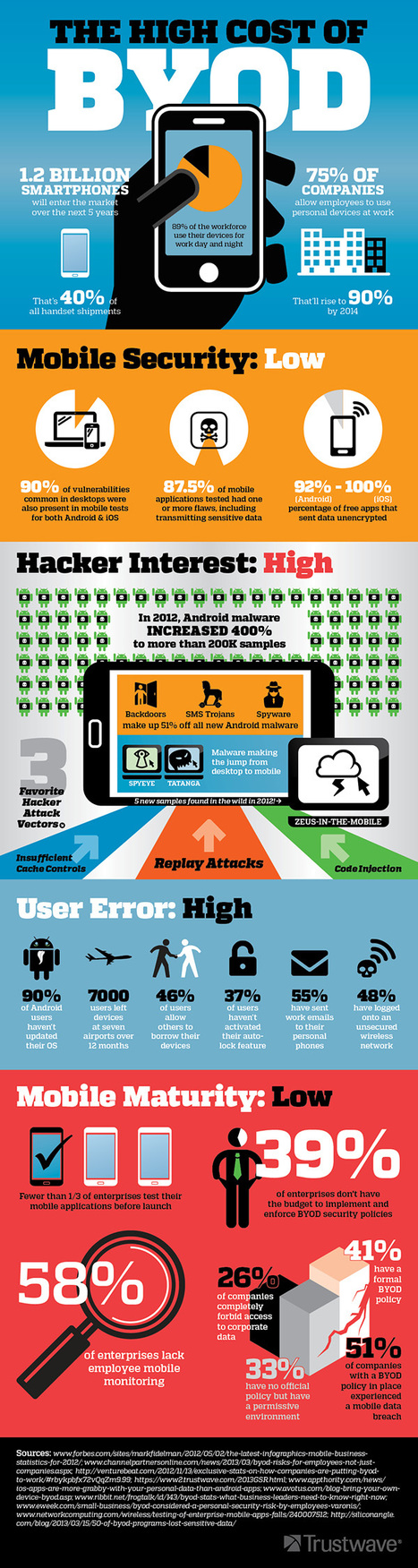
Businesses today are embracing BYOD- 75% of businesses let employees use their own devices to access the network. What threats are lurking behind this mobile revolution?

|
Scooped by
Gust MEES
April 26, 2013 7:32 AM
|
Symantec helps consumers and organizations secure and manage their information-driven world.

|
Scooped by
Gust MEES
April 16, 2013 7:27 AM
|
Laut einer Studie von NQ Mobile hat sich die Anzahl der Malware 2012 gegenüber 2011 verdreifacht. Im vergangenen Jahr gab es über 65.000 Schadprogramme.

|
Scooped by
Gust MEES
April 15, 2013 9:21 AM
|
Mobile service provider NQ Mobile today released a study of malware covering 2012, using data gathered from the company's Security Labs. NQ’s data indicates that Android is a big risk for malware, but iOS has also recently come under fire for free apps that leak more personal data than on other platforms. Overall, mobile security is likely to be a growing concern, and one that could potentially become more complicated as the pace of improvements to mobile tech increases and our usage of those devices grows higher still. ===> For now, common sense is probably the best defense against security threats, but a more unified Android platform would help to limit malware problems as well as significantly improve developers’ lives. <===

|
Scooped by
Gust MEES
March 8, 2013 11:53 AM
|
Bringing your own device to work may be beneficial to the worker, but what about when personal citizen data gets loaded on to such devices? British authorities are firing off the warning flares. The ICO this week published its latest guidance note [PDF] on some of the risks that employers face when allowing personal devices into the enterprise. While BYOD is on the rise in the U.K., employers must still remember that the Data Protection Act—which stems from a 1995 European directive—still applies to these devices.

|
Scooped by
Gust MEES
February 18, 2013 3:34 PM
|
The Bring Your Own Device phenomenon is reshaping the way IT is purchased, managed, delivered, and secured. Our editors and analysts will delve into what it means, the key products involved, how to handle it, and where it’s going in the future.
BYOD is creating new challenges for IT. The top two sources of frustration were onboarding and then supporting the increasing number and variety of personal devices, far outranking even security concerns. The survey also found that IT is increasingly losing control of mobility budgets as departments assume greater responsibility for mobile initiatives. The number of enterprises in which IT manages the mobility spend has dropped to 48 percent, down from 53 percent in 2011. Forty (40) percent of companies' mobility budgets are now managed by non-IT departments.

|
Scooped by
Gust MEES
December 27, 2012 12:41 PM
|
Spoofing, banking attacks, authentication flaws, and more top the list of 2012's biggest mobile security headaches

|
Rescooped by
Gust MEES
from ICT Security-Sécurité PC et Internet
December 11, 2012 5:56 AM
|
Mobile Device Security: What Senior Managers Should Know
Next-generation mobile devices like iPads and Android phones can do wonders for mobile workers and drive productivity and innovation in business. However, new devices bring increased cost of administration, risk of data loss and reputation damage if they aren’t managed correctly.
This article provides clear, practical guidance on how you can make sure mobile ===> devices are a benefit rather than a risk for your organization. <=== Read more, a MUST: http://www.sophos.com/en-us/security-news-trends/security-hubs/mobile-security/mobile-security-101.aspx
|

|
Scooped by
Gust MEES
March 19, 2014 8:34 AM
|
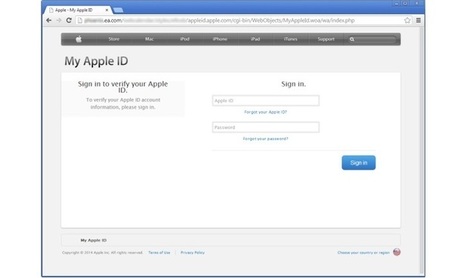
Apple phishing scams are not uncommon, but phishing pages hosted on the website of a major company are certainly worth looking at. Experts have found ...
“The mere presence of old software can often provide sufficient incentive for a hacker to target one system over another, and to spend more time looking for additional vulnerabilities or trying to probe deeper into the internal network.”
The problem with phishing pages hosted on the web servers of reputable companies is that it’s less likely that they’ll be flagged. Furthermore, some users might be tricked into thinking that the pages are legit considering that they’re on a trusted domain.
In this case, the attackers could have made up a story about a collaboration between EA and Apple and that would have truly made the phish efficient.

|
Scooped by
Gust MEES
October 10, 2013 4:53 PM
|
There has been a veritable parade of headlines and news stories in even the mainstream consumer press about the increasing security risk presented by smartphones – a.k.a. the small yet powerful computers that most of us carry around in our pockets. ===> Trend Micro recently released data showing that there will be more than one million malware variants in the market by the end of this year. <===

|
Scooped by
Gust MEES
June 2, 2013 8:57 AM
|
INFOGRAPHIC: Bring Your Own Risk (BYOR)

|
Scooped by
Gust MEES
May 3, 2013 9:51 AM
|
With the growth of BYOD, what security measures can IT take to ensure security of enterprise data – and does MDM have a role?

|
Scooped by
Gust MEES
April 28, 2013 5:18 PM
|
Unfortunately, the "EdTech vs. IT" mindset is all too prevalent in many organizations. Operational IT looks down disdainfully on their users from an ivory tower, viewing them as "threats" to be carefully controlled and monitored. Teachers view the IT department as a bunch of out of touch control freaks who hinder rather than facilitate their work. As a former teacher, I have seen it from both sides.
This sad situation is wrong on many levels. ===> The relationship between IT and users should be a partnership, not a boxing match! <===

|
Scooped by
Gust MEES
April 16, 2013 10:47 AM
|
There are a few snags that can get in the way of implementing BYOD in schools and are worth knowing about before setting out on a BYOD path. 1. Security 2. Safety 3. Affordability 4. Networking and Compatibility

|
Scooped by
Gust MEES
April 15, 2013 2:40 PM
|
There has always been at least some sort of disconnect between how things like mobile learning are taught in a classroom and how things work in the 'real world'.

|
Scooped by
Gust MEES
March 13, 2013 3:57 PM
|
Symantec helps consumers and organizations secure and manage their information-driven world.

|
Scooped by
Gust MEES
March 4, 2013 11:01 AM
|
There are some surprising numbers available that tell a dark story about mobile apps and what they can be doing on your device. By now you've read about malicious apps that leak privacy data, but do you realize how serious it really is? If not, you'd better pay attention to the following statistics gathered by Symantec*. And if you think that Google Play is 100% safe, it isn't. I have some data that yields some shocking results about the number of malicious apps waiting to grab your data.
===> Unfortunately, the playing surface for Internet naughtiness has changed in the past couple of years and you need to know that it's only getting worse. <===

|
Scooped by
Gust MEES
February 15, 2013 12:42 PM
|
People may think their shiny new smartphones and tablets are safe from hackers and malicious software, but that isn't the case, Internet security

|
Scooped by
Gust MEES
January 12, 2013 2:38 AM
|
A new survey has found rising interest in mobile device management platforms to address mobile security threats. Still, few IT professionals indicate a real deployment of the platforms. The survey found that 34 percent of respondents considered mobile devices a serious threat to business, and 55 percent said they were thinking more about the security of corporate smartphones and tablets than they did last year. Despite the attention given to mobile malware and attacks targeting device owners, the biggest threat to enterprises are lost and stolen devices, according to most security experts. ===> The survey found that 10 percent of respondents experienced data leaks following the loss or theft of mobile devices. <===

|
Rescooped by
Gust MEES
from ICT Security-Sécurité PC et Internet
December 18, 2012 1:00 PM
|
An infographic from security-testing company Veracode explores the rise of data breaches and what it could mean for businesses and consumers.
|



 Your new post is loading...
Your new post is loading...







![Survey: Despite Security Incidents, BYOD Worth The Risks [Infographic] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/AmjfVVh3JSRFrcTVEXBUozl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)








![BYOD: Bring Your Own Risk (BYOR) [INFOGRAPHIC] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/y5NTg9uYlSpK6x67Mbb7WDl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)



![The Importance Of Mobile Learning In (And Out Of) The Classroom [Infographic] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/an8zp0xrd2ueChG43lwYQTl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)
![BYOD: Mobility making it easier for insiders to take IP [Infographic] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/7qGVluSAqAo_xdmrGdGXozl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)


![Why You Should Care About Mobile Security [INFOGRAPHIC] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/bCDzCBQu4qMgWJAbygdm2jl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)





When you look at most of the mobile apps, you accept the application and its privileges settings, and there is very little ability for you to customise those settings, so you either agree or disagree.
App developers are trying to monetise their apps, because remember, most of these are being sold for $1.99 or they're free, so the only way that they are going to make money is collecting and harvesting data, and selling it to a data house, who in turn is going to sell it to advertisers.
Learn more:
- http://gustmees.wordpress.com/2014/03/05/often-asked-questions-are-there-cyber-security-dangers-with-apps-and-whats-about-privacy/
- http://www.scoop.it/t/apps-for-any-use-mostly-for-education-and-free