 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
Some types of two-factor authentication (2FA) security can no longer be guaranteed to keep the bad guys out, the FBI is reported to have warned US companies in a briefing note circulated last month.
FBI reporting identified several methods cyber actors use to circumvent popular multi-factor authentication techniques in order to obtain the one-time passcode and access protected accounts.
The simplest and therefore most popular bypass is SIM swap fraud, in which the attacker convinces a mobile network (or bribes an employee) to port a target’s mobile number, allowing them to receive 2FA security codes sent via SMS text.
Naked Security now regularly covers this kind of hack, almost always because it was used to empty people’s bank accounts, steal cryptocurrency from wallets or exchange accounts, or to attack services such as PayPal. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Two-factor+authentication

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
The Supreme Court has approved a rule change that will allow US judges to issue search warrants for accessing computers and devices in any jurisdiction.
That would greatly expand the FBI's hacking capability, say civil liberties groups, who are opposing the planned changes.
Under existing rules, judges can only issue orders within their jurisdiction, often only a few miles across or a few local districts.
But the Justice Dept. argued the changes are necessary to keep up the pace against criminals, who often work across multiple jurisdictions -- even countries.

|
Scooped by
Gust MEES
|
If you control enough of the Tor network, it’s possible to get a kind of bird’s eye view of the traffic being routed through it. It was clear that Tor thought the Carnegie Mellon researchers were responsible. The researchers refused to talk to the press, but a conference spokesperson told Reuters the talk was canceled because the researchers hadn’t cleared the release of their work through their department, the Software Engineering Institute, which is funded by the Defense Department.
At the time, many assumed that the university pulled the plug on the talk because of the gray legal zone it was in, with the researchers casually intercepting Web traffic. But maybe it got pulled because the researchers were revealing a law enforcement technique that the government did not want publicized. If nothing else, it’s highly likely the information the researchers collected about “drug dealers and child pornographers” made its way into law enforcement hands. McCord said he was “unable to comment on the matter.” Carnegie Mellon’s SEI declined comment about the canceled talk and about whether it had provided information from the research to law enforcement.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=TOR

|
Scooped by
Gust MEES
|
November 26, 2013 The FBI Might Do More Domestic Surveillance than the NSA This is a long article about the FBI's Data Intercept Technology Unit (DITU), which is basically its own internal NSA. It carries out its own signals intelligence operations and is trying to collect huge amounts of email and Internet data from U.S. companies -- an operation that the NSA once conducted, was reprimanded for, and says it abandoned. [...] The unit works closely with the "big three" U.S. telecommunications companies -- AT&T, Verizon, and Sprint -- to ensure its ability to intercept the telephone and Internet communications of its domestic targets, as well as the NSA's ability to intercept electronic communications transiting through the United States on fiber-optic cables. [...] After Prism was disclosed in the Washington Post and the Guardian, some technology company executives claimed they knew nothing about a collection program run by the NSA. And that may have been true. The companies would likely have interacted only with officials from the DITU and others in the FBI and the Justice Department, said sources who have worked with the unit to implement surveillance orders. [...]

|
Scooped by
Gust MEES
|
The Wall Street Journal is reporting that the FBI employs a number of high-tech hacker tactics in its efforts to round up information on suspects, including the ability to remotely activate microphones on Android devices and notebook computers,...
Internet security has changed the bureau’s priorities on national security INFOSEC: CYBER CRIME is fast becoming a threat to surpass terrorism, the US Federal Bureau of Investigation (FBI) said on Wednesday, ===> announcing that it has changed its priorities to focus on cyber security as "a national security threat". <===

|
Scooped by
Gust MEES
|
Steven Chabinsky, former top lawyer in the FBI's cybersecurity section, thinks attackers are ahead of us and we need to change our defensive thinking. "When that happens, you know you have a strategy problem on your hands. Had the strategy been working, people would have been executing properly and succeeding. But it isn't. The government and private sector were executing on their plans very well and they didn't improve cybersecurity every year. There was objectively better security, but subjectively, against threat actors, they were gaining momentum. The threat continues to outpace us." Read more, a MUST: http://threatpost.com/en_us/blogs/think-differently-cybersecurity-or-fall-farther-behind-former-fbi-lawyer-says-091912

|
Scooped by
Gust MEES
|
Director Robert Mueller tells Congress that police are 'increasingly unable' to bring criminals to justice because rapid advances in technology thwart surveillance. Read this blog post by Declan McCullagh on Politics and Law. The FBI is renewing its request for new Internet surveillance laws, saying technological advances hinder surveillance and warning that companies should be required to build in backdoors for police. An internal FBI strategy document from 2007 recently posted by Cryptome.org refers to "proposed amendments" to CALEA that would codify the authority of police to "process a subject's communications traffic, including IP/packet-based communications." Read more: http://news.cnet.com/8301-13578_3-57518265-38/fbi-renews-broad-internet-surveillance-push/

|
Scooped by
Gust MEES
|
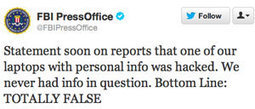
Following yesterday's claim made by AnitSec hackers that they have gotten ahold of a document containing a list of over 12 million Apple iOS devices - including Unique Device Identifiers (UDID), user names, name of device, type of device, Apple Push Notification Service tokens, ZIP codes, cellphone numbers, addresses, and more - after breaking into a computer used by an FBI agent, the agency has issued a resounding denial via Twitter: Read more: http://www.net-security.org/secworld.php?id=13528

|
Scooped by
Gust MEES
|
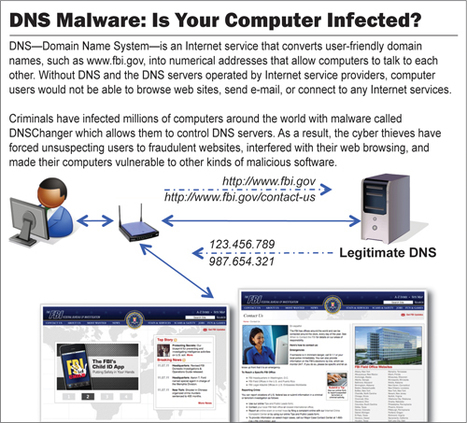
Case against Internet fraud ring reveals millions unknowingly affected worldwide. - Learn about DNSChanger malware and how it can affect your computer
- Check your computer’s DNS settings
- Register as a victim of the DNSChanger malware
Read more: http://www.fbi.gov/news/stories/2011/november/malware_110911

|
Scooped by
Gust MEES
|
The FBI's top cyber cop offered a grim appraisal of the nation's efforts to keep computer hackers from plundering corporate data networks: We're not winning, he said.

|
Scooped by
Gust MEES
|
Hacking group leader, identified as Hector Xavier Monsegur, revealed as FBI mole as five other alleged LulzSec members arrested.
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Two-hundred thousand voter records were stolen from the Illinois board of elections, and a few murky clues point yet again to Russian hackers.

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
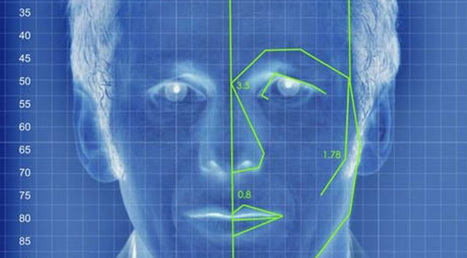
The FBI is building a massive facial recognition database that could contain as many as 52 million images by 2015, including 4.3 million non-criminal images, according to information obtained by th...
Learn more:

|
Scooped by
Gust MEES
|
The feds have caught up to the Silk Road. The underground website long known for drug trafficking was seized by the FBI who also arrested the owner on three criminal counts.
The FBI has become aware of the recent news regarding the ransomware that’s designed to target Mac OS X users. The agency’s Internet Crime...
Via Gust MEES

|
Scooped by
Gust MEES
|
The FBI's top man, Robert S. Mueller III, tackles the internet age. The web has changed the way we learn, work and communicate. But with that convenience we have compromised our security, and widespread use has also left us vulnerable to attack from hostile foreign powers, hackers, spies - and even terrorists.

|
Scooped by
Gust MEES
|
To report potential e-scams, please go the Internet Crime Complaint Center and file a report. Note: the FBI does not send mass e-mails to private citizens about cyber scams, so if you received an e-mail that claims to be from the FBI Director or other top official, it is most likely a scam. If you receive unsolicited e-mail offers or spam, you can forward the messages to the Federal Trade Commission at spam@uce.gov. Read more: http://www.fbi.gov/scams-safety/e-scams?utm_campaign=email-Immediate&utm_content=145512

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
According to authorities, Murmylyuk was part of a gang that beginning in late 2010, gained access to online trading accounts at Scottrade, e*Trade, Fidelity, Charles Schwab, and other brokerage firms and conducted a series of sham trades. Once the hackers controlled the accounts, they used stolen identities to open additional accounts at other brokerage houses, and then initiated "unprofitable and illogical securities trades" that benefited the attackers. They also changed the phone numbers and email addresses on file to prevent victims from being notified of the illegal trades. If convicted, Murmylyuk faces a maximum penalty of five years in prison and a $250,000 fine. Read more...

|
Scooped by
Gust MEES
|
Six Hackers in the United States and Abroad Charged for Crimes Affecting Over One Million Victims
Four Principal Members of “Anonymous” and “LulzSec” Charged with Computer Hacking and Fifth Member Pleads Guilty; “AntiSec” Member also Charged with Stealing Confidential Information from Approximately 860,000 Clients and Subscribers of Stratfor
|



 Your new post is loading...
Your new post is loading...

























Some types of two-factor authentication (2FA) security can no longer be guaranteed to keep the bad guys out, the FBI is reported to have warned US companies in a briefing note circulated last month.
FBI reporting identified several methods cyber actors use to circumvent popular multi-factor authentication techniques in order to obtain the one-time passcode and access protected accounts.
The simplest and therefore most popular bypass is SIM swap fraud, in which the attacker convinces a mobile network (or bribes an employee) to port a target’s mobile number, allowing them to receive 2FA security codes sent via SMS text.
Naked Security now regularly covers this kind of hack, almost always because it was used to empty people’s bank accounts, steal cryptocurrency from wallets or exchange accounts, or to attack services such as PayPal.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/securite-pc-et-internet/?&tag=Two-factor+authentication