 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
A new information stealer malware named 'MetaStealer' has appeared in the wild, stealing a wide variety of sensitive information from Intel-based macOS computers.
MetaStealer, not to be confused with the 'META' info-stealer that saw some popularity last year, is a Go-based malware capable of evading Apple's built-in antivirus tech XProtect, targeting business users. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
A new information-stealing malware has set its sights on Apple's macOS operating system to siphon sensitive information from compromised devices.
Dubbed MacStealer, it's the latest example of a threat that uses Telegram as a command-and-control (C2) platform to exfiltrate data. It primarily affects devices running macOS versions Catalina and later running on M1 and M2 CPUs.
"MacStealer has the ability to steal documents, cookies from the victim's browser, and login information," Uptycs researchers Shilpesh Trivedi and Pratik Jeware said in a new report. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=MacStealer

|
Scooped by
Gust MEES
|
The threat actors' goal is to trick targets into opening malicious files that infect systems with malware that can be used to breach the internal networks of crypto companies to steal large amounts of cryptocurrency, NFTs, or conduct espionage.
In August 2022, Lazarus was seen targeting IT workers with malicious job offers that impersonated Coinbase and targeted users with Windows malware or macOS malware.
In a new report by Sentinel One, the hackers have now switched to impersonating Crypto.com in their phishing attacks using the same macOS malware seen in previous campaigns. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Apple released updates to iOS, iPad OS, and macOS after researchers from Toronto's Citizen Lab found a dangerous, hidden exploit buried in iMessage's code.

|
Scooped by
Gust MEES
|
Apple has released security updates to patch three zero-day vulnerabilities that attackers might have exploited in the wild.
In all three cases, Apple said that it is aware of reports that the security issues "may have been actively exploited," but it didn't provide details on the attacks or threat actors who may have exploited the zero-days.
Exploitable for privacy bypass and code execution
Two of the three zero-days (tracked as CVE-2021-30663 and CVE-2021-30665) impact WebKit on Apple TV 4K and Apple TV HD devices. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
For the past few weeks, macOS Big Sur has suffered from a bug that could cause serious data loss. The bug was introduced in Big Sur 11.2, and it made its way into the 11.3 data.
The bug comes down to the macOS Big Sur installer not checking if the Mac has the required free space available to carry out an upgrade. The upgrade runs into problems, and if that isn't bad enough, if the user's Mac was encrypted using FileVault, then the user is locked out of their data.
Pretty scary stuff.
The bug has been explored extensively by Mr. Macintosh, outlining the problem, some possible solutions, along with a very informative and detailed video. The bug was narrowed down to an evil Goldilocks zone, where users had more than 13GB of free space, but less than 35.5GB.
The video is truly awesome work. Thank you Mr. Macintosh for your work! Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Probleme in macOS Mojave: Apple zieht Browser- und Sicherheits-Update zurück
Nach Nutzerbeschwerden über teils erhebliche Mac-Probleme hat Apple die Bereitstellung zweier sicherheitsrelevanter Updates für macOS 10.14 gestoppt.
Apple hat das Sicherheits-Update 2020-005 sowie die neue Safari-Version 14.0 für macOS 10.14.6 Mojave zurückgezogen. Beide Updates sollten von der in das Betriebssystem integrierten Software-Aktualisierung in dieser macOS-Version nicht länger zum Download angeboten werden, auch Webseiten mit Download-Links wurden entfernt. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
The Lazarus group, which has been named as one of North Korea's state-sponsored hacking teams, has been found to be using new tactics to infect macOS machines.
Dinesh_Devadoss, a threat analyst with anti-malware merchant K7 Computing, took credit for the discovery and reporting of what is believed to be the Lazarus group's first piece of in-memory malware on the Apple operating system.
In-memory infections, also known as fileless malware, operate entirely within the host machine's volatile RAM. This allows the software nasty to avoid setting off any antivirus systems that monitor files in storage or otherwise don't regularly scan all of system memory for threats
The malware sample found by Dinesh_Devadoss was dissected this week by Mac security guru Patrick Wardle, who says that the attack is a new spin on the classic Lazarus group tactic for slipping its malware onto the machines of unsuspecting users; by not installing any files during the secondary stage of the attack where the actual malicious activity occurs. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Lazarus+group https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Longtemps épargné par les virus et autres malwares MacOS suscite de plus en plus l'intérêt des cybercriminels et l'écosystème d'Apple est de plus en plus ciblé.
Apple fait l'objet de plus en plus d'attaques sur son écosystème et ces derniers mois, la découverte de menaces et failles vont bon train.
Une des plus importantes failles de ces derniers mois a été mise en avant par le chercheur en sécurité Filippo Cavallarin et concerne le contournement de GateKeeper. Cette faille permet à des attaquants d'exécuter du code à distance sur MacOS sans autorisation préalable de l'utilisateur. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
AppleInsider reports that a vulnerability first disclosed to Apple three months ago remains unpatched and now the security researcher who found it has gone public. Filippo Cavallarin has published details of how the vulnerability enables a user to be tricked into running malicious applications, bypassing the Gatekeeper function in the process.
Gatekeeper is the Apple mechanism that has, since 2012, been enforcing the code signing and verification of application downloads. If a user were to download an app outside of the Mac App Store then Gatekeeper would kick in and prevent it from running without the express consent of the user. In theory anyway.
Cavallarin says that, on macOS X version 10.14.5 (Mojave) and below, it is possible to "easily bypass Gatekeeper in order to execute untrusted code without any warning or user's explicit permission." According to Cavallarin, he contacted Apple February 22 and the vendor is aware of the issue. It was, he says, "supposed to be addressed, according to the vendor, on May 15, but Apple started dropping my emails." As a 90 day disclosure deadline, which he says Apple is aware of, has now passed, Cavallarin has made details of the vulnerability public. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Gatekeeper

|
Scooped by
Gust MEES
|
Depuis la première version de macOS Mojave, le dossier Safari (~/Library/Safari) n’est plus accessible qu’à une poignée d’applications (il était auparavant ouvert à tous les vents). Le Terminal ne peut même pas en afficher le contenu… Le système d’exploitation fournit l’accès à ce dossier à une poignée d’apps (et au Finder).
Jeff Johnson a néanmoins trouvé une faille qui permet à n’importe quel logiciel de regarder de plus près le contenu de ce dossier normalement protégé des regards indiscrets. Le tout, sans avoir besoin des sésames du système ou de l’utilisateur. La vulnérabilité se passe même de boîtes de dialogue d’autorisation. En exploitant ce bug, un malware peut obtenir l’historique de navigation et donc, potentiellement, des informations à caractère privé.
Mieux, ou pire encore, une application ayant reçu l’estampille du notaire de Mojave (une mesure de sécurité inaugurée avec macOS 10.14) pourrait tout de même être en mesure de piocher sans autorisation dans l’historique de Safari. En revanche, une application sandboxée, c’est à dire distribuée sur le Mac App Store, est incapable de tirer partie de cette faille.
Le découvreur a dûment informé Apple de sa découverte, avec tous les détails de la faille. Jeff Johnson a déjà été crédité par le constructeur pour ses trouvailles, et il est probable qu’une future mise à jour de sécurité vienne combler ce bug. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/

|
Scooped by
Gust MEES
|
A German security researcher has published a video over the weekend showing a new zero-day affecting Apple's macOS desktop operating system.
In an interview to German tech site Heise, Linus Henze, the security researcher, says the vulnerability allows a malicious app running on a macOS system to get access to passwords stored inside the Keychain --the password management system built into all macOS distributions.
The exploit is highly efficient because the malicious app doesn't need admin access to retrieve passwords from the user's Keychain file, and can even retrieve the contents of other Keychain files, which store passwords for other macOS users. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/
|

|
Scooped by
Gust MEES
|
Der Sicherheitsforscher Patrick Wardle machte auf der Defcon-Hackerkonferenz in Las Vegas auf mehrere Schwachstellen im Background-Task-Management (BTM) von macOS aufmerksam. Wie aus einem Bericht von Wired hervorgeht, soll es Angreifern damit möglich sein, Apples Warnsystem zu umgehen und so eine persistente Schadsoftware auf einem Mac zu installieren, ohne dass der Benutzer dies mitbekommt. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Une nouvelle version du malware Dridex cible actuellement les Mac pour se propager sur un grand nombre d'ordinateurs.
Le malware Dridex est déjà connu par les utilisateurs de PC Windows, mais c'est la première fois que ce logiciel malveillant s'attaque à macOS. Pour ce faire, les hackers ont changé le mode de fonctionnement pour parvenir à leurs fins. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Security researchers disclosed today a new vulnerability in Apple's macOS Finder, which makes it possible for attackers to run arbitrary commands on Macs running any macOS version up to the latest release, Big Sur.
Zero-days are publicly disclosed flaws that haven't been patched by the vendor which, in some cases, are also actively exploited by attackers or have publicly available proof-of-concept exploits.
The bug, found by independent security researcher Park Minchan, is due to how macOS processes inetloc files, which inadvertently causes it to run any commands embedded by an attacker inside without any warnings or prompts. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Threat actors enlist compromised WordPress websites in campaign targeting macOS users.
Threat actors known as WildPressure have added a macOS malware variant to their latest campaign targeting energy sector businesses, while enlisting compromised WordPress websites to carry out attacks.
Novel malware, initially identified in March 2020 and dubbed Milum, has now been retooled with a PyInstaller bundle containing a trojan dropper compatible with Windows and macOS systems, according to researchers. Compromised endpoints allow the advanced persistent threat (APT) group to download and upload files and executing commands.
On Wednesday, Kaspersky published its latest findings tied to the APT and malware, which it first discovered and reported on in March 2020. At that time, researchers noted WildPressure targeted Middle East organizations with a C++ version of a trojan it called Milum. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
For more than five years, macOS users have been the targets of a sneaky malware operation that used a clever trick to avoid detection and hijacked the hardware resources of infected users to mine cryptocurrency behind their backs
Named OSAMiner, the malware has been distributed in the wild since at least 2015 disguised in pirated (cracked) games and software such as League of Legends and Microsoft Office for Mac, security firm SentinelOne said in a report published this week.
"OSAMiner has been active for a long time and has evolved in recent months," a SentinelOne spokesperson told ZDNet in an email interview on Monday.
"From what data we have it appears to be mostly targeted at Chineses/Asia-Pacific communities," the spokesperson added. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
MacOS is thought of as more secure than Microsoft’s Windows, but the amount of malware targeting Apple’s operating system is growing. Apple has taken steps to mitigate malware on macOS through a process called notarization—but even this can be bypassed by new and improved adware, a security researcher has discovered.
The adware campaign uses notarized malware, meaning it was scanned and "approved" by Apple and will run on Catalina and Big Sur, security researcher Patrick Wardle has found. “As far as I know, this is the first time hackers have been able to abuse Apple's new notarization,” Wardle told me. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
The Lazarus hacking group has been caught trying to sneak a new ‘fileless’ Trojan on to Apple macOS computers disguised as a fake cryptocurrency trading application.
The discovery was reported by K7 Computing’s Dinesh Devadoss to Mac security expert Patrick Wardle, who immediately spotted similarities to previous attacks.
The first of these, from 2018, was the ‘Apple.Jeus’ malware, which also used a cryptocurrency trading application to lure high-value targets in order to steal cryptocoins.
In October 2019, the hackers retuned with a new backdoor Trojan that spreads using the same approach – a cryptocurrency application posted to GitHub for victims to download.
To make the applications appear trustworthy, both campaigns used the ruse of setting up fake software companies using legitimate certificates.
Both were connected to the suspected North Korean Lazarus Group, widely blamed for big attacks such as WannaCry in 2017 and Sony Pictures in 2014. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Lazarus+group https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
DDoS-for-hire services, also known as DDoS booters, or DDoS stressors, are abusing macOS systems to launch DDoS attacks, ZDNet has learned.
These attacks are leveraging macOS systems where the Apple Remote Desktop feature has been enabled, and the computer is accessible from the internet, without being located inside a local network, or protected by a firewall.
More specifically, the attackers are leveraging the Apple Remote Management Service (ARMS) that is a part of the Apple Remote Desktop (ARD) feature.
When users enable the Remote Desktop capability on their macOS systems, the ARMS service starts on port 3283 and listens for incoming commands meant for the remote Mac.
HUGE "AMPLIFICATION FACTOR"
But sometime this year, cyber-criminals have realized that they can abuse the ARMS service as part of a so-called "DDoS amplification attack." Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Researcher discloses vulnerability in macOS Gatekeeper security feature that allows the execution of malicious code on current version of the OS.
Researcher Filippo Cavallarin disclosed a bug in the macOS security feature Gatekeeper that allows malicious code execution on systems running the most recent version of Mojave (10.14.0).
MacOS Gatekeeper is an Apple security feature that enforces code signing and verifies downloads and apps before users run them. The goal is to eliminate the possibility of malicious files being executed on systems. Gatekeeper requires the user’s consent before opening a file.
“On MacOS X version <= 10.14.5 (at time of writing) it is possible to easily bypass Gatekeeper in order to execute untrusted code without any warning or user’s explicit permission,” wrote Cavallarin, the CEO of Segment, an Italian security firm. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Gatekeeper

|
Scooped by
Gust MEES
|
Google's Project Zero has revealed a "high severity" flaw in the macOS kernel, one which could allow an attacker to make changes to a file without macOS being informed, an issue that could lead to infected files being opened and allowing more malicious activities to become available to abuse. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
There are no permission dialogues for apps in certain folders for macOS Mojave, which allows a malicious app to spy on browsing histories..
A design flaw in Apple’s macOS could allow a malicious application to steal victims’ Safari web browsing history.
The security hole exists in every version of the Mac’s Mojave operating system, including macOS Mojave 10.14.3 Supplemental Update recently released on Feb. 7. That’s according to Mac and iOS developer Jeff Johnson, who disclosed the bug over the weekend.
The issue specifically exists in the fact that there are no permission dialogues for apps in certain folders. While enforcing permissions would mean that these folders could only be accessed by certain apps, the alternative (no permissions required) in the case of ~/Library/Safari means that apps are allowed to look inside it.
And inside the folder is a user’s entire web browsing history (as well as reading list archives, remote notifications, template icons and more). Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/
|



 Your new post is loading...
Your new post is loading...



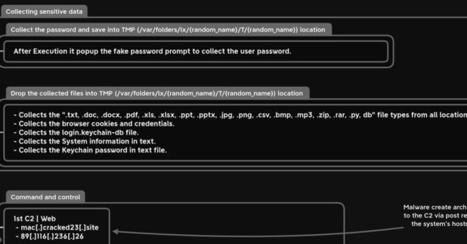



























A new information stealer malware named 'MetaStealer' has appeared in the wild, stealing a wide variety of sensitive information from Intel-based macOS computers.
MetaStealer, not to be confused with the 'META' info-stealer that saw some popularity last year, is a Go-based malware capable of evading Apple's built-in antivirus tech XProtect, targeting business users.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security