 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
The solution for Smeets and his team though is not to pile on extra layers of authentication, but rather to distribute them. And that's where blockchain comes it. Because the blockchain functions via a distributed and encrypted ledger shared across all of a network's users and devices, it creates a network of authentication that is verifiable and not easily hacked. With blockchain implemented, a device cannot access a network unless it is verified through the entire ledger. In this scenario attacks like Mirai become significantly more difficult, if not impossible, because a hacker would need to modify the entire ledger, and not just the credentials of any one device.
Ericcson Research demonstrated a proof-of-concept of this idea at the 2017 Mobile World Congress in Barcelona this past March. The researchers set up a small WiFi network that used blockchain authentication instead of a typical username/password setup. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=blockchain

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Did we learn nothing from Arthur C. Clarke's 1968 sci-fi epic, 2001: A Space Odyssey?
In the film, astronauts on a mission to Jupiter discover that the HAL 9000 artificial intelligence computer that controls and automates all functions on the spacecraft starts seriously glitching. The astronauts get worried, HAL gets paranoid -- yada, yada, yada -- HAL kills everyone on the ship.
Windows as a Service: What's it mean?
Microsoft's decision to unveil a subscription licensing model for Windows 10 for enterprises could be a
READ NOW
The moral of the story is that when lives depend on fully automated systems, it's a good idea to keep an eye on those systems anyway. (And if that's not the moral of the story, it should have been.)
How do you use something that's fully automatic, anyway? What is the responsibility of the "user"? Can we just hand over control to the bots?
Recent events in the news suggest that when it comes to using our automatic products and features, some people are doing it wrong. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Artificial+Intelligence http://www.scoop.it/t/securite-pc-et-internet?q=iot

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Two authors WHO have collaborated already since looong (see below links, please) on Global-Collaboration and learning together about ICT and everything around it, Cyber Security, Privacy , Digital CitiZenship are trying to show YOU, dear readers, THE possibilities on THE How-To to integrate Physical EDUcation within ICT and Social Media...
You will find as well links to software chosen by renowned Universities...

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Vint Cerf is known as a "father of the Internet," and like any good parent, he worries about his offspring -- most recently, the IoT.
"Sometimes I'm terrified by it," he said in a news briefing Monday at the Heidelberg Laureate Forum in Germany. "It's a combination of appliances and software, and I'm always nervous about software -- software has bugs."
The Internet of Things will offer the ability to manage many of the appliances we depend on, acknowledged Cerf, who won the Turing Award in 2004. With its ability to continuously monitor such devices, it also promises new insight into our use of resources, he said.
Devices such as Google's Nest thermostat, for instance, can "help me decide how well or poorly I've chosen my lifestyle to minimize cost and my use of resources -- it can be an important tool," he said.
As with so many technological tools, however, there are plenty of potential downsides. Safety is one of them.
Cerf is now vice president and chief Internet evangelist at Google, but you won't find him enjoying any of the massage chairs the company provides for its employees. "I know they're run by software -- I worry they will fold up on me," he quipped.
As more such appliances are run by software, people will be increasingly reliant on programmers' ability to write good code, he pointed out.
"It's fraught with issues, some technical and some legislative," he said. "Who is liable when an appliance doesn't work the way it should, and what if that's a software question?"
Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Internet+of+Things
http://www.scoop.it/t/securite-pc-et-internet/?tag=Internet+of+things
http://globaleducationandsocialmedia.wordpress.com/2014/01/21/why-is-it-a-must-to-have-basics-knowledge-of-cyber-security-in-a-connected-technology-world/
http://www.scoop.it/t/securite-pc-et-internet/?tag=Cars

|
Scooped by
Gust MEES
|
|

|
Scooped by
Gust MEES
|
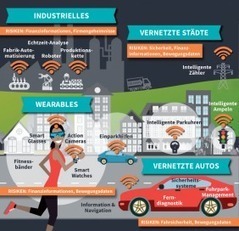
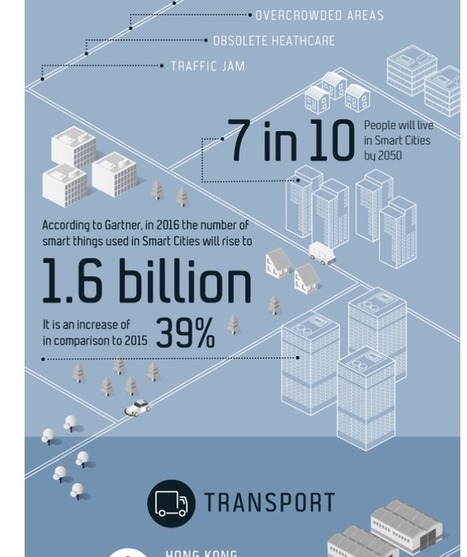
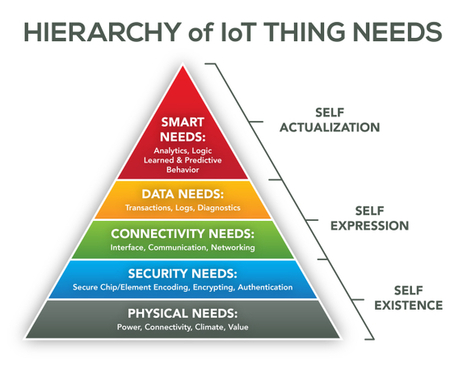
There is no doubt that companies of all shapes and sizes are increasing their spend in internet-of-things (IoT) technology. In fact, IDC projects this to be a $1.4 trillion market by 2021. With the increased spend and demand by consumers for low-price and high-value IoT devices, makers of these connected technologies have put a premium on affordability. The race to the bottom on price has inadvertently created major risks for organizations and consumers, according to PwC’s “Uncovering the Potential of the Internet of Things” report.
The pressure is on, and we see many makers of connected devices that produce IoT products as inexpensively as possible skipping important steps such as the design of security and privacy protections. This is generating significant new risks that are not widely understood during a time when consumers are more concerned about price than privacy and security. Risks include physical, software, encryption and network attacks, all of which could have wide-ranging effects on our daily lives, from taking over a connected car to obtaining sensitive data from a connected home to accessing a private network via a wearable device. Also, there are societal concerns, including getting access to valuable intellectual property, sabotage to companies or governments and espionage. Consumer-focused companies need to ensure they are meeting their customers’ concerns. Simply put, the proper cybersecurity and privacy measures can aid businesses in seeing the full potential of IoT. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=IoT http://www.scoop.it/t/securite-pc-et-internet/?&tag=iot

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
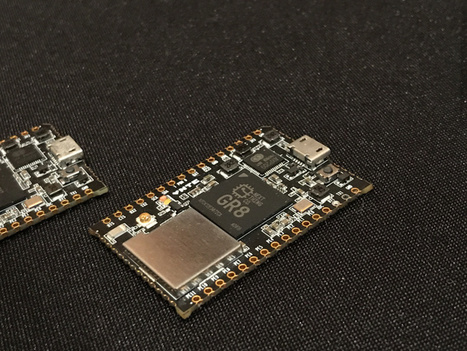
Say you want to create the next generation of voice recognition-enabled, AI-ensmartened, buzzword-laden gadget. The fist thing you need to do is pick a platform. Arduino isn’t powerful enough. The Raspberry Pi works great for prototyping, but going from Pi to production is a many-step process. Next Thing‘s Chip Pro is stepping up to fill the gap with a smart development kit for IoT creators. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Internet+of+Things

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
|



 Your new post is loading...
Your new post is loading...














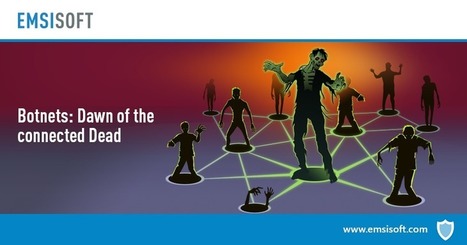











With blockchain implemented, a device cannot access a network unless it is verified through the entire ledger. In this scenario attacks like Mirai become significantly more difficult, if not impossible, because a hacker would need to modify the entire ledger, and not just the credentials of any one device.
Ericcson Research demonstrated a proof-of-concept of this idea at the 2017 Mobile World Congress in Barcelona this past March. The researchers set up a small WiFi network that used blockchain authentication instead of a typical username/password setup.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=blockchain