Bring Your Own Device (BYOD) is more complex than most people know, read further to learn… . .
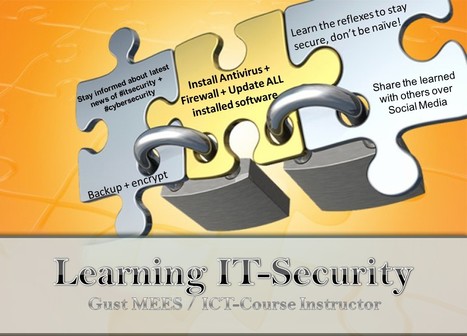
Keywords for this free course: . motivation, engagement, heroes, Security-Scouts, critical thinking, stay out of the box, adapt to new technologies, be aware of the malware, nobody is perfect, knowing the dangers and risks, responsibility, responsibility of School, responsibility of IT-Admin, responsibilities of BYOD users, Apple insecurity, Insecurity of Apps, Principals responsibilities, Mobile Device Management, risks of BYOD, BYOD-Policy, IT-Security Infrastructure, Teacher-Parents Meeting, Cyberwar, Cyberwarfare, Government, Internet-Safety, IT-Security knowledge basics...
The weakest link in the Security Chain is the human! If you don’t respect certain advice you will get tricked by the Cyber-Criminals!
=> NOBODY is perfect! A security by 100% doesn’t exist! <=
Read more:
http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/
Via
Gust MEES



 Your new post is loading...
Your new post is loading...




![4 things you need to know to help your students manage their online reputation [Infographic] | omnia mea mecum fero | Scoop.it](https://img.scoop.it/j7dVyVsW9VcD8NbMbZtXoTl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)





The entrance to GitHub is the most Instagram-able lobby in tech. It's a recreation of the Oval Office, and the mimicry is spot-on---except for the rug. Instead of the arrow-clutching American eagle that graces Obama's office rug, it shows the code-sharing site's Octocat mascot gazing into the digital future, just above the motto: "In Collaboration We Trust."
For more resources on STEM Education visit http://bit.ly/1640Tbl