 Your new post is loading...

|
Scooped by
Marteq
|
CONTENT MARKETING
Many businesses use a Content Management System (CMS) such as WordPress to support content marketing. This allows you to easily upload, edit, and feature new content like blog posts. However, as the most popular CMS, hackers are very familiar with how WordPress functions. If they hack your site they can use it to distribute malware to your users. Needless to say, this can severely damage your reputation.
EMAIL MARKETING
A common hacker tactic is to hijack one of your email accounts and use it to send spam, including fraudulent or virus-infected emails. Most ISPs and many servers have set up spam filters to identify and block spammers based on the originating IP address. Hackers want to take over your site’s email to do their dirty work while protecting themselves.
CUSTOMER RELATIONSHIP MANAGEMENT
Forming strong relationships with your customers is about building trust. Start by installing SSL (Secure Sockets Layer) protocols on your website.This will ensure that sensitive information is not stored or transferred in plain text format; instead, it will be encrypted.
SOCIAL MEDIA MARKETING
While it’s important to keep all your security software up to date, most data breaches occur because of human mistakes. Unauthorized downloads, shared copies, and poor passwords can introduce threats to your network. One channel that requires special vigilance is social media.

|
Scooped by
Marteq
|
"Overall privacy and security of Marketing Automation is a key area for B2Bs to consider. It is important to not only identify existing threats and the way they corrupt entire networks or systems, but also to have a fair assessment of emerging cyber threats along with secure ways to prevent them. When choosing automation for various levels of marketing, it is crucial for B2Bs to demand answers to questions regarding: - Security of owned data during integration,
- Security when using third-party functions,
- Levels of foreseen data loss or threat in event of a breach while using automated tools."

|
Scooped by
Marteq
|
You're saying that CMOs really need to make cybersecurity a top priority?
If you're in a business that doesn't have an awareness of cybersecurity overall, when a crisis comes -- and we all know that a crisis is going to come -- it's going to be on the marketing team to be able to explain it. And it's going to look really bad if it was that marketing team that potentially introduced the backdoor in the first place from something that they built. We all want to be transparent and use martech to remove barriers, to enable feedback loops and make purchasing easier. But we also have to keep that data secure, [given that] marketers are collecting massive amounts of data, including personal information.

|
Scooped by
Marteq
|
IT and marketing are well-partnered in many companies. It is a natural marriage, as IT has the data that marketing uses to find customers and convert their product interest into sales. Despite this partnership, both departments have different starting points and different views on IT security.
In the RSA poll, cyber risk exposure from marketing was a major concern for IT departments, with 75 percent of respondents flagging this as a major weakness. This worry was only shared by 44 percent of marketing respondents. About three-fourths of IT and marketing respondents recognized that “shadow IT” and other workarounds were an operating reality in their companies.

|
Scooped by
Marteq
|
- "Through 2020, 99% of vulnerabilities exploited will continue to be ones known by security and IT professionals for at least one year.
- By 2020, a third of successful attacks experienced by enterprises will be on their shadow IT resources.
- By 2018, the need to prevent data breaches from public clouds will drive 20% of organizations to develop data security governance programs.
- By 2020, 40% of enterprises engaged in DevOps will secure developed applications by adopting application security self-testing, self-diagnosing and self-protection technologies.
- By 2020, 80% of new deals for Cloud Access Security Broker (CASB) technology will be packaged with network firewall, secure web gateway (SWG) and web application firewall (WAF) platforms.
- By 2018, enterprises that leverage native mobile containment rather than third-party options will rise from 20% to 60%.
- By 2019, 40% of IDaaS implementations will replace on-premises IAM implementations, up from 10% today.
- By 2019, use of passwords and tokens in medium-risk use cases will drop 55%, due to the introduction of recognition technologies.
- Through 2018, over 50% of IoT device manufacturers will not be able to address threats from weak authentication practices.
- By 2020, more than 25% of identified enterprise attacks will involve IoT, though IoT will account for only 10% of IT security budgets."

|
Scooped by
Marteq
|
Here are the lessons enterprise leaders of all stripes should take away from these events:
- “Digital dependence” for customers & businesses is real.
- The interconnectedness of the digital economy is difficult to comprehend until something like this happens and we see it play out live by infection timestamps.
- Security is now a customer-facing issue as each widespread attack proves.
- Worldwide financial systems, critical infrastructure, and overall global economic prosperity is under attack from cyberweapons and threat actors.

|
Scooped by
Marteq
|
What is marketing’s role in potentially enabling cyber breaches or preventing them?
Marketing has three roles in the realm of cyber security: 1) the victim, 2) the risk factor, and 3) the brand protector. In the first role, marketers are the targets of hackers. They often can be the individuals who the hackers are conducting reconnaissance on because they are highly visible. Marketers tend to engage in social media, have detailed information on LinkedIn, and in some companies, be visible through press releases and other marketing activities. This makes it easier for the hackers to become aware of marketers and then to observe them. The second role marketers play—unbeknownst to many, is that they are often the cause of the intrusions. Because marketers purchase a lot of technology, much of which operates in the cloud, if they aren’t close with their IT department, new technology can become an unwitting opportunity for hackers.

|
Scooped by
Marteq
|
To help, RSA Security’s CMO, Holly Rollo provided a checklist of five things marketers can do to minimise their exposure to security risks. The first is to increase their cyber awareness and better understand the risk. Rollo’s second piece of advice is to take accountability for the security of your marketing technology by asking the question of both vendors as well as third-party suppliers such as integrators and implementers. It’s also important to make security a key decision factor when choosing vendors.
Another big one is to partner with IT on your roadmap and monitoring strategy. Rollo’s final piece of advice is to advocate or create a breach communication plan.

|
Scooped by
Marteq
|
Whitler: In prior articles, we’ve talked about what cybersecurity is, the degree of threat firms face from an attack, who manages it, and why CEOs/CMOs should care. Let’s assume you’ve convinced firm leaders. What steps can a CMO take to help protect customer data?
Rollo: The basis of a modern marketing engine revolves around a web platform and the supporting systems, marketing/customer databases, automation, operations, analytics tools and connections to CRM, ERP, and a whole host of other systems. There are bells and whistles galore that can be used to capture, score, manage, nurture, clean, append, correlate, analyze, and connect customer and prospect data for the purpose of promoting, selling, enabling selling, syndicating, replicating, or socially promoting anything you can imagine.
We must build our modern marketing infrastructures with security in mind, partnering directly with the CIO or CSO on it. It is important that we drive a conversation about how the IT security teams can better protect the marketing infrastructure and respond in the event of a breach. We must also insist that vendors go through security audits and that we ask as many questions as we can about their ability to protect and defend our data and any possible entry points into our environment that can affect other parts of the business.

|
Scooped by
Marteq
|
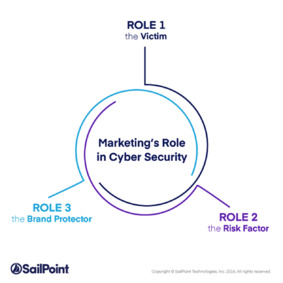
Here’s the situation in a nutshell. Marketing as a function is spending the most amount of money on technology according to 2016 research by IDG; more money than finance, engineering, sales and HR. This is a result of recent technology innovations that have allowed marketers to take advantage of data science to drive ROI and deliver more highly quality results for Sales. Many of those innovations have been delivered by companies who understand that marketing traditionally doesn’t get a lot of IT support, so many if not most of these are delivered as web-based or web-enabled applications. But we aren’t buying one application; we are connecting together say ten of these tools when we go through a new web launch for example. There’s a huge amount of pressure to go fast and we don’t always get the IT support we need, so we outsource, get parts from the company’s shared services, or create shadow IT.
So, there is lots of spending and tools being put together, using mostly cloud and some form of outsourced IT. Meanwhile, the IT security organization is busy protecting the enterprise’s core infrastructure. These teams are working really hard, but only 27% of enterprises say they actively monitor cloud-based infrastructure as part of their security strategy based on our research. And they absolutely can’t monitor and protect systems or applications they don’t know exist. So, who is looking at the security strategy for all of these marketing assets that we just spent all this money to acquire? Yes, security-conscious IT organizations will help us through a security audit for each vendor, but we are connecting the tools together with APIs and the connections are what is concerning. Remember, at some point, all that connects to CRM and ERP, so the modern marketing infrastructure with that marketing automation forms page, it’s a front door to sensitive information.
Realizing this, we as marketing leaders need to do all that we can to be more security-aware and partner with our CIOs and CSOs to be sure we have an end-to-end security strategies for our infrastructure.

|
Scooped by
Marteq
|
Organisations are transforming their security spending strategy in 2017, moving away from prevention-only approaches to focus more on detection and response, according to Gartner, Inc. Worldwide spending on information security is expected to reach $90 billion in 2017, an increase of 7.6 per cent over 2016, and to top $113 billion by 2020. Spending on enhancing detection and response capabilities is expected to be a key priority for security buyers through 2020.

|
Scooped by
Marteq
|

|
Scooped by
Marteq
|
CMOs seldom have a seat at the table in cybersecurity decision-making even though a major breach can have immediate, deep and long-lasting consequences for the brand that the CMO is responsible for.
It puts CMOs in the unfair and untenable position of being held accountable for revenue and other metrics but wielding no authority on an important topic that, if the worst happens, could derail them.
Thinking of the CMO as anything less than a key cybersecurity stakeholder also makes little sense when you consider that engaging customers digitally without compromising sensitive information is at the very heart of the CMO’s mission today.
|
|

 Your new post is loading...
Your new post is loading...



















Overcoming Cyber Security Challenges in Digital Marketing - Relevance
Make no mistake: you MUST secure cybersecurity insurance! Budget it in for 2018.
This news comes to you compliments of marketingIO.com. #MarTech #DigitalMarketing