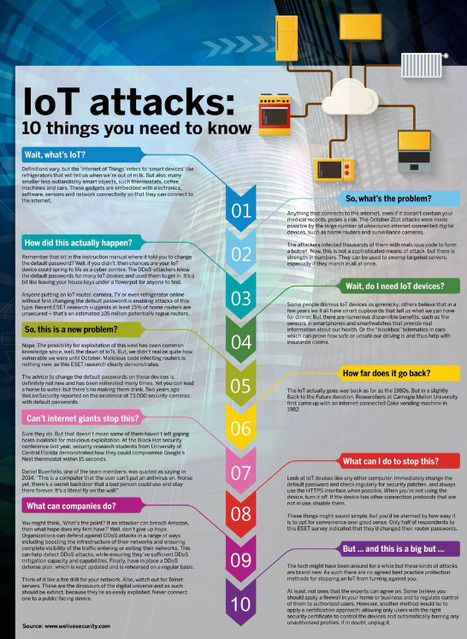
IoT attacks are on the rise. As the technology becomes more relevant to our lives, we take a look at what the state of play is.
Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberattacks
http://www.scoop.it/t/securite-pc-et-internet/?&tag=Amnesia
http://www.scoop.it/t/securite-pc-et-internet/?&tag=Amnesia&tag=BrickerBot
http://www.scoop.it/t/securite-pc-et-internet/?tag=Mirai+Botnet
http://www.scoop.it/t/securite-pc-et-internet/?tag=wearables
http://www.scoop.it/t/securite-pc-et-internet/?tag=SHODAN+Search+Engine
http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Internet+of+Things
http://www.scoop.it/t/securite-pc-et-internet/?tag=smart-TV
http://www.scoop.it/t/securite-pc-et-internet/?tag=Internet+of+things
http://www.scoop.it/t/securite-pc-et-internet/?tag=Cars



 Your new post is loading...
Your new post is loading...








Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/securite-pc-et-internet/?&tag=Cyberattacks
http://www.scoop.it/t/securite-pc-et-internet/?&tag=Amnesia
http://www.scoop.it/t/securite-pc-et-internet/?&tag=Amnesia&tag=BrickerBot
http://www.scoop.it/t/securite-pc-et-internet/?tag=Mirai+Botnet
http://www.scoop.it/t/securite-pc-et-internet/?tag=wearables
https://globaleducationandsocialmedia.wordpress.com/2014/01/21/why-is-it-a-must-to-have-basics-knowledge-of-cyber-security-in-a-connected-technology-world/
http://www.scoop.it/t/securite-pc-et-internet/?tag=SHODAN+Search+Engine
http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Internet+of+Things
http://www.scoop.it/t/securite-pc-et-internet/?tag=smart-TV
http://www.scoop.it/t/securite-pc-et-internet/?tag=Internet+of+things
http://www.scoop.it/t/securite-pc-et-internet/?tag=Cars