Your new post is loading...
 Your new post is loading...
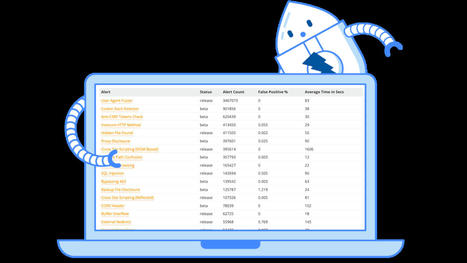
The world’s most widely used web app scanner. Free and open source. Actively maintained by a dedicated international team of volunteers. A GitHub Top 1000 project.
The featured infosec products this month are from: ABBYY, ARMO, Array, AuditBoard, AuthenticID, AwareGO, Code42, Corelight, and more.
They say it “takes a village” to help raise a child… well, it also takes a village to help raise an infosec professional. With so many technologies, techniques, and tools and the need for soft-skills and the ability to navigate different types of relationships, we all need help.
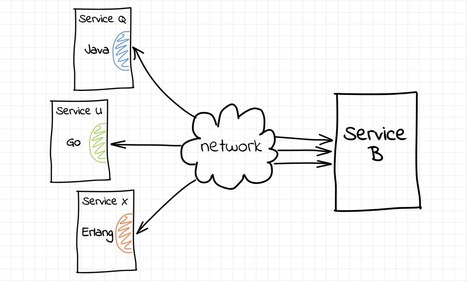
Explaining the ideas of pod, sidecar and service proxy with envoy demo playground.
It is no longer a secret for anyone, Security is a major issue for all companies and of course the management of TLS certificates is one of these issues. However, certificate requests are rarely…
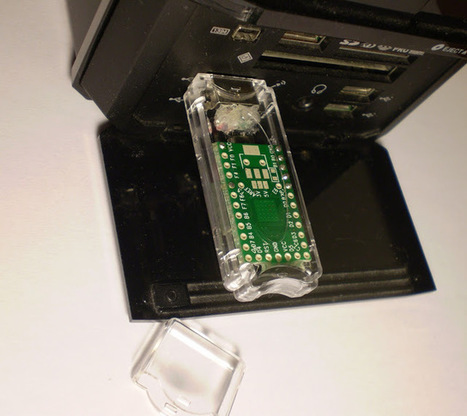
Every time when I get bored from my day job I tend to find some small interesting project that I can do that can give me an instant sense of accomplishment and as the result lift my spirits and improve motivation. So this time I remembered when someone once asked me if they could use Terraform to control their physical network devices and I had to explain how this is the wrong tool for the job.
Finding potential software vulnerabilities from git commit messages
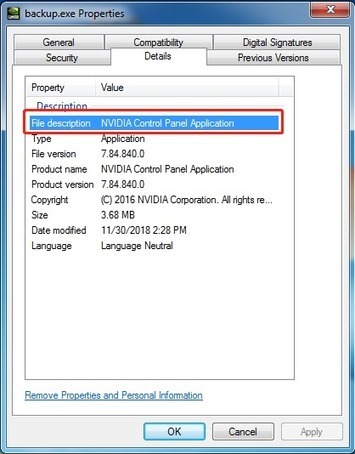
FireEye Managed Defense detected and responded to a FIN6 intrusion at a customer within the engineering industry.
State of Osquery Process Auditing Facebook’s Osquery is a proven, lightweight tool to gather process information from endpoints. Osquery has a concept of “tables”, similar to a database, that provide a SQL interface to structured data. It’s important to understand the 2 different types of tables, normal and event, which operate very differently. Let’s dive …
An algorithmic method to assist in analyzing information at scale.
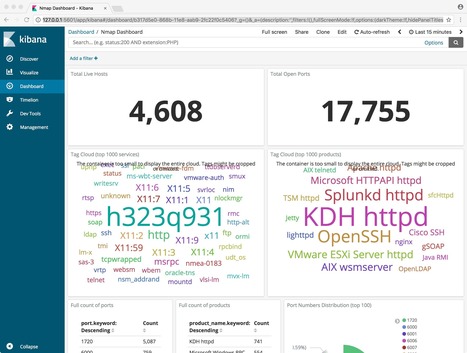
How traditional defensive tools for Offensive security data analysis have advantages over the traditional grep when parsing and analysing data.
|
While the 2022 report from (ICS)2 indicated that Ireland has reduced its cybersecurity skills gap, globally the picture was not so positive.
Infosec/hacking videos recorded by Cooper (@Ministraitor)...
Relax, there's more chance of Babbage coming back to life to hack your system than this flaw being exploited...
Microsoft Open Source: get involved in open source communities, discover projects and ecosystems Microsoft is involved in, and learn about the Microsoft open source program
As Kubernetes becomes the de-facto solution for container orchestration, managed Kubernetes services have popped up everywhere, with cloud providers investing significant effort into their offerings…
When I’ve just started working on this, I thought it would be easy to add SSO to static website, but as it often goes with solving problems on Kubernetes — when you want to solve issue for one…
decent looking diagrams for engineers
This topic for the IT professional lists questions and answers about understanding, deploying, and managing security audit policies.
Interested in securing your enterprise and Active Directory environment? Please visit TrimarcSecurity.com. Sean Metcalf, founder and Principal Consultant for Trimarc, has presented on security attack and defense at several major security conferences including: Black Hat USA (2015, 2016, 2018) BSides Charm (2015, 2016, 2017, 2018) BSides DC (2016) DEF CON (2015, 2016, 2017, 2018) DerbyCo
SANS Digital Forensics and Incident Response Blog blog pertaining to The new version of SOF-ELK is here. Download, turn on, and get going on forensics analysis.
A high-level mind map to summarize all the techniques/tools covered by Peter Kim’s book.
|






 Your new post is loading...
Your new post is loading...