 Your new post is loading...
 Your new post is loading...
Since at least May 2021, stealthy Linux malware called AVrecon was used to infect over 70,000 Linux-based small office/home office (SOHO) routers to a botnet designed to steal bandwidth and provide a hidden residential proxy service.
This allows its operators to hide a wide spectrum of malicious activities, from digital advertising fraud to password spraying.
According to Lumen's Black Lotus Labs threat research team, while the AVrecon remote access trojan (RAT) compromised over 70,000 devices, only 40,000 were added to the botnet after gaining persistence. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Linux
Via Gust MEES
Une grave faille de sécurité affecte le noyau Linux
Sécurité : La faille de sécurité affecte ksmbd, un serveur SMB intégré au noyau de Linux 5.15, et sa note de gravité avoisine le 10, selon la ZDI.
Joyeux Noël à tous les administrateurs de systèmes Linux ! Et en guise de cadeau : une grave faille de sécurité dans le noyau Linux.
C’est la Zero Day Initiative (ZDI), une société de recherche sur les failles zero-day, qui l’a découverte et annoncée juste avant le réveillon.
Cette vulnérabilité pourrait permettre à un attaquant à distance authentifié de divulguer des informations sensibles et d’exécuter du code sur les versions vulnérables du noyau Linux.
Via Gust MEES
Microsoft has continued its analysis of the LemonDuck malware, known for installing crypto-miners in enterprise environments. It makes a strong case for why it is worth removing it from your network.
This group, according to Microsoft, has a well-stocked arsenal of hacking tools, tricks and exploits aimed at one thing: for their malware to retain exclusive access to a compromised network for as long as possible.
While crypto-mining malware could be just a nuisance, LemonDuck attributes suggest the attacker group really do try to own compromised networks by disabling anti-malware, removing rival malware, and even automatically patching vulnerabilities -- a competitive effort to keep rival attackers from feeding off its turf. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/topic/securite-pc-et-internet
Via Gust MEES
A small but complex malware variant is targeting supercomputers worldwide.
Reverse engineered by ESET and described in a blog post on Tuesday, the malware has been traced back to attacks against supercomputers used by a large Asian Internet Service Provider (ISP), a US endpoint security vendor, and a number of privately-held servers, among other targets.
The cybersecurity team has named the malware Kobalos in deference to the kobalos, a small creature in Greek mythology believed to cause mischief.
Kobalos is unusual for a number of reasons. The malware's codebase is tiny but is sophisticated enough to impact at least Linux, BSD, and Solaris operating systems. ESET suspects it may possibly be compatible with attacks against AIX and Microsoft Windows machines, too.
"It has to be said that this level of sophistication is only rarely seen in Linux malware," commented cybersecurity researcher Marc-Etienne Léveillé. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Linux
Via Gust MEES
Partager vos fichier en toute simplicité sur sur un réseau local grâce à NitroShare
Via SebTIC
|
A pervasive cyber-espionage group known as Iron Tiger, believed to be out of China, has updated one of its malware frameworks to attack Linux-based systems.
Researchers at Trend Micro recently discovered that Iron Tiger (aka Emissary Panda or APT27) had added new features to its so called SysUpdate malware family, which allows it to infect Linux platforms in addition to Windows. SysUpdate abuses system services, grabs screenshots, browses and terminates processes, retrieves drive information, executes commands, and can find, delete, rename, upload, and download files as well as peruse a victim's file directory. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Linux
Via Gust MEES
Flaws in networkd-dispatcher, a service used in the Linux world, can be exploited by a rogue logged-in user or application to escalate their privileges to root level, allowing the box to be commandeered, Microsoft researchers said Wednnesday.
It's nice of Redmond to point out these flaws and have them fixed in any affected distributions; the US tech giant is a big user of Linux and relies on the open-source OS throughout its empire. It's just a little perplexing the biz went to all the effort of a big write-up and giving the flaws a catchy name, Nimbuspwn, when countless privilege-elevation holes are fixed in its Windows operating system each month, and we can't recall Microsoft lately making this much of a song and dance over them. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Linux
Via Gust MEES
The Hive ransomware gang now also encrypts Linux and FreeBSD using new malware variants specifically developed to target these platforms.
However, as Slovak internet security firm ESET discovered, Hive's new encryptors are still in development and still lack functionality.
The Linux variant also proved to be quite buggy during ESET's analysis, with the encryption completely failing when the malware was executed with an explicit path.
Via Gust MEES
Microsoft is warning customers about the LemonDuck crypto mining malware which is targeting both Windows and Linux systems and is spreading via phishing emails, exploits, USB devices, and brute force attacks, as well as attacks targeting critical on-premise Exchange Server vulnerabilities uncovered in March.
The group was discovered to be using Exchange bugs to mine for cryptocurrency in May, two years after it first emerged.
Notably, the group behind LemonDuck is taking advantage of high-profile security bugs by exploiting older vulnerabilities during periods where security teams are focussed on patching critical flaws, and even removing rival malware. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/topic/securite-pc-et-internet
Via Gust MEES
Linus Torvalds has kicked off yet another development cycle for the Linux kernel, announcing the release of 5.10-rc1, and this time with an historical twist. The new version of the kernel effectively marks the end of a decade-old feature that has long been made redundant after it was found to cause security bugs.
With the closing of the two-week-long merge window, which precedes the release of every new iteration of the Linux kernel, Torvalds shared his reflections on the Linux kernel mailing list, maintaining that "things seem to have gone fairly smoothly".
The merging window is a key part of any new kernel release process, during which up to 1,000 patches submitted by the developer community are merged every day into the mainline repository managed by Torvalds. A review process ensures that each patch implements a desirable change. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/securite-pc-et-internet/?&tag=Linux
Via Gust MEES
Ubuntu est une distribution Gnu/Linux maintenue par la communauté Ubuntu et sponsorisée par l'entreprise Canonical Ltd. Son nom, Ubuntu, provient d'un ancien mot bantou qui signifie :
"« Je suis ce que je suis grâce à ce que nous sommes tous »"
Cette distribution, basée sur Debian, est destinée à proposer un système convivial, ergonomique, libre et gratuit y compris pour les entreprises.
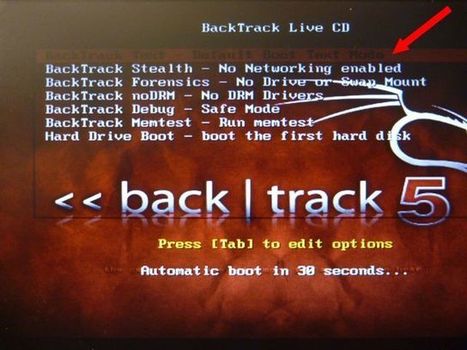
Aujourd’hui, nous vous proposons de découvrir comment cracker un WiFi facilement. Le but de cet article est de démontrer comment il est facile et à la
Via SebTIC
|



 Your new post is loading...
Your new post is loading...
















Since at least May 2021, stealthy Linux malware called AVrecon was used to infect over 70,000 Linux-based small office/home office (SOHO) routers to a botnet designed to steal bandwidth and provide a hidden residential proxy service.
This allows its operators to hide a wide spectrum of malicious activities, from digital advertising fraud to password spraying.
According to Lumen's Black Lotus Labs threat research team, while the AVrecon remote access trojan (RAT) compromised over 70,000 devices, only 40,000 were added to the botnet after gaining persistence.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/securite-pc-et-internet/?&tag=Linux