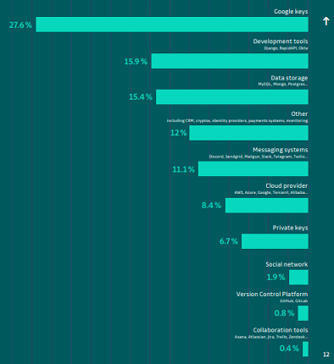
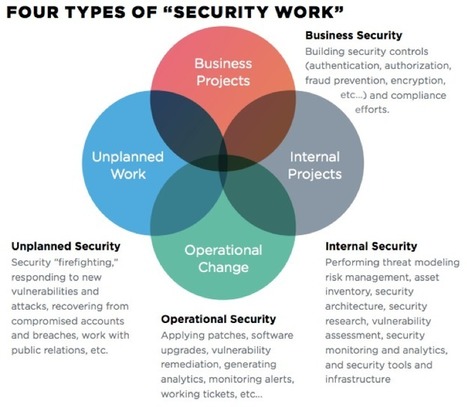
From web threats over IAM principles to auditing and monitoring, learn more about securing serverless architectures in this 2-parter infographic.
Research and publish the best content.
Get Started for FREE
Sign up with Facebook Sign up with X
I don't have a Facebook or a X account
Already have an account: Login
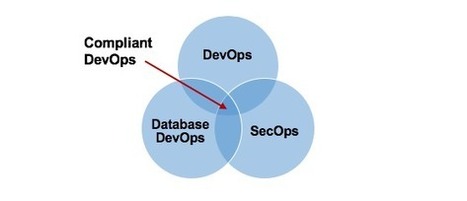
For Product Owners/Product Managers and Scrum Teams: Growth Hacking, Devops, Agile, Lean for IT, Lean Startup, customer centric, software quality...
Curated by
Mickael Ruau
 Your new post is loading... Your new post is loading...
 Your new post is loading... Your new post is loading...
|
|




![Securing Serverless Architectures [Infographics] - DZone Security | Devops for Growth | Scoop.it](https://img.scoop.it/_8kGg-Db4_5OsRDEucaEVTl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)