It’s become almost axiomatic that Apple devices and the apps on them are more secure than the competition. But researchers continue to blow up that notion and today a group of academics have ripped apart the securityprotections in Mac OS X and iOS to show it’s not only possible to create malware and get it onto the App Store, but it’s also feasible to launch “devastating” attacks using rogue software to steal the most sensitive personal data around, from iCloud passwords and Evernote notes to dodgy selfies and more.
The attacks, known as unauthorized cross-app resource access or XARA, expose design flaws that allow a bad app to access critical pieces of data in other apps. As a result, Apple has struggled to fix the issues, according to apaper released today from Indiana University Bloomington, Peking University and the Georgia Institute of Technology.
En savoir plus / Merhr erfahren / Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?tag=XARA



 Your new post is loading...
Your new post is loading...

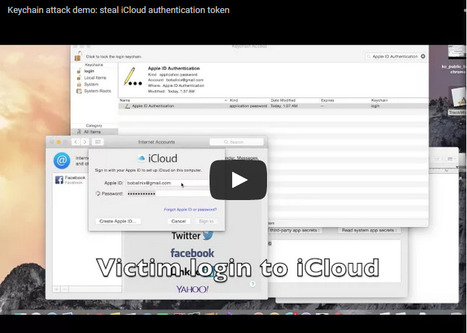


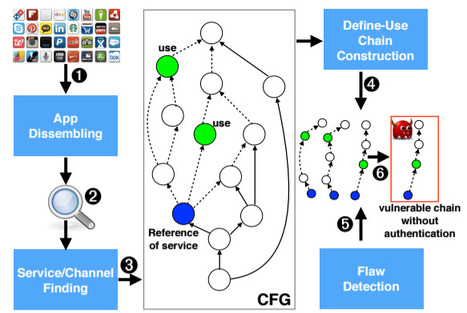





It’s become almost axiomatic that Apple devices and the apps on them are more secure than the competition. But researchers continue to blow up that notion and today a group of academics have ripped apart the securityprotections in Mac OS X and iOS to show it’s not only possible to create malware and get it onto the App Store, but it’s also feasible to launch “devastating” attacks using rogue software to steal the most sensitive personal data around, from iCloud passwords and Evernote notes to dodgy selfies and more.
The attacks, known as unauthorized cross-app resource access or XARA, expose design flaws that allow a bad app to access critical pieces of data in other apps. As a result, Apple has struggled to fix the issues, according to apaper released today from Indiana University Bloomington, Peking University and the Georgia Institute of Technology.
En savoir plus / Merhr erfahren / Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?tag=XARA