 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Bösartige Apps können sich auf iOS-Geräten festbeißen und selbst wenn man sie über den Task-Manager schließt weiter Daten abfischen.
Über eine Ins0mnia getaufte Schwachstelle können Angreifer mit präparierten Apps Apples Vorgaben zum Schließen von Drittanbieter-Anwendungen umgehen und im Hintergrund dauerhaft Informationen abgreifen. Das gelingt auch, wenn Nutzer Apps über den Task-Manager schließen, berichten die Entdecker der Lücke von FireEye. Die Schwachstelle wurde mit der Veröffentlichung von iOS 8.4.1 geschlossen.
Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?tag=Ins0mnia

|
Scooped by
Gust MEES
|
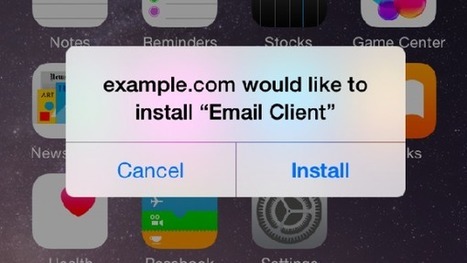
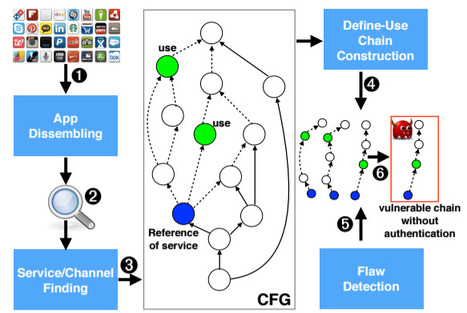
It’s become almost axiomatic that Apple devices and the apps on them are more secure than the competition. But researchers continue to blow up that notion and today a group of academics have ripped apart the securityprotections in Mac OS X and iOS to show it’s not only possible to create malware and get it onto the App Store, but it’s also feasible to launch “devastating” attacks using rogue software to steal the most sensitive personal data around, from iCloud passwords and Evernote notes to dodgy selfies and more.
The attacks, known as unauthorized cross-app resource access or XARA, expose design flaws that allow a bad app to access critical pieces of data in other apps. As a result, Apple has struggled to fix the issues, according to apaper released today from Indiana University Bloomington, Peking University and the Georgia Institute of Technology.
En savoir plus / Merhr erfahren / Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?tag=XARA

|
Scooped by
Gust MEES
|
"Note that all the attack apps were successfully released by the Apple Stores. So, the security threats are indeed realistic."
So, it's a serious problem. And, as yet, not fixed.
The university researchers say that they first reported the vulnerability to Apple on October 15 2014, and contacted them again in November 2014 and early this year. They claimed that Apple told them that because of the complex nature of the security issue, six months' grace would be required to develop a solution.
Unfortunately, that fix has still not emerged and the researchers have chosen to go public with their findings.
For now, until a proper solution is discovered, the most secure approach might be to exercise caution about what apps you download onto your Macs and iOS devices, even if they are listed in the official iOS and Mac App Store — stick with apps from known developers.
Learn more:
.

|
Scooped by
Gust MEES
|
|

|
Scooped by
Gust MEES
|
Après Microsoft qui a publié un Patch Tuesday bien fourni en correctifs critiques, c’est au tour d’Apple de mener un grande vague de mises à jour de sécurité sur plusieurs produits. Les OS de la firme de Cupertino sont bien évidement aux premières loges.
Différentes versions de Mac OS X sont concernées : OS X El Capitan 10.11.2, OS X Yosemite 10.10.5, et Mavericks 10.9.5. Au total, la Security Update 2015-008 corrige 54 vulnérabilités dans des services et des composants tel qu’App Sandbox, Bluetooth, Compression, Configuration Profiles, CoreGraphics, CoreMedia Playback, EFI, File Bookmark, Hypervisor, ImageIO, Intel Graphics Driver, IOAcceleratorFamily, IOHIDFamily, IOKit SCSI, Kernel, Keychain Access, OpenGL, Sandbox, Security, etc. A noter que la moitié des failles découvertes sont critiques, car elles peuvent permettre à des pirates d’exécuter du code arbitraire à distance.
Learn more / Mehr erfahren / En savoir plus :
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?tag=Patch+Tuesday+made+in+Apple
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Apple devices are generally considered by security experts to be safe, and rather difficult to hack. But difficult doesn’t mean impossible.
Over the weekend someone proved just how possible it is to hack at least one of these devices, the iPhone.
The hack came about as part of a challenge issued in September by bug bounty startup Zeriodium, which offered up a million dollar bounty for “an exclusive, browser-based, and untethered jailbreak for the latest Apple iOS 9 operating system and devices” that was set to expire on October 31.
This new hack has implications far exceeding the million dollar bounty.
Learn more:
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?tag=ZERODIUM

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Cybercriminals have reportedly stolen over 225,000 Apple ID account credentials from jailbroken iOS devices, using a type of malware called, “Keyraider”. The criminals have been using the stolen credentials to make in-app purchases with user accounts. Keyraider poses as a downloadable app, but once it’s on the user’s phone, it steals the user’s account login credentials, device GUID (globally unique identifier), Apple push notification service certificates and private keys, and iTunes purchase receipts. These attacks happened mainly in China, but jailbreaking is not exclusive to China. Jailbreaking is practiced by iOS users all over the world.
Jailbreaking your device is a security risk!
This news is a timely reminder about the downside to jailbreaking your Apple iOS device. It sounds like a great idea, in theory, but what many often overlook is that while jailbreaking allows Apple users to bypass many iOS operating system restrictions they might consider burdensome, for example being only able to download apps from the Apple iOS App Store, it also means that cybercriminals have much more freedom to attack the device.
One of the biggest reasons that jailbreaking puts your phone or tablet at risk is that it disables the “sandboxing” feature native in all Apple devices. Sandboxing keeps third party apps out of your operating system, and only allows those apps certain permissions to your information (which these apps “ask” for through pop-ups to be approved by the device user). Because these apps need your explicit permission to look through your photos, access your location, or look up your contacts, it’s highly unlikely that malicious code can get through to do damage or steal your information. Once you remove the sandbox, any app can access all of your private information, including malicious apps posing as legitimate apps.

|
Scooped by
Gust MEES
|
Über die iOS-Sicherheitslücke Ins0mnia können bösartige Apps iPhone-Nutzer ausspionieren. Abhilfe schafft ein Update auf die neue Version 8.4.1 von Apples Betriebssystem.
Lauschangriff auf iPhone-Nutzer: Normalerweise ist es Drittanbieter-Apps unter iOS nicht gestattet, dauerhaft im Hintergrund ausgeführt zu werden. Das Betriebssystem schließt die Anwendungen automatisch nach 3 Minuten, falls diese nicht genutzt werden. Über die Sicherheitslücke Ins0mnia ist es laut Untersuchungen des Sicherheitsanbieters FireEye allerdings möglich, diese Beschränkung zu umgehen.
Dadurch sind bösartige Apps in der Lage, den Nutzer dauerhaft zu tracken und beispielsweise GPS-Standorte weiterzuleiten. Selbst das manuelle Beenden der App über den Task Switcher schafft keine Abhilfe.
Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?tag=Ins0mnia

|
Scooped by
Gust MEES
|
Plusieurs failles de sécurité ont été repérées par des chercheurs universitaires, celles-ci permettant de contourner la sécurité de l’application keychain, des sandbox des programmes ou encore les mesures de sécurité sur l’App Store. La famille Xara Et ce type de failles se retrouve un peu partout : selon les auteurs de l’étude, qui ont testé 200 applications choisies au hasard sur l'App Store, la grande majorité d'entre elles se révèlent vulnérables face à ces failles de sécurité. Si l’exemple de Keychain est le plus parlant, les chercheurs notent que ce type de vulnérabilités peut être utilisé pour accéder à de nombreux services et applications sur iOS et OSX. Au total, les chercheurs estiment que 88,6% des applications proposées sur l’Apple Store seraient vulnérables à ce type d’attaques.
En savoir plus / Merhr erfahren / Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?tag=XARA

|
Scooped by
Gust MEES
|
|Nach Angaben mehrerer Universitätsforscher sind das Sandboxing-System und die Schlüsselbundverwaltung von Apple nicht sicher. So soll es möglich sein, private Daten, Fotos und Passwörter zu klauen.
Forschern mehrerer Universitäten ist es gelungen, Sicherheitsmechanismen in Apple-Produkten zu umgehen. Sie entdeckten mehrere Lücken, über die sie von einer manipulierten App auf andere Anwendungen zugreifen konnten. Eigentlich sollte dies nicht möglich sein. Nach ihren eigenen Aussagen informierten sie Apple über die Lücken. Der Hersteller, der im vergangenen Quartal 13,6 Milliarden Dollar Gewinn machte, forderte sie auf, mindestens sechs Monate zu warten, reagierte dann aber nicht mehr. Deswegen entschieden sie sich, ihre Erkenntnisse in einem Whitepaper (PDF) zu veröffentlichen. . Learn more: . .
|



 Your new post is loading...
Your new post is loading...














Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
http://www.scoop.it/t/securite-pc-et-internet
Good to know..
Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
http://www.scoop.it/t/securite-pc-et-internet