 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|
A new information stealer malware named 'MetaStealer' has appeared in the wild, stealing a wide variety of sensitive information from Intel-based macOS computers.
MetaStealer, not to be confused with the 'META' info-stealer that saw some popularity last year, is a Go-based malware capable of evading Apple's built-in antivirus tech XProtect, targeting business users. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Microsoft has detailed the evolution of a relatively new piece of Mac malware called UpdateAgent that started out stealing system information in late 2020 but has morphed into a tool for delivering adware and potentially other threats.
One of UpdateAgent's newest and most potent features is the ability to bypass Apple's built-in Gatekeeper system that is meant to allow only trusted, signed apps to run on Macs.
Microsoft flagged the malware now as it appears to be under continuous development. Today, it installs an "unusually persistent" adware threat called Adload, but Microsoft cautions it could be used to distribute other more dangerous payloads in future. For example, Microsoft found its makers host additional payloads on Amazon Web Services' S3 and CloudFront services. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Apple hat zum zweiten Mal in diesem Monat eine Sicherheitslücke mit einem Betriebssystem-Patch geschlossen. Welche Geräte betroffen sind und was Apple an regulären Updates in den nächsten Wochen plant. Apple hat eine gefährliche Sicherheitslücke geschlossen, die Angreifer unter den Betriebssystemen iOS und iPadOS in die Lage versetzen konnte, gefährliche Malware auf den mobilen Geräten auszuführen. Wie das Unternehmen mitteilt, sollten Nutzer auf den aktuellen Mobilgeräten dazu umgehend Version 14.4.2 installieren. Nutzer älterer Geräte finden mit iOS 12.5.2 die passenden Patches. Anwender, die iOS 13 verwenden, erhalten dagegen keinen gesonderten Patch mehr und sollten upgraden. Nutzer der Apple Watch schließlich benötigen die Betriebssystemversion 7.3.3. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
MacOS is thought of as more secure than Microsoft’s Windows, but the amount of malware targeting Apple’s operating system is growing. Apple has taken steps to mitigate malware on macOS through a process called notarization—but even this can be bypassed by new and improved adware, a security researcher has discovered.
The adware campaign uses notarized malware, meaning it was scanned and "approved" by Apple and will run on Catalina and Big Sur, security researcher Patrick Wardle has found. “As far as I know, this is the first time hackers have been able to abuse Apple's new notarization,” Wardle told me. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
The Mac vs. PC debate isn't nearly as intense as it was earlier in the 21st century, but a new malware report could stoke the flames a little bit for the first time in years.
Antivirus company Malwarebytes released a big ol' report about the prevalence of different types of malware across different operating systems this week. There's plenty to chew on, but the most eye-catching finding is that, for the first time anyone can remember, Macs are more susceptible to malware than Windows PCs.
Malwarebytes measured the average number of threats detected per endpoint, which basically means "device" in this context. In 2018, Macs only averaged 4.8 threats per endpoint, but that number ballooned to 11 in 2019. Windows devices, by comparison, only saw 5.8 threats per endpoint last year. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Mac

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Before either of those patches rolled out, Mozilla became aware of an attack leveraging both vulnerabilities. At the time, we only knew the attacks had something to do with Coinbase as the initial bug report came from a researcher who works on both Google’s Project Zero and the Coinbase security team. Now, Coinbase’s head of security Philip Martin says the attack was aimed at Coinbase employees and not users. Martin also notes that other exchanges were targeted in the attacks, although none have stepped forward.
Meanwhile, Apple security expert Patrick Wardle published an analysis of malware that appears to have installed itself on a fully updated Mac. The hash provided by Wardle matches one from Martin, and the victim of the attack was involved with a cryptocurrency exchange until very recently. Unfortunately, the malware is novel and avoided Apple’s protection mechanisms, but Wardle believes that Apple will have a patch to change the way macOS scans files downloaded by applications rather than the user. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Browsers

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Un malware qui vise les MAC OS s’invite pour la première fois dans le Top 10 des malwares détectés au 3ème trimestre de l’année 2018
décembre 2018 par WatchGuard® Technologies
WatchGuard® Technologies publie son Rapport sur la Sécurité Internet pour le troisième trimestre 2018. Pour la première fois au cours de ce trimestre, un malware visant spécifiquement les MAC OS a fait partie de la liste des dix malwares les plus couramment détectés par WatchGuard. Le rapport a également révélé que 6,8% des 100 000 sites web générant le plus de trafic dans le monde acceptent toujours des versions obsolètes et non sécurisées du protocole de chiffrement SSL. En outre, WatchGuard a enregistré plus d’attaques de malwares dans la zone Asie-Pacifique que dans toute autre région du monde, indiquant un accroissement significatif du nombre de malwares ciblant cette zone en 2018. Le rapport WatchGuard est basé sur des données récoltées par des dizaines de milliers de boîtiers UTM WatchGuard Firebox actifs à travers le monde, et analyse les campagnes de malware majeures, les attaques réseau et les menaces de sécurité ciblant les PME et les entreprises dites distribuées. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
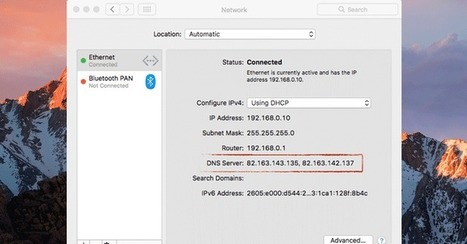
Déjà quatre nouveaux malwares identifiés en 2018 sur Mac
Malwarebytes dévoile en outre que pas moins de quatre nouveaux malwares ont été identifiés depuis le début de l'année 2018. L'un d'entre eux a été identifié par un utilisateur dont les DNS ont été changés à son insu et qui s'est retrouvé dans l'impossibilité de les remettre à zéro : OSX.MaMi. Outre le changement de DNS, le malware avait également installé un nouveau certificat de sécurité.
Un autre malware serait issu des outils développés par le Liban dans le cadre de l'opération d'espionnage d'Etat DarkCaracal. Ce malware ne serait toutefois qu'en phase de développement, la version identifiée étant la 0.1, d'après Malwarebytes. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
US authorities have charged a 28-year-old Ohio man who is alleged to have created and installed creepy spyware on thousands of computers for 13 years.
Phillip R. Durachinsky, of North Royalton, Ohio, is alleged to have used Mac malware known as “Fruitfly” to remotely control victims’ computers, access and upload files, grab screenshots, log keystrokes, and surreptitiously spy via infected computer’s webcams.
Durachinsky, who faces multiple charges including Computer Fraud and Abuse Act violations, Wiretap Act violations, and identify theft, is said to have created a visual interface that allowed him to retrieve live images from several infected computers simultaneously.
In the indictment, Durachinsky is said to have used malware he created between 2003 and January 2017 to steal personal data, tax records, passwords, and “potentially embarrassing communications.”
According to the indictment, Durachinsky used stolen usernames and passwords to hack into his victims’ online accounts and steal further information, keeping detailed notes on his victims. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Fruitfly

|
Scooped by
Gust MEES
|
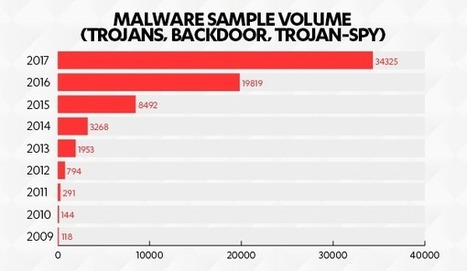
In den ersten drei Quartalen des Jahres 2017 stieg die Zahl der Malware-Angriffe auf Macs um über 70 % und die PUA (potenziell unerwünschte Anwendungen wie z.B. Adware) um 50 % gegenüber dem Vorjahr (Quelle: F-Secure Labs). Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
|

|
Scooped by
Gust MEES
|
Une nouvelle version du malware Dridex cible actuellement les Mac pour se propager sur un grand nombre d'ordinateurs.
Le malware Dridex est déjà connu par les utilisateurs de PC Windows, mais c'est la première fois que ce logiciel malveillant s'attaque à macOS. Pour ce faire, les hackers ont changé le mode de fonctionnement pour parvenir à leurs fins. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Threat actors enlist compromised WordPress websites in campaign targeting macOS users.
Threat actors known as WildPressure have added a macOS malware variant to their latest campaign targeting energy sector businesses, while enlisting compromised WordPress websites to carry out attacks.
Novel malware, initially identified in March 2020 and dubbed Milum, has now been retooled with a PyInstaller bundle containing a trojan dropper compatible with Windows and macOS systems, according to researchers. Compromised endpoints allow the advanced persistent threat (APT) group to download and upload files and executing commands.
On Wednesday, Kaspersky published its latest findings tied to the APT and malware, which it first discovered and reported on in March 2020. At that time, researchers noted WildPressure targeted Middle East organizations with a C++ version of a trojan it called Milum. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
A second malware that targets Macs with Apple’s in-house M1 chip is infecting machines worldwide — but it’s unclear why.
Hard on the heels of a macOS adware being recompiled to target Apple’s new in-house processor, researchers have discovered a brand-new family of malware targeting the platform.
Curiously, in the samples seen so far by analysts at Red Canary, the malware (dubbed Silver Sparrow) has been executing on victim machines with the final payload yet to be determined. It appears to be lying in wait for further instructions, which is worrying because it’s clear that the authors are advanced and sophisticated adversaries, researchers said.
Silver Sparrow has taken flight in any event: As of February 17, this fresh entry to the malware scene had already infected 29,139 macOS endpoints across 153 countries, according to researchers – primarily in Canada, France, Germany, the United Kingdom and the United States. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Xcode projects are being exploited to spread a form of Mac malware specializing in the compromise of Safari and other browsers.
The XCSSET malware family has been found in Xcode projects, "lead[ing] to a rabbit hole of malicious payloads," Trend Micro said on Thursday.
In a paper (.PDF) exploring the wave of attacks, cybersecurity researchers said an "unusual" infection in a developer's project also included the discovery of two zero-day vulnerabilities. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
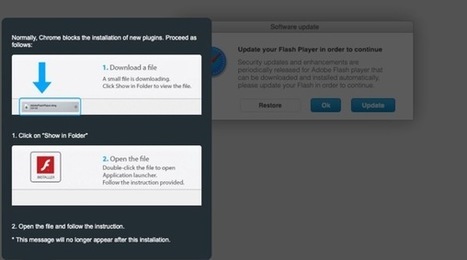
Meet OSX/CrescentCore, the next generation of fake Flash Player malware—now redesigned to evade antivirus detection.
Hot on the heels of Intego's discovery of OSX/Linker and being the first to detect OSX/NewTab, the Intego team has discovered in the wild another previously unknown bit of malware that installs other unwanted software—but only if you're not running third-party endpoint protection software, and only if your operating system isn't running inside a virtual machine.
Intego has observed this malware in multiple places across the Web, from sketchy copyright-infringing download sites to rogue, high-ranking, non-sponsored Google search results links. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Researcher discloses vulnerability in macOS Gatekeeper security feature that allows the execution of malicious code on current version of the OS.
Researcher Filippo Cavallarin disclosed a bug in the macOS security feature Gatekeeper that allows malicious code execution on systems running the most recent version of Mojave (10.14.0).
MacOS Gatekeeper is an Apple security feature that enforces code signing and verifies downloads and apps before users run them. The goal is to eliminate the possibility of malicious files being executed on systems. Gatekeeper requires the user’s consent before opening a file.
“On MacOS X version <= 10.14.5 (at time of writing) it is possible to easily bypass Gatekeeper in order to execute untrusted code without any warning or user’s explicit permission,” wrote Cavallarin, the CEO of Segment, an Italian security firm. Learn more / En savoir plus / Mehr erfahren: http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security https://www.scoop.it/topic/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Gatekeeper

|
Scooped by
Gust MEES
|
Apple users continue to be some of the favorite targets of malvertising campaigns, according to a report published this week by cyber-security firm Confiant.
The report describes a new malvertising group called VeryMal that's been going after Apple users, with the latest campaigns employing steganography techniques to hide malicious code inside ad images to avoid detection.
The Confiant report comes after the company discovered a different malvertising group last year, named ScamClub, which also exclusively targeted Apple users.
But while ScamClub was a much bigger operation, hijacking as many as 300 million web sessions for US-based iOS users, the VeryMal group is a much smaller in size, being blamed for only five million hijacks.
However, the difference, according to researchers, is that this newer group is way sneakier, employing steganography to hide the code responsible for redirecting users from legitimate sites to malicious ones. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Steganography https://www.scoop.it/t/securite-pc-et-internet/?&tag=Steganography

|
Scooped by
Gust MEES
|
Earlier this week, we discovered a new piece of Mac malware that is combining two different open-source tools—the EmPyre backdoor and the XMRig cryptominer—for the purpose of evil.
The malware was being distributed through an application named Adobe Zii. Adobe Zii is software that is designed to aid in the piracy of a variety of Adobe applications. In this case, however, the app was called Adobe Zii, but it was definitely not the real thing.
As can be seen from the above screenshots, the actual Adobe Zii software, on the left, uses the Adobe Creative Cloud logo. (After all, if you’re going to write software to help people steal Adobe software, why not steal the logo, too?) The malware installer, however, uses a generic Automator applet icon. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
A security researcher has revealed details of a new piece of undetectable malware targeting Apple's Mac computers—reportedly first macOS malware of 2018.
Dubbed OSX/MaMi, an unsigned Mach-O 64-bit executable, the malware is somewhat similar to DNSChanger malware that infected millions of computers across the world in 2012.
DNSChanger malware typically changes DNS server settings on infected computers, allowing attackers to route internet traffic through malicious servers and intercept sensitive information.
First appeared on the Malwarebytes forum, a user posted a query regarding unknown malware that infected his friend's computer that silently changed DNS settings on infected macOS to 82.163.143.135 and 82.163.142.137 addresses. Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
New MacOS malware steals bank log-in details and intellectual property.
Security researchers have discovered a new, invasive OSX.Pirrit adware variant targeting Mac OS X that enables cyber-criminals to take full control of a user's Mac computer.
The malware has already infected thousands of Mac computers around the world. According to a blog post by Amit Serper, principal security researcher at Cybereason, while usual adware campaigns enable the attackers to flood a person's computer with ads, this malware not only bombards Macs with adware, it spies on users and runs with the highest user privileges, enabling hackers to leverage this adware to capture personal information on the users, including bank account logins and intellectual property of businesses.
“To my surprise, it's very active. Not only is it still infecting people's Macs, OSX.Pirrit's authors learned from one of their mistakes (They obviously read at least one of our earlier reports),” said Serper.
He added that unlike old versions of OSX.Pirrit that used rogue browser plug-ins or even installed a proxy server on the victim's machine to hijack the browser, this incarnation uses AppleScript, Apple's scripting/automation language.
Learn more / En savoir plus / Mehr erfahren: https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security/?&tag=Malware https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
|



 Your new post is loading...
Your new post is loading...































A new information stealer malware named 'MetaStealer' has appeared in the wild, stealing a wide variety of sensitive information from Intel-based macOS computers.
MetaStealer, not to be confused with the 'META' info-stealer that saw some popularity last year, is a Go-based malware capable of evading Apple's built-in antivirus tech XProtect, targeting business users.
Learn more / En savoir plus / Mehr erfahren:
https://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security