 Your new post is loading...
 Your new post is loading...
An average of 19 vulnerabilities per day were reported in 2014, according to the data from the National Vulnerability Database (NVD). In this article, I look at some of the trends and key findings for 2014 based on the NVD’s database. . #Mac OS X and #Linux had more #vulnerabilities in 2014 than ALL #Windows Versions in sum. .
Not surprisingly at all, web browsers continue to have the most security vulnerabilities because they are a popular gateway to access a server and to spread malware on the clients. Adobe free products and Java are the main challengers but web browsers have continuously topped the table for the last six years. Mozilla Firefox had the most vulnerabilities reported in 2009 and 2012; Google Chrome in 2010 and 2011; Internet Explorer was at the top for the last two years. To keep systems secure, it is critical that they are fully patched. IT admins should focus on (patch them first): - Operating systems (Windows, Linux, OS X)
- Web browsers
- Java
- Adobe free products (Flash Player, Reader, Shockwave Player, AIR).
. Learn more:

|
Scooped by
Gust MEES
|
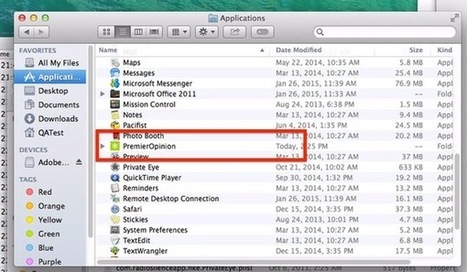
Almost five years ago, Intego security researchers warned about the OSX/OpinionSpy spyware infecting Mac computers, downloaded during the installation of innocent-sounding applications and screensavers distributed via well-known sites such as MacUpdate and VersionTracker.
Once compromised, infected Macs could leak data and open a backdoor for further abuse.
Now, sadly, a variant of OpinionSpy seems to be making something of a comeback.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Woburn, MA – February 10, 2015 - According to the Consumer Security Risk Survey conducted by Kaspersky Lab and B2B International, Apple users responded to have encountered cyber threats almost as often as the users of other platforms. The survey showed that 24 percent of Apple desktop users and 10 percent of Apple laptop users encountered malware during the year*, whereas the number of affected PC owners is slightly higher at 32 percent.
Although security experts have not, thus far, found as much harmful software for OS X as they have for other platforms like Windows, malware does still aim to attack Mac devices. Malware such as ransomware was reportedly faced by 13 percent of Mac users compared to 9 percent of Windows users. There is a similar situation with threats targeting financial data: these incidents were reported by 51 percent of OS X users and 43 percent of Windows users.
In addition the survey results showcased that Mac users are generally less aware of Internet threats than Windows users. For example, 39 percent of MacBook owners have never or hardly heard of ransomware, and 30 percent do not know about dangerous malicious programs that can exploit vulnerabilities in software. By comparison, among all respondents 33 percent know almost nothing about ransomware and 28 percent are unaware of exploits.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Adobe has released Flash Player 16.0.0.305, a new version that fixes the latest zero-day flaw (CVE-2015-0313) that is currently exploited in...

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
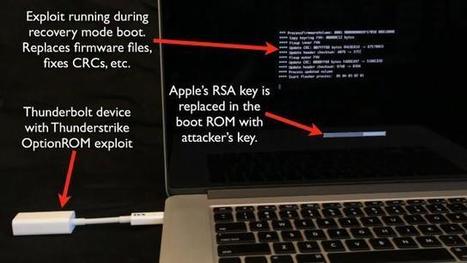
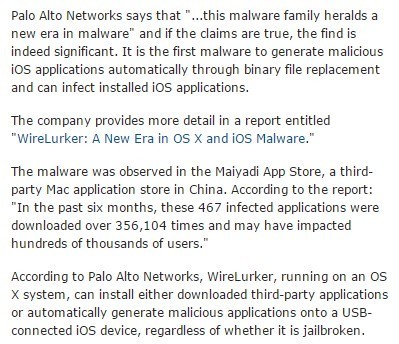
According to Palo Alto Networks, WireLurker, running on an OS X system, can install either downloaded third-party applications or automatically generate malicious applications onto a USB-connected iOS device, regardless of whether it is jailbroken.
The malware is able to install malicious and infected programs on non-jailbroken iOS devices, according to the report, by using enterprise provisioning techniques, thus appearing to be an in-house application. The user is presented with a confirmation dialog box such as the one shown below, but otherwise the application will behave the same as an uninfected one.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security?q=wirelurker

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
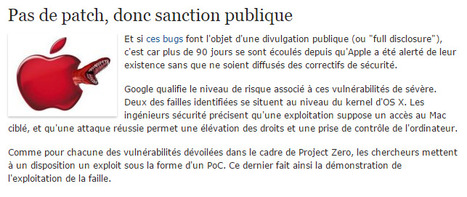
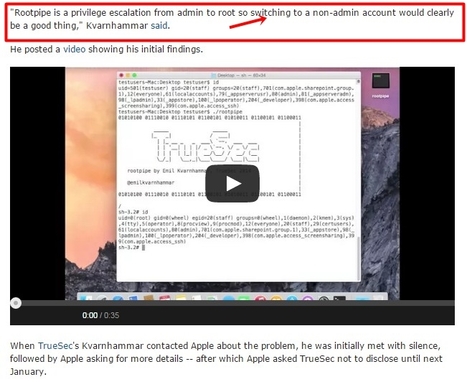
Details are finally emerging about a serious vulnerability in Apple's OS X Yosemite, called "Rootpipe" which allows root access by attackers.
The privilege escalation vulnerability was discovered by Swedish hacker Emil Kvarnhammar, who has been asked by Apple to withhold details until January 2015 -- since Apple likely wouldn't allow details until they have a fix, this is probably when users can expect a patch.
Rootpipe is a privilege escalation from admin to root so switching to a non-admin account would clearly be a good thing," Kvarnhammar said.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
|

|
Scooped by
Gust MEES
|
Five months on from the release of iOS 8, and following six rounds of bugfixes, Apple's flagship mobile platform that powers almost three out of four iPhone and iPads is still riddled with bugs.
I'm just going to come out and say it - this is a mess. If we were talking about cosmetic stuff like a badly laid out user interface or poor selection of wallpapers then I could overlook the issues, but they aren't. These are bugs relating to core systems such as Wi-Fi, cellular connectivity, Bluetooth, and stability and performance.
These are show-stopping bugs. These are bugs that quite frankly should have been sorted before iOS 8 was released, and definitely should have been pinned down after the first couple of updates.
But they aren't.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|
Major cyber security incidents continue to hit the headlines. Security and privacy are top concerns for IT and security professionals, especially after 2014’s highly publicized data breaches.
Companies around the globe were victim to malware, stolen data and exploited vulnerabilities. Big companies weren’t immune to this, with Target, JPMogan Chase, Home Depot and Sony Pictures suffering the painful sting of data breaches. Even celebrities were targeted, with compromised iCloud accounts.
It really isn’t surprising that almost everyone anticipates the need to prepare for security challenges in the coming months. According to a recent survey by Tech Pro Research, 84 percent of IT professionals are more concerned about security and privacy in 2015.

|
Scooped by
Gust MEES
|
Apple is pushing out a mandatory update for Adobe Flash in the wake of the recent disclosure of three zero-day vulnerabilities that are actively being exploited in the wild.
Mac OS X will find that Flash has been disabled on their devices and will see popup messages urging them to install the latest updates if they want to continue to use the software.
“If you’re using an out-of-date version of the Adobe Flash Player plug-in, you may see the message ‘Blocked plug-in’, ‘Flash Security Alert’ or ‘Flash out-of-date’ when attempting to view Flash content in Safari. To continue viewing Flash content, update to a later version of Adobe Flash Player. Click the Download Flash button. Safari opens the Adobe Flash Player page on the Adobe website,” the advisory from Apple stated.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
They also discovered malware samples uploaded to a public cloud storage service of Baidu by a user a month before the apps were made available on the Mayaidi app store, and they have reason to "suspect that Maiyadi has a close relationship with the creator of WireLurker."
"This should also be a wake-up call for Apple users and the way they think about security," commented Kaspersky Lab's Stefan Tanase. "Just like Mac OS X malware quickly evolved from being just a myth to becoming a sad reality, we are seeing iOS being targeted more and more often lately - with nobody being able to offer protection for this platform. Anti-malware vendors are still not allowed to develop protection for iPhone users."
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security?q=wirelurker

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
A Swedish researcher has unearthed a serious bug that affects the newest version of OS X - version 10.10, or Yosemite - and which could allow attackers to gain complete control of the target's Mac machine.
It's a privilege escalation bug he dubbed Rootpipe, but declined to explain why, as the explanation could reveal details that would help attackers find it and create an exploit.
The existence of the flaw has been indirectly confirmed by Apple when they asked the researcher to delay publishing details about it until January 2015, after a fix for the bug is released and pushed out to users
Rootpipe is a privilege escalation from admin to root so switching to a non-admin account would clearly be a good thing," Kvarnhammar said.
Learn more:
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security?q=Rootpipe
|



 Your new post is loading...
Your new post is loading...

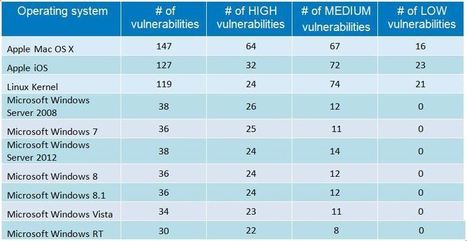



















An average of 19 vulnerabilities per day were reported in 2014, according to the data from the National Vulnerability Database (NVD). In this article, I look at some of the trends and key findings for 2014 based on the NVD’s database.
.
#Mac OS X and #Linux had more #vulnerabilities in 2014 than ALL #Windows Versions in sum.
.
Not surprisingly at all, web browsers continue to have the most security vulnerabilities because they are a popular gateway to access a server and to spread malware on the clients. Adobe free products and Java are the main challengers but web browsers have continuously topped the table for the last six years. Mozilla Firefox had the most vulnerabilities reported in 2009 and 2012; Google Chrome in 2010 and 2011; Internet Explorer was at the top for the last two years.
To keep systems secure, it is critical that they are fully patched.IT admins should focus on (patch them first):